Stanford University announced that it was investigating a cybersecurity incident after claims about an attack surfaced online. Akira ransomware group claimed the Stanford University cyberattack on October 27, 2023, on its dark web portal.
Following this, the leading research university posted a statement confirming the Stanford University cyberattack impacting its Department of Public Safety.
The statement by the university addressing the Stanford University cyberattack read, “We are continuing to investigate a cybersecurity incident at the Stanford University Department of Public Safety (SUDPS) to determine the extent of what may have been impacted.”
Stanford University Cyberattack
The statement concerning the SUDPS cyberattack read that the investigation conducted till the point of posting the same established that there were no signs of the SUDPS cyberattack impacting any other part of the university.
Confirming the Stanford University cyberattack, the statement ascertained that the impacted SUDPS system has been secured. The amount demanded in ransom or the data type exfiltrated was not explicit in the statements posted by Stanford University or the Akira ransomware group.
The investigations into the Stanford University ransomware attack have been ongoing. Since the statement about the SUDPS ransomware attack and its investigations was posted on the same day Akira claimed it, the details covered in the investigation reports might not be thorough.
Stanford Ransomware Attack: Akira’s Dark Web Post
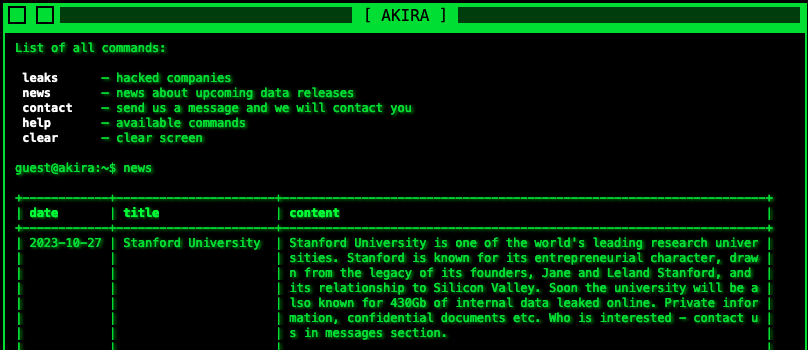
The Akira ransomware group posted details about Stanford University on its website. “Send us a message and we will contact you,” read the Stanford University ransomware attack threat.
Dominic Alvieri, Cybersecurity Analyst tweeted about the SUDPS ransomware attack by Akira. He wrote that Akira has 430 GB of internal data from Stanford University.
Previous Cyberattack on Stanford University
Stanford was embroiled in a data leak incident in 2021. The Clop ransomware group managed to pilfer and leak the personal information belonging to the Stanford community.
The Stanford data leak comprised of Social Security Numbers, addresses, emails, family details, and financial data.
This Stanford data leak was in connection with the Accellion file transfer vulnerability exploitation by Clop. Just like MOVEit vulnerability exploitation by Clop which allowed them to gain access to several clients of MOVEit, the Accellion incident led to the exposure of its clients.
The Accellion cyberattack was successful after exploiting a 20-year-old legacy service using its file transfer platform. The legacy service was discontinued in April 2021.
There is always a probability of reusing leaked data on the dark web. Cybercriminals may find details that they could misuse to launch further attacks at a later date.
Despite Akira claiming the latest Stanford ransomware attack, it was not found how they infiltrated its systems.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.




















































