PathLegal, a prominent online legal service provider in India, has fallen victim to a devastating data breach, resulting in the exposure of sensitive information belonging to an astounding 127,000 legal professionals and students.
The alleged PathLegal cyber attack, orchestrated by the cybercriminal group Hacktivist Indonesia, was part of their larger “OpIndia” campaign.
PathLegal, known for its extensive network of over 10,000 legal professionals, remained accessible even in the aftermath of the alleged cyber intrusion.
Presently, the PathLegal cyber attack remains unconfirmed, and the company has not released an official statement acknowledging or addressing the alleged breach.
PathLegal Cyber Attack
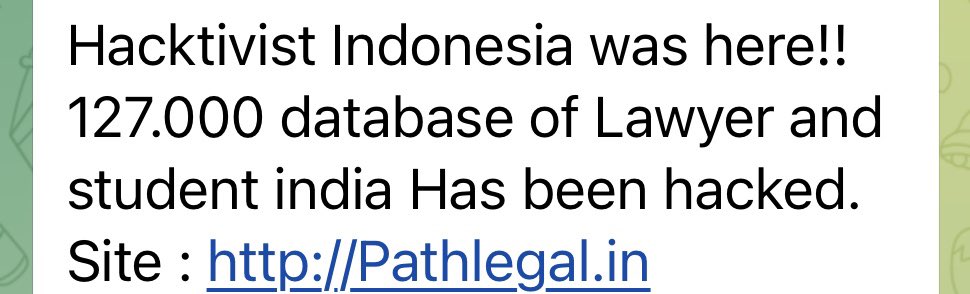
Hacktivist Indonesia wrote that they exfiltrated 127,000 databases of lawyers through the PathLegal cyber attack. The hacked database also included student information.
Threat Intelligence platform Falcon Feeds posted the above screenshot from the Telegram channel of the hackers. They tweeted, “The breach by Hacktivist Indonesia as part of their OpIndia campaign.”
Hacktivist Threats in Connection with the G20 India Summit
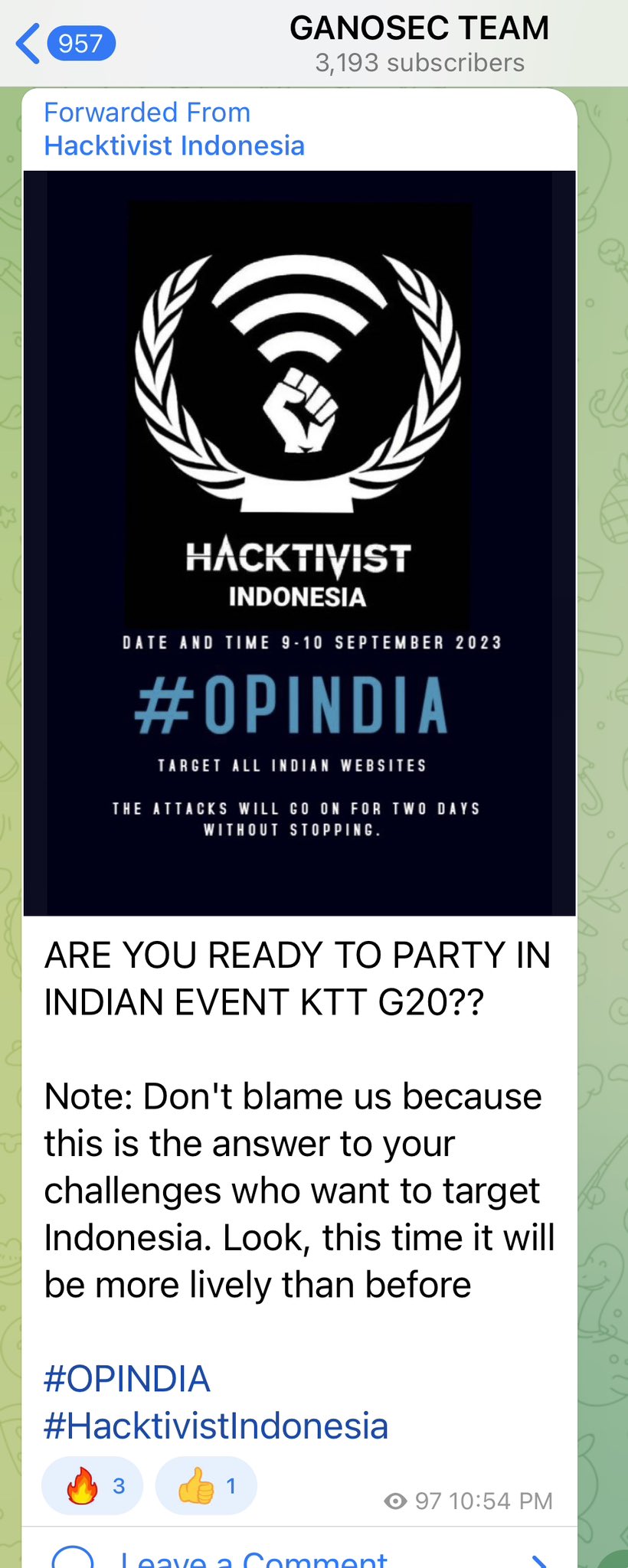
Several Indonesian hacktivist groups posted tweets about targeting Indian websites and threatened to disrupt Indian digital infrastructure prior the two-day G20 Summit 2023. They claimed to hack websites and launch cyber attacks.
The Twitter channel of the Indonesian hacktivist group Jambi Cyber Team was used to publicly release records of registrants with photo IDs from educational institutions and government websites. The account has now been suspended.
The G20 Summit 2023 was a global meeting with over 19 countries along with the European Union participating in it to discuss various international agendas. Hackers took to Telegram to announce their plans around G20 cyber attacks between September 9 and 10, 2023.
Hacktivists including Ketapang Grey Hat Team, Hacktivist Indonesia, Jambi Blackhat, Warrior Garuda Crime, and Karawang Cyber