Lockbit 3.0 ransomware gang has added one of the biggest development partners of popular automotive manufacturers such as BMW, Audi, Daimler, Tesla, VW and, Porsche, EDS Automotive GmbH, to its list of victims, putting many consumers at risk. In October last year, data of nearly 300,000 customers were exposed in the Toyota data breach.
In 2022, Lockbit gained exponential feats and successfully brought big corporations to their knees. Clearly, the hacker collective plans to continue the trend in 2023. According to recent reports, Lockbit has slowly become one of the most controversial hacking groups in the space, going as far as lecturing companies on how to negotiate ransoms.
The company, which started as a family project in 1989, basically around automotive CAD development, later became the official parts supplier of BMW, development services for Tesla, official supplier of Volkswagen Group, and many more, distinguished above all by many years of experience and a broad spectrum of competence.
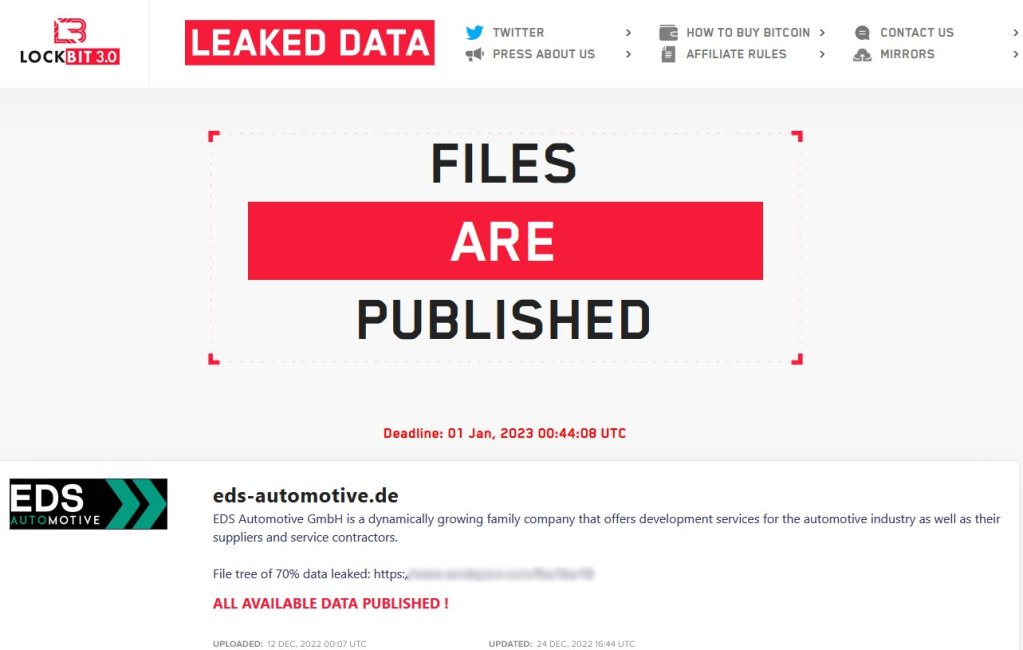
Lockbit 3.0 attacks development partner EDS Automotive GmbH
According to a post shared by the threat actor, the company’s data has been published, including crucial information, such as agreements, invoices, account statements, contracts, and other important data.
Over the years, hacks have shifted a large portion of focus from computers to cars, given that electronics have become the new normal for vehicles. One of the reasons why hackers go after car manufacturers is to steal sensitive information, such as proprietary designs, trade secrets and more.
Hackers may also be motivated by the desire to disrupt the company’s operation or gain access to the supply chain to insert malicious software or hardware into the products being produced.
In some cases, hackers may target car manufacturers to extort money through sophisticated ransomware attacks. Additionally, some hackers may be motivated to prove a point or raise awareness about security vulnerabilities in connected devices.
Toyota Data Breach
In a similar incident, a data breach at the Indian subsidiary of Toyota, Toyota Kirloskar Motor may have exposed customers’ data to unauthorized parties. Toyota India has been facing the attack and notified the authorities, who are currently mitigating the issue.
Toyota Kirloskar Motor (TKM) has been notified by one of its service providers of an incident that might have exposed the personal information of some of TKM’s customers on the internet,” TKM stated in a statement without disclosing the number of clients affected was not disclosed.
How can hackers gain access to your car?
Cyberattacks on cars are a growing concern as more and more vehicles become connected to the internet. These types of attacks can range from hackers gaining access to a car’s onboard computer systems to physically taking control of a vehicle. There are several ways that hackers may attempt to gain unauthorized access to a car’s systems.
- One way is by exploiting vulnerabilities in the car’s wireless communication systems, such as Bluetooth or the cellular network.
- Hackers may also try to gain physical access to the car’s onboard diagnostics (OBD) port, a standardized interface that provides access to the car’s diagnostic and tracking systems.
- In some cases, hackers may try to gain access to the car’s systems by infecting it with malware through other means, such as a USB drive or an infected website.