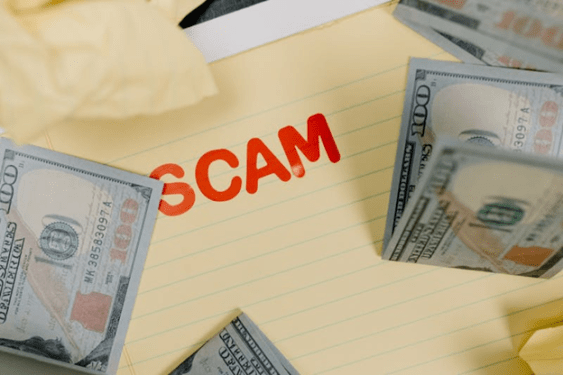
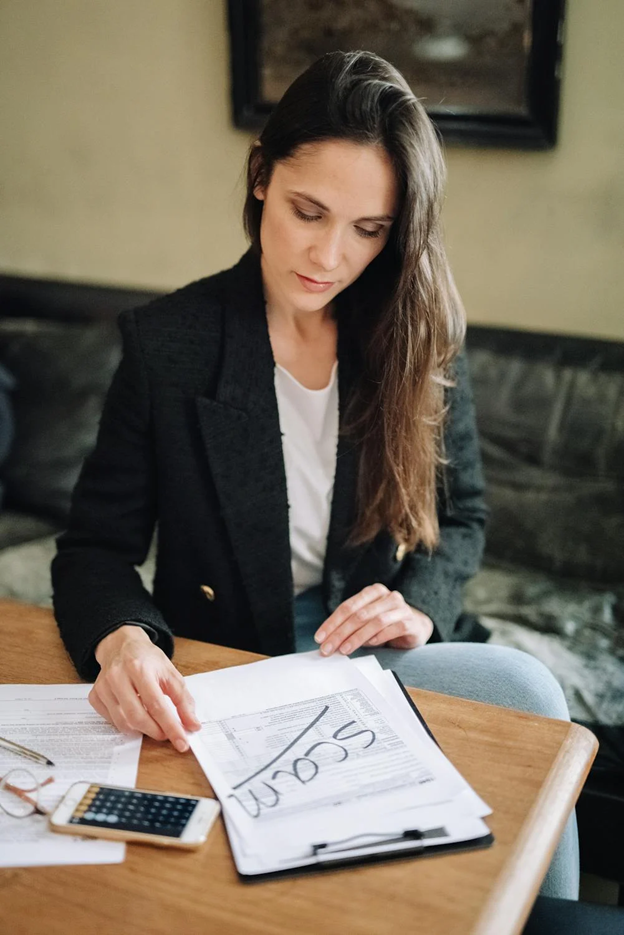
Have you ever felt unsure about an email, text, and phone call asking for personal details or money? Scams are all around us these days – from fraudulent emails trying to steal login credentials and bank details to sophisticated phone calls pretending to be from tech support or government agencies.
In 2020 alone, American consumers lost over $3.3 billion to internet fraud as reported by the FBI Internet Crime Complaint Center. The disturbing reality is that anyone can fall prey to a cyber scam if we are not cautious.
We work, shop, socialize and manage our finances virtually each day without giving it much thought. However, this hyper-connectivity comes with risks – one of the major dangers lurking in cyberspace are online scams. We will discuss what scam is and everything you must know here!
What is Scam?
A scam refers to any deceptive activity aimed at obtaining money or valuable assets from individuals through fraudulent means. Spam, on the other hand, involves the mass distribution of unsolicited messages via email, instant messaging, or other digital platforms, often favored by advertisers due to its low operating costs.
Scammers, the individuals behind scams, employ various tactics such as unwanted phone calls and misleading pop-up ads to deceive unsuspecting individuals.
They may impersonate officials from reputable computer or software companies and employ techniques like requesting remote access to victims’ computers to steal sensitive information or sell unnecessary products or services. While some scammers are easily identifiable, others may be more sophisticated and harder to detect. The primary objectives of scammers include:
- Obtaining personal information.
- Persuading individuals to accept dubious offers without seeking advice.
- Convincing them to send money based on false promises.
- Enticing them to make purchases without proper inspection.
Common Types of Scams
Fraud and scams come in various forms and can target individuals through different means. Being aware of the common types of fraud and scams can aid you recognize warning signs and take necessary precautions to protect yourself, your loved ones, and your finances. Here’s a detailed overview of some prevalent scams and fraud schemes:
1) Charity Scams:
- Charity scams involve thieves posing as legitimate charitable organizations or creating fake charities to solicit money from unsuspecting individuals.
- These scams often increase during holidays or natural disasters, where scammers exploit people’s generosity.
