Infamous Play ransomware group has extended its list of victims by adding 17 new names of companies based in the US, UK, Netherlands, and Canada. The list of Play ransomware attack victims was published on the dark web portal of the cybercriminal group.
On November 28, a list of purported victims targeted by the Play ransomware attack emerged, warning of data exposure if ransom demands aren’t met by December 4.
Play Ransomware Attack Victims
The ransomware attack has targeted 14 companies based in the US and the other three based in the UK, Netherlands, and Canada.
What adds to the seriousness of the alleged Play ransomware attack is the category of companies listed by the ransomware gang.
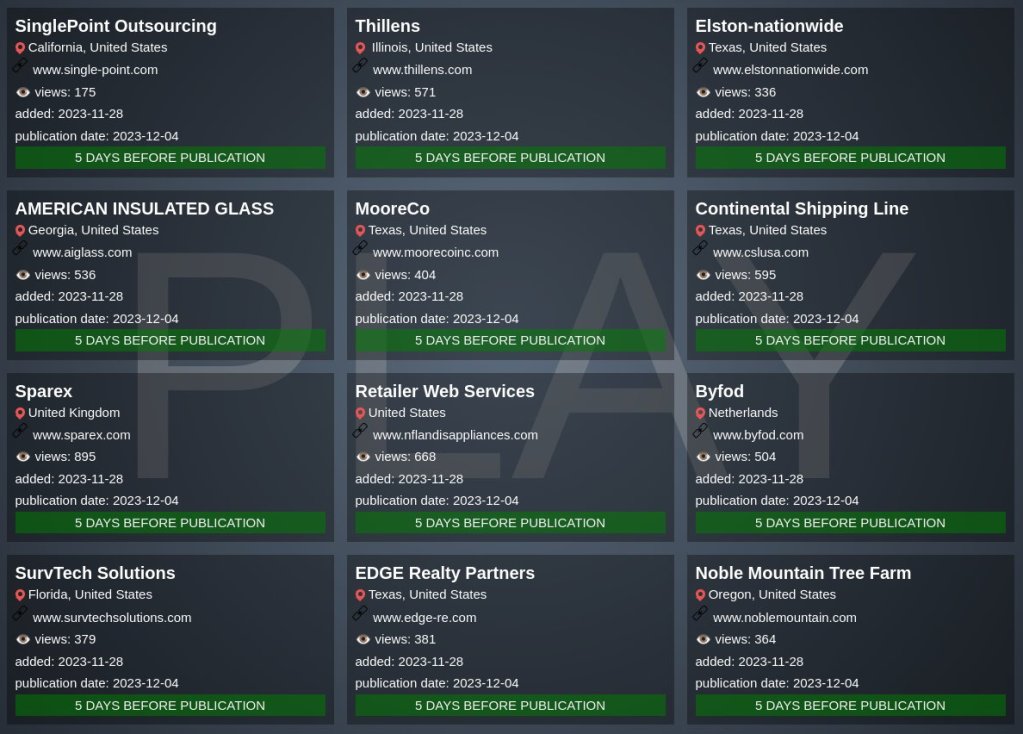
Single Point Outsourcing, Thillens, Elston Nationwide, American Insulated Glass, Moore Co., Continental Shipping Line, Sparex, Retailer Web Services, Byfod, SurvTech Solutions, EDGE Realty Partners, Noble Mountain Tree Farm, Unitransfer, SC Hydraulic Engineering, Labtopia, OLA Consulting Engineers, and Canderel Management are among the victims impacted by the alleged Play ransomware attack.
The Play ransomware group has listed companies across IT services, outsourcing, retail, real estate, shipping, engineering, consulting, and management services. These companies are at risk of exposing extensive details of ordinary individuals who are unaware of the potential threat.

The potential victims of this data breach are individuals seeking deliveries, employment, IT services, or consultation from the affected companies. Such a breach poses severe risks of identity theft and various forms of fraudulent activities.

Ransomware attacks often lead to reputational damage for the companies that face the brunt by losing customer base, trust quotient in the market, and future business prospects. Making things worse, legal consequences lead to immediate financial losses for the victims of data breach.
One wise strategy to avoid incidents like the Play ransomware attack is to use content filters and virus scanners on your mail servers. These applications reduce the possibility of spam mails landing in your mailbox with harmful attachments or compromised links.
About Play Ransomware Group
Hackers from the Play ransomware group target businesses and governmental establishments. Since its formation in 2022, the group has attacked targets in the US, UK, Canada, Netherlands, Brazil, Argentina, Germany, Belgium, and Switzerland.
Experts in security believe the Play ransomware group has ties to Russia. PlayCrypt is another name for the group. It was created by a team known as Balloonfly, which Symantec monitors. After encrypting files, the group’s ransomware appends the suffix “.play.”
The word “PLAY” and the email address of the group are included in its ransom note. Two fresh, proprietary tools have been employed by the Play ransomware organization to bolster their attacks, namely, Volume Shadow Copy Service (VSS), Grixbat.
What to do if your company has already been affected
These actions as stated by the National Cyber Security Center of the UK, could lessen the damage if ransomware has already infected your company:
- Disconnect all network connections, whether wired, wireless, or based on a mobile device, from the compromised PCs, laptops, or tablets right away.
- If the situation is really bad, think about whether you really need to disengage from the internet, disable any switches and turn off your Wi-Fi.
- Change all of your login information, including passwords (particularly for the administrator and other system accounts); nevertheless, make sure you aren’t preventing yourself from accessing systems that are necessary for recovery.
- Replace the OS on the compromised devices and safely wipe them.
- Make sure the backup is free of viruses before restoring from it.
- To download, install, and update the operating system and any other software, connect devices to a sanitized network.
- Run, install, and update your antivirus program.
- Reestablish a network connection.
- To find out if there are any infections left, keep an eye on network traffic and do antivirus scans.
To heighten the chance of avoiding ransomware attacks, it’s crucial to create offline backups and store them in a separate location, preferably offshore, away from your network and systems. Alternatively, consider utilizing a secure cloud service explicitly designed for this purpose.
Paying ransom, in most cases, is not a wise choice to make. Even after companies pay the ransom, there is no surety that the data will be retrieved. The computer systems still continue to be infected with the ransomware and are more likely to be attacked in the future.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.





















































