In a collaborative investigation, a team of security experts disrupted the operations of the RedLine Stealer.
In a series of tweets, ESET Research elaborated how, with the help of GitHub, and Flare Systems, they managed to disrupt the operations of RedLine Stealer temporarily.
Disrupting RedLine Stealer Operations — A successful collaboration
In conversation with The Cyber Express, Malware researcher at ESET Research Mathieu Tartare elaborated on the dead-drop resolver and how it was used by the RedLineStealer.
“A dead drop resolver is an existing, legitimate website used to host information that points to additional command and control infrastructure (C2) controlled by the attacker,” Tartare said.
For example, one can store an encrypted C2 address in a GitHub repository, a Reddit or imgur comment, a Steam community profile, etc. Malware will retrieve this encrypted C2 address from the legitimate website and decrypt it. It will then be able to contact its C2 server.
“In the case of RedLine Stealer, it’s used by the RedLine panel (used by affiliates) to obtain the address of back-end servers (controlled by RedLine stealer operators/resellers). What we refer to as RedLine panel is a GUI control panel used by affiliates to manage infostealing campaigns,” Tartare concluded.
In the absence of taking down the repositories, RedLine stealer operators will no more have the backend servers for authentication. They will need a new, and full panel update for their customers.
On noting the repositories being used as dead drop resolvers, the ESET Research team notified one of their contacts at GitHub after which it was taken down.
Details about the RedLine Stealer being disrupted
Threat research firm ESET Research, software development hosting service GitHub, and cybersecurity firm Flare system collectively disrupted RedLine Stealer activities.
Researchers found modules of the third layer of RedLine Stealer during investigations.
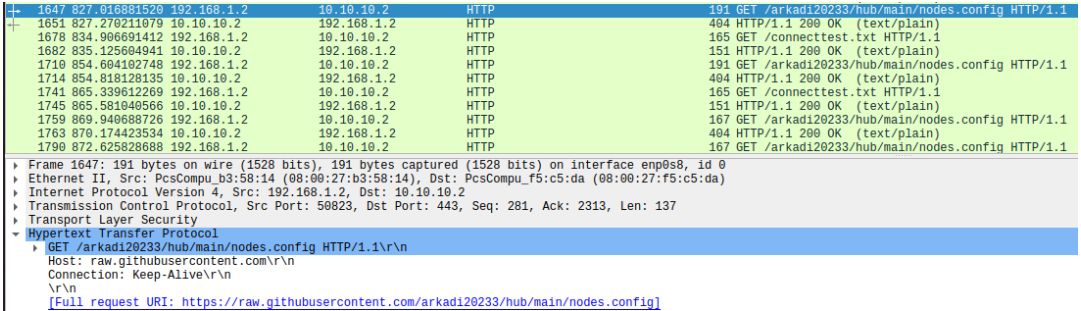
Four repositories were found along with the backend which was not shown publicly, a Sleuthcon report read.
The four repositories were as follows –
- github[.]com/lermontovainessa/Hub
- github[.]com/arkadi20233/hub
- github[.]com/ivan123iii78/hub
- github[.]com/MTDSup/updateResolver
Fortunately, there were no fallback channels noticed by researchers which led to the confirmation that the removal of the repositories would break the authentication of panels that were used by Redline Stealer.
In the case where a fallback mechanism would have been in place, taking down the GitHub repositories may not have been sufficient to disrupt the panels as they would have an alternate way of contacting their backend server,” Tartare told The Cyber Express.
It was also found that despite the removal of the repositories, the back-end servers would not be impacted however, it would lead the RedLine Stealer developers to create new panels for their buyers.
Details about the RedLine Stealer
The RedLine Stealer malware was first discovered by researchers in 2020. It steals user credentials, browser data, financial information, data from cryptocurrency wallets, etc.
RedLine Stealer is accessed by cybercriminals as a Malware-as-a-Service by paying a subscription fee.

The information stealer can be found on Russian underground forums for about $100 per month. It gets installed through phishing emails sent to targets, and trojanized applications.
“For the price, an affiliate gets a control panel that can generate malware samples and act as a C&C server for them,” Tartare said to The Cyber Express.
RedLine fetches the details of the software, system location, peripheral device, and so on. RedLine Stealer evades detection on infected devices by impairing its defenses and modifying the antivirus tools.
Researchers found that the information stealer was under development and was regularly upgraded to increase its impact.
RedLine Stealer recent incident
Advertisements with RedLine Stealers placed on Facebook business and community pages were found by researchers. Cybercriminals targeted credible names to lure their targets to exploit their data.
The fraudulent advertisements on Facebook were tricking people by offering free downloads of AI chatbots. They appeared to be offering access to ChatGPT and Google Bard to unsuspecting users.
This information-stealing campaign was detected in January this year and continued through March.

According to a Veriti research report, Greece, India, USA, Mexico, and Bangladesh were targeted by cybercriminals among other nations.
To avoid being infected by information stealers, it is critical that users limit the download of executables. Having clear policies about sandboxing executables before downloading is also recommended to avoid falling prey to information-stealing malware.