- To avoid falling victim to charity scams, always verify the legality of a charity by researching its details, such as address and phone number, and confirming its authenticity through trusted sources.
2) Debt Collection Scams:
- Scammers posing as debt collectors may attempt to coerce individuals into paying nonexistent debts or debts that have already been settled.
- It’s crucial not to provide any personal or financial details until you can verify the legitimacy of the debt. Requesting more information or using sample letters to seek validation can help prevent falling victim to such scams.
3) Debt Settlement and Relief Scams:
- Debt settlement or relief companies may promise to renegotiate or settle debts but often engage in deceptive practices that can leave individuals in further financial distress.
- Beware of companies that guarantee debt settlement and charge upfront fees. Instead, seek assistance from nonprofit credit counseling programs for reliable debt management options.
4) FDIC Logo Misuse:
- Scammers may misuse the FDIC logo or falsely claim FDIC insurance to gain individuals’ trust and falsely assure the safety of their money.
- Always verify the authenticity of FDIC-insured banks through official channels to ensure the safety of your deposits.
5) Foreclosure Relief or Mortgage Loan Modification Scams:
- Fraudulent schemes promising foreclosure relief or mortgage loan modifications may exploit homeowners’ vulnerabilities by making false promises to save them from foreclosure.
- Seek assistance from HUD-approved housing counseling agencies to explore legitimate options and avoid becoming a victim of foreclosure relief scams.
6) Grandparent Scams:
- Grandparent scams involve scammers impersonating relatives in distress, such as grandchildren, and requesting money or gift cards to help them out of supposed trouble.
- Be cautious of unsolicited requests for financial assistance and cross check the identity of the caller before giving any funds.
7) Imposter Scams:
- Imposter scams involve scammers posing as trusted individuals or organizations, such as government officials or charities, to deceive victims into sending money.
- Always verify the authenticity of the caller or organization independently to avoid falling for imposter scams.
8) Mail Fraud:
- Mail fraud schemes lure individuals with false promises of valuable rewards or prizes in exchange for upfront payments or personal information.
- Recognize warning signs, such as requests for immediate payments or personal information, and report suspected mail fraud to the appropriate authorities.
9) Money Mule Scams:
- Money mule scams involve individuals unwittingly assisting fraudsters by receiving and transferring funds obtained through fraudulent means.
- Avoid involvement in suspicious financial transactions and be cautious of offers promising easy money or employment opportunities.
10) Money Transfer or Mobile Payment Services Fraud:
- Con artists exploit money transfers and mobile payment services to defraud individuals by tricking them into sending money or merchandise without receiving the promised benefits.
- Only use trusted payment methods and avoid sending money to unfamiliar individuals or businesses to prevent falling victim to fraudulent schemes.
11) Mortgage Closing Scams:
- Scammers target homebuyers nearing mortgage closing dates by posing as real estate or settlement agents to steal their closing funds.
- Take precautions, such as verifying payment instructions directly with trusted individuals, to safeguard against mortgage closing scams.
12) Lottery or Prize Scams:
- Lottery or prize scams involve scammers falsely claiming that individuals have won prizes or lottery winnings, requiring upfront payments or personal information.
- Exercise caution when contacted about unexpected winnings and avoid providing sensitive information or making payments to unknown parties.
13) Romance Scams:
- Romance scams exploit individuals’ emotions by deceiving them into forming romantic connections online, ultimately seeking financial gains.
- Stay vigilant and avoid sharing personal or financial information with unfamiliar online acquaintances to protect against romance scams.
By familiarizing yourself with these common types of fraud and scams, you can enhance your awareness and resilience against deceptive practices, ultimately safeguarding yourself and your finances from potential harm.
How to Identify a Scam?
Here is how you can spot scams:
- Insistence on Full Payment and No Negotiation: Scammers often push for full payment without allowing any negotiation and may even demand that you cover shipping costs upfront.
- Refusal to Allow Property Inspection: When dealing with rental properties, if the landlord refuses to let you inspect the property, it could be a red flag for a scam.
- Excuses and Pressure Tactics: Scammers may use various excuses and pressure tactics to coerce you into making quick payments, such as claiming that the deal is off unless immediate payment is made, citing personal emergencies like a family member’s death, or threatening legal consequences if payment isn’t sent promptly.
- Request for Payment in Gift Cards: Beware of requests to make payments using gift cards, as scammers often prefer this method to avoid traceability.
- Claim of Unavailability: Scammers may claim to be out of town or unavailable to meet in person, making excuses to delay face-to-face interactions.
- Lack of Company Information: If the seller or service provider doesn’t have a visible online presence, lacks company details, or uses a name similar to well-known brands, it could indicate a scam.
