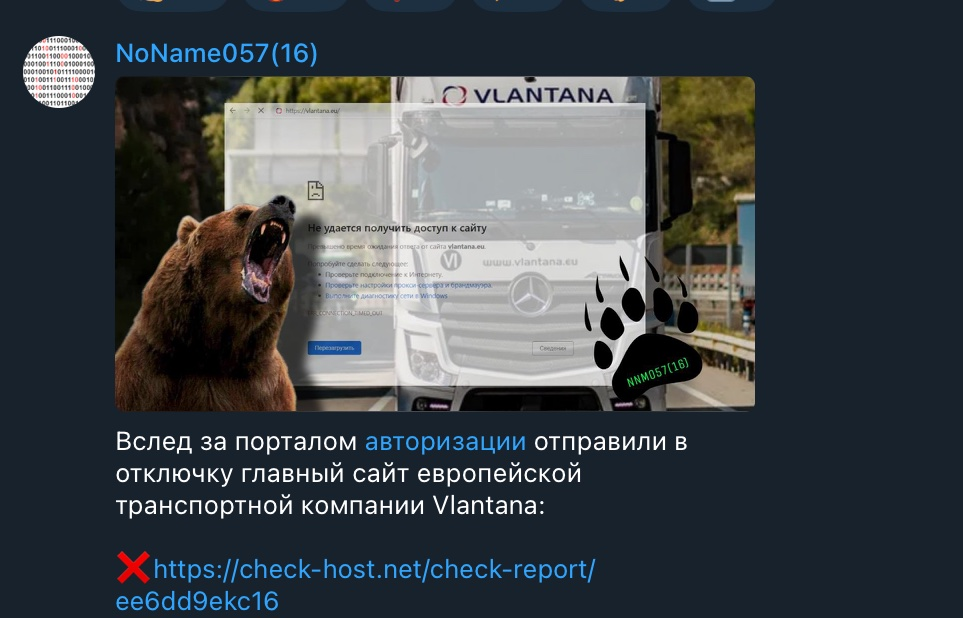
The attacks of pro-Russian threat actor NoName on European logistics and transportation companies continue. Lithanian transportation and warehousing logistics services Vlantana and UAB RUSKO are the group’s latest victims.
The ongoing pattern of attacks indicate that the hit on on Vlantana and RUSKO’s websites is part of a larger campaign aimed at disrupting the operations of European logistics and transportation companies.
The disruption of Vlantana’s website led to the company’s portal being taken offline, which caused significant interference in its operations.
The attack on RUSKO’s website is also believed to have caused significant disruption, with the company’s website being entirely down.
NoName is known for using various tactics, including phishing emails and malware to carry out its attacks. The group has been active since 2019 and has targeted multiple industries, including healthcare, education, and technology.
Pro-Russian TA NoName on the rise
In another incident, the Pro-Russian hacker group NoName listed Japanese organizations, including railway services, as its targets.
The retaliation came after Japan imposed sanctions against 48 Russian individuals and 73 organizations in response to Russia’s aggression against Ukraine. The targeted organizations include the Petroleum Association of Japan and East Japan Railway Company.
The Japanese government imposed more sanctions on Russia a month ago in response to its missile attacks in Ukraine. The latest measures include freezing assets, prohibiting exports to specific entities of the Russian Federation, and banning exports of items that could enhance Russian industrial capacities.
These measures will come into effect immediately, except for the asset freeze measures for the specific bank of the Russian Federation, which will be implemented from March 30, 2023.
NoName emerged in March 2022, at the onset of the Russian invasion of Ukraine.
Since then, the pro-Russia hacker group has claimed responsibility for various cyberattacks on government agencies, media, and private company websites in countries including Ukraine, the United States, and several European nations.
The group publishes information about their attacks on their Telegram messenger channel and has been accused of sending threatening letters to Ukrainian journalists.
Despite the group’s reported number of successful attacks seeming large, statistical information indicates the contrary.
The group’s success rate is 40%. Websites hosted on well-secured servers can withstand the attacks. Around 20% of the attacks the group claims to be responsible for did not match the targets in their configuration files.
The cyberattacks on European logistics and transportation companies and the recent threat posed by the pro-Russian hacker group NoName highlight a bigger campaign and a need for a sophisticated system to detect and prevent these attacks.
It also emphasizes businesses need a robust cybersecurity framework to protect their sensitive information and operations.
Businesses and governments need to work together to mitigate cyber threats and improve cybersecurity practices to ensure the safety of the economy and the public.




















































