Three Apple vulnerabilities — patches issued last week — are being exploited in the wild, CISA warned.
Three zero-day vulnerabilities reported to Apple last week were added to CISA’s Known Exploited Vulnerabilities (KEV) catalog.
It is not clear whether the zero-day vulnerabilities caused damage to the systems. However, Apple did indicate in its reports that they may have been exploited. The three Apple vulnerabilities must be patched immediately to prevent cyber attacks.
Did you patch these three Apple vulnerabilities yet?
The three Apple zero-day vulnerabilities were reported last week. Security updates for affected versions of Apple namely iOS, iPadOS, macOS, tvOS, and watchOS were released.
These can be triggered by WebKit, which is the browser engine for Safari, Mail, and App Store, among others.
The three Apple vulnerabilities were CVE-2023-32373, CVE-2023-32409, and CVE-2023-28204. These are the details of the zero days with predicted damage to unpatched systems.
- CVE-2023-32373 can allow hackers to execute arbitrary code. Apple made changes to the impacted software for improved memory management.
- CVE-2023-32409 was a sandbox escape vulnerability that would also allow arbitrary code execution. It was alerted to Apple by researchers from Google’s Threat Analysis Group and Amnesty International’s Security Lab.
- CVE-2023-28204 was an out-of-bounds read vulnerability that would give access to sensitive data on unpatched devices. “Apple is aware of a report that this issue may have been actively exploited,” Apple posted in its advisory.
The Rapid Security Updates for these three Apple vulnerabilities
To update the software, one may enable Apple’s new feature, Rapid Security updates.
It allows Apple to release automatic updates on the device. This feature specifically allows updates pertaining to immediate security issues that were found by the company.
It can be enabled through the following steps –
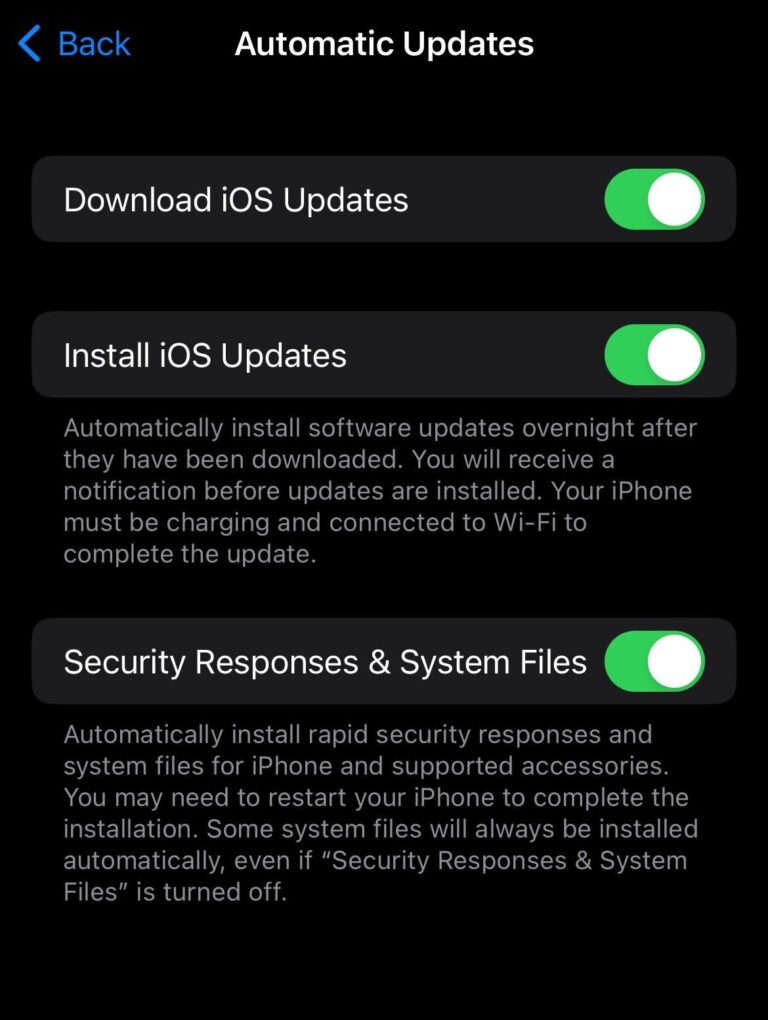
- Settings
- General
- Software Update
- Automatic Updates
Zero-day exploits and the three Apple vulnerabilities
A zero-day is a flaw in software, hardware, or firmware that leave developers clueless in the wake of an exploitation of the said vulnerability. There is no patch because the engineers were not aware of the vulnerability.
Hence, hackers look for zero-day vulnerabilities such as the three Apple vulnerabilities to gain access to systems and hack system data to further leverage it for extortion. Zero-day exploit is the technique used by hackers to run malicious code in vulnerable software.
A zero-day attack is when hackers have already exploited the vulnerability in software. Hence, before hackers reach a vulnerability, developers, and companies look for them and reward researchers in bug bounty programs.
According to a report, 95% of cyber attacks targeted unpatched vulnerabilities. Moreover, it was found that 30% of businesses lack a formal patch management system that formally looks for and releases patches for bugs.
Most exploited vulnerabilities
Companies often release patches upon being notified of zero-day vulnerabilities which users must install without fail.
The following is a list of the 10 most exploited vulnerabilities:
- Atlassian Confluence RCE (CVE-2022-26134)
- Follina (CVE-2022-30190)
- Google Chrome Zero-Day (CVE-2022-0609)
- ICMAD (CVE-2022-22536)
- Log4Shell (CVE-2021-44228)
- PetitPotam (CVE-2021-36942)
- ProxyLogon (CVE-2021-26855)
- Spring4Shell (CVE-2022-22965)
- VMware vSphere (CVE-2021-21972)
- ZeroLogon (CVE-2020-1472)
The average time to detect a breach is 201 days. A Microsoft study found that 80% of cyberattacks could have been detected and prevented with timely software updates and patch releases.
The global patch management market is also predicted to grow by 12% from 2020 to 2025.
The largest market for patch management was North America, according to reports followed by Europe and Asia-Pacific. Microsoft, Oracle, IBM, CA technologies, and HPE are among the top players with the highest patch management market.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.





















































