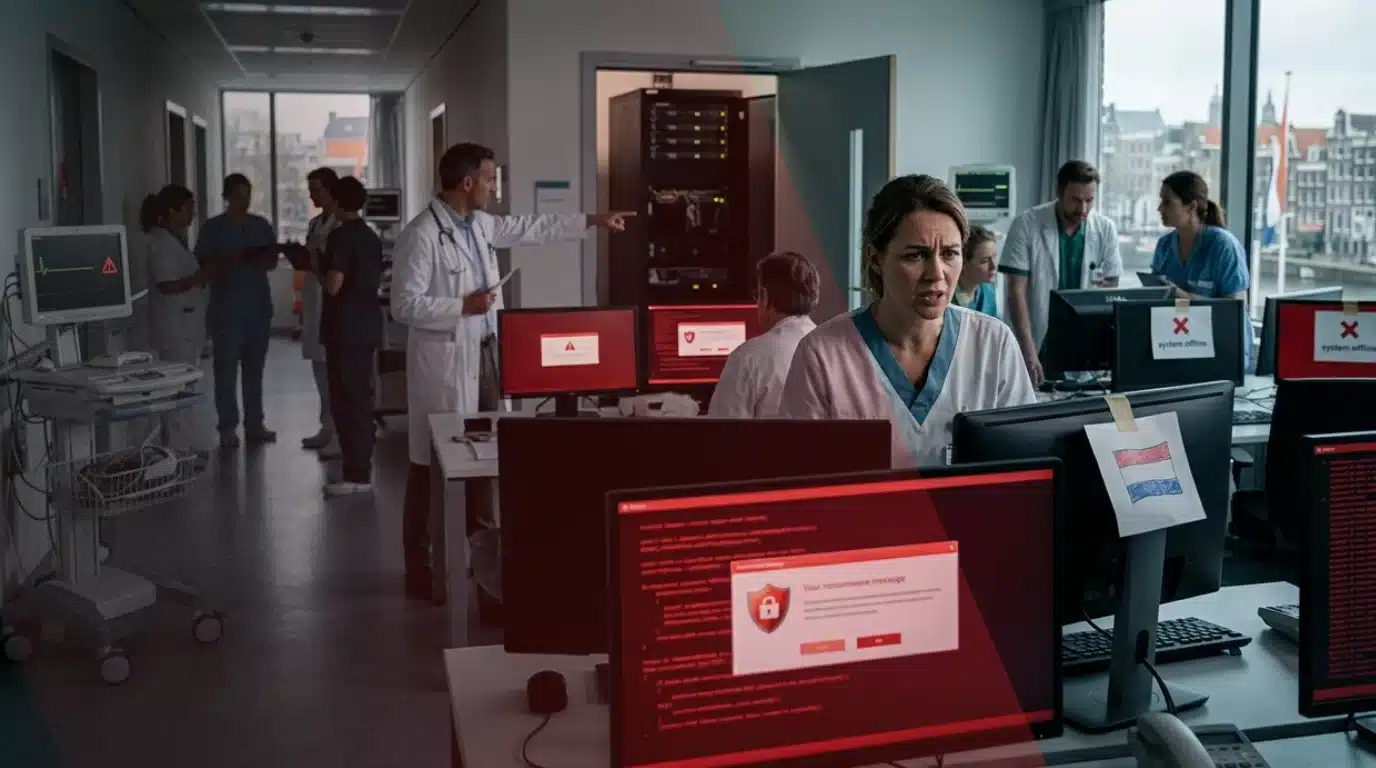
A powerful cyberattack paralyzed Ukraine’s state railway service’s online ticketing system, causing long queues at stations on Monday. Ukrainian officials have hinted that Ukraine railway cyberattack may be another attempt by Russia to “destabilize” the country during ongoing wartime challenges.