- Solicitation of Banking ID Details: Be cautious if asked to provide sensitive banking information for payment, especially if the transaction does not involve secure online payment methods.
- Inaccessible Contact Information: Scammers may avoid answering phone calls or providing consistent contact information, making it challenging to reach them.
- Overly Friendly Behavior: Scammers may feign affection or respect to build trust, but it’s often a tactic to manipulate victims emotionally.
- Elusiveness and Changing Contact Details: Be wary if the scammer constantly changes phone numbers or online profiles, making it difficult to track them down.
How to Keep Yourself Safe from Scams Using Cybersecurity
Here are tips to keep yourself safe from scams:
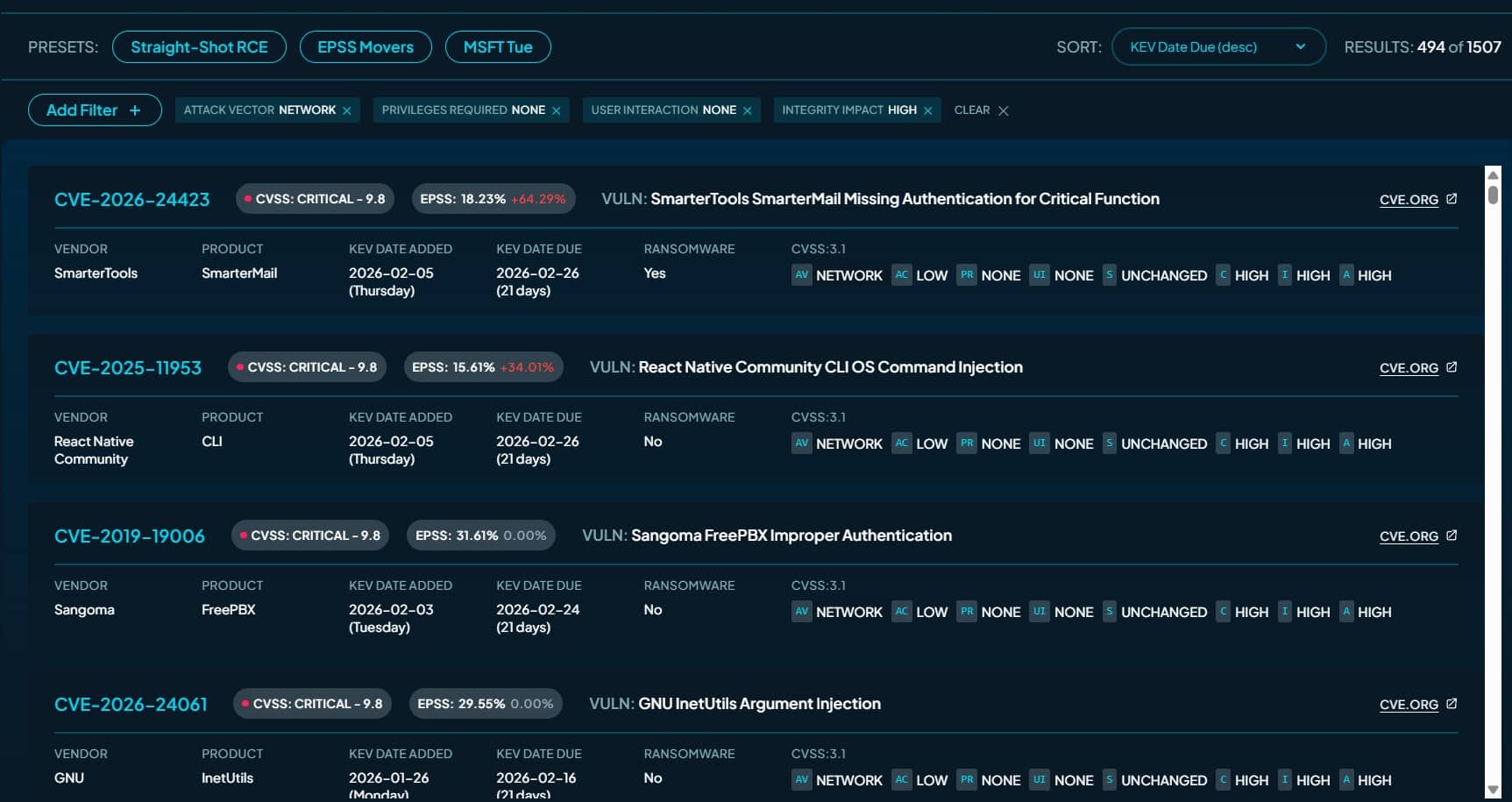
- Keep Software Updated: Please ensure that the operating system, antivirus softwares, web browsers, and other applications are updated with the latest security patches. This helps protect against known vulnerabilities exploited by scammers.
- Use Strong Passwords: Develop complex passwords for your online accounts, comprising a mix of letters, numbers, and special characters. Avoid using easily guessable passwords and refrain from sharing them with others.
- Enable Two-Factor Authentication (2FA): Enable 2FA whenever possible to involve an extra layer of security to your accounts. This requires a second form of verification, like as a code sent to your mobile or email, to access your account.
- Be Cautious Suspicious Emails: Be cautious when clicking on emails from unknown senders or clicking on links and attachments. Look out for spelling errors, grammatical mistakes, and suspicious requests for personal or financial information.
- Verify Website Security: Before entering the sensitive information on a website, please ensure that it is secure by checking for “https://” and a padlock symbol in the address bar. Avoid entering personal details on unsecured websites.
- Educate Yourself: Stay informed regarding common types of scams and cyber threats prevalent online. Educate yourself about phishing, malware, ransomware, and other tactics used by scammers to deceive individuals.
- Use Secure Wi-Fi Networks: Avoid connecting to public Wi-Fi networks for sensitive activities like online banking or shopping. Instead, use a secure, password-protected network or a virtual private network (VPN) for added security.
- Protect Personal Information: Be cautious regarding sharing personal information online, especially on social media platforms. Avoid oversharing details that could be used by scammers to impersonate you or steal your identity.
- Install Security Software: Install trusted antivirus and anti-malware software on your devices to identify and remove malicious threats. Regularly scan your system for viruses & malware to ensure it remains protected.
Internet Rules To be Followed
Here are internet rules you need to be followed:
1) Practice Respect:
- Respect Diversity: Acknowledge and appreciate the diverse backgrounds, experiences, and cultures of individuals you interact with online.
- Respect Privacy: Safeguard the privacy of others by refraining from sharing personal information, images, or files without their explicit consent.
2) Uphold Ethical Standards:
- Avoid Copyright Infringement: Refrain from using copyrighted content without proper authorization, respecting the intellectual property rights of creators and owners.
- Share Knowledge Responsibly: Share information and knowledge online, ensuring accuracy and clarity. Avoid duplicating existing content and contribute positively to the digital community.
3) Exercise Responsibility:
- Combat Cyber Bullying: Take a stand against cyberbullying, recognizing its harmful impact on victims. Refrain from engaging in or promoting online harassment, and be mindful of the consequences of digital actions.
- Ignore Trolls: Resist the urge to engage with internet trolls seeking to provoke or disrupt. Disengage from troll behavior by refusing to respond, thereby denying them the attention they seek.
Wrapping Up!
Scam is a malicious act that targets individuals and organizations by using fraudulent means to obtain personal information or money. With the extensive use of technology in our day to day life, scams have become more prevalent and sophisticated, making it even more important for us to stay vigilant and save ourselves from potential threats.
This is where cybersecurity plays a crucial role in safeguarding our personal and sensitive information.
By understanding the common types of scams and following good cybersecurity practices such as regularly updating your software, creating strong passwords, and being cautious of suspicious emails or websites, you can greatly lessen your risk of being victim to a scam.
It is also important to be aware of any red flags or warning indications that may indicate a potential scam and to always trust your gut feelings when sharing the personal information or making financial transactions.
Key Highlights
- Scams encompass fraudulent activities aimed at deceiving individuals to obtain money, sensitive information, or valuables through deceitful means.
- Common scams include phishing, fake charity appeals, lottery scams, and romance scams, among others.
- Utilize cybersecurity tools such as antivirus software, firewalls, and secure browsing practices to safeguard your devices and personal information.
- Stay informed about common scam tactics and practice vigilance while interacting online to mitigate the risk of falling victim to scams.
FAQ’s
What is a scam?
A scam is any fraudulent activity or deceptive technique aimed at obtaining money, sensitive information, or other valuable assets from individuals through deceitful means.
How can I identify a scam?
- Look out for unsolicited requests for personal information or payments.
- Be cautious of offers that seem too good to be true.
- Verify the legitimacy of organizations or individuals before providing any sensitive information or making transactions.
What are common types of scams?
Common scams include phishing emails, fake charity appeals, lottery or prize scams, and romance scams, among others. Scammers often use various tactics to manipulate individuals into providing money or personal details.
How can cybersecurity help protect against scams?
Cybersecurity measures, like antivirus software, firewalls, and secure browsing practices, can help safeguard your devices and personal information from online threats. Additionally, staying informed about common scam tactics and practicing vigilance while interacting online are essential for staying safe from scams.