Ukraine’s railway system plays an important role in civilian and freight transportation across the country. Since Russia’s full-scale invasion in 2022, air travel has been largely grounded due to frequent missile and drone strikes. This has made railways an essential mode of transport, both for domestic and international passengers and for the delivery of military supplies.
The cyberattack on Ukraine railway was first reported on Sunday when Ukrainian Railways (Ukrzaliznytsia) informed passengers of a failure in its IT system, advising them to purchase tickets on-site or onboard trains. The railway company described the attack as “very systemic, unusual, and multi-level” in a post on Telegram.
Ukraine Railway Cyberattack: Public Announcement and Response
On March 23, 2025, Ukrzaliznytsia provided an update via X, formerly known as Twitter, stating:
“We apologize for the inconvenience and are strengthening morning shifts of ticket offices at the stations with additional employees. You are always welcome to purchase tickets for international routes there. Due to an IT failure, online services are temporarily not working.”

Despite efforts to restore systems, the attack continued. A follow-up statement on March 24 confirmed that the cyberattack was ongoing:
“Our system is still under a massive cyberattack of the enemy. Nevertheless, our trains are running in accordance with the schedule. Our ticket offices are prioritizing passengers who are willing to either depart or arrive in the next few days. We will keep you posted.”

While officials have reassured the public that train operations remain unaffected, work continues to restore the online ticketing service, which has been down for over 24 hours since the initial breach.
Blame Pointed at Russia
Although Ukrzaliznytsia did not explicitly name Russia, Ukrainian officials have strongly hinted at Russian involvement. Anton Gerashchenko, a former advisor to Ukraine’s Internal Affairs Minister, posted on X:
“Online systems of Ukrainian Railways (Ukrzaliznytsia) have been subjected to a large-scale cyberattack, possibly a Russian one. The company’s employees, together with the Security Service of Ukraine Cyber Department, have been restoring the systems for two days.
Gerashchenko emphasized that, despite the attack, train operations remain stable:
“The enemy has not succeeded in its key goal: train traffic is stable, running smoothly without delays, and all operational processes are in place in a backup format. The railroad continues to move despite physical attacks on infrastructure, and even the most vile cyberattacks cannot stop it.”
A senior Ukrainian government source, speaking on condition of anonymity, described the attack as a “strong strike but not critical,” adding that it appeared designed to “destabilize” the country and exert psychological pressure on citizens.
Impact of Cyberattack on Ukraine Railway on Passengers and Railway Services
As a result of the cyberattack, Kyiv’s central train station saw long queues on Monday morning, with passengers scrambling to purchase tickets. Currently, booking offices are only offering tickets for travel until Tuesday.
Passengers who bought their tickets online before the cyberattack but are now unable to access them have been advised to present the PDF copy sent to their email or arrive at the station 20 minutes before departure to explain their situation to officials. Ukrzaliznytsia has also urged passengers who are scheduled to travel tomorrow to refrain from crowding ticket offices today, allowing staff to assist those with imminent travel plans.

Railway’s Role in Wartime Ukraine
Ukraine’s railways have been a crucial transportation network since the war began. Trains serve not only as a means of evacuating civilians but also as a key route for delivering weapons and military supplies. In 2024 alone, the system transported approximately 20 million passengers and 148 million tonnes of freight, according to Deputy Prime Minister Oleksiy Kuleba.
Oleksandr Pertsovskyi, chairman of Ukrzaliznytsia’s board, praised the railway company’s quick response to the cyberattack in a televised statement:
“Operational traffic did not stop for a single moment. The enemy attack was aimed at stopping trains, but we quickly switched to backup systems.”
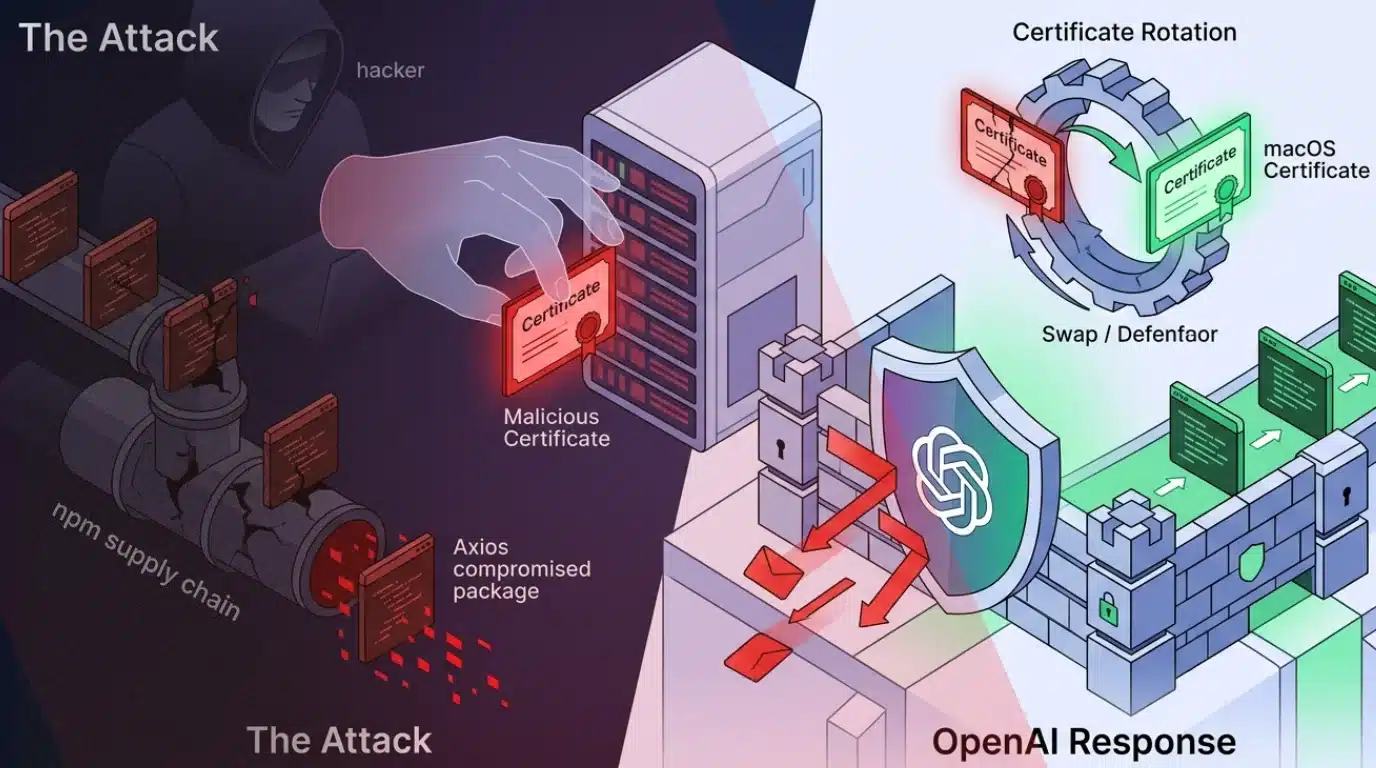
A Pattern of Cyberattack on Ukraine
This is not the first cyberattack on Ukrzaliznytsia. Ukraine’s critical infrastructure has been repeatedly targeted by cyber threats since the onset of the war. Cyberattacks have become a key tool in modern warfare, with Russia allegedly using them to disrupt vital services, weaken public morale, and destabilize government operations.
While the cyberattack on Ukrzaliznytsia has caused inconvenience to passengers and forced the system to operate offline, the railway company’s strong backup measures have ensured that operations remain largely unaffected.
Ukrainian authorities are working to restore online ticketing services while ensuring smooth rail operations. In the meantime, passengers are encouraged to remain patient and follow official instructions regarding ticket purchases and travel arrangements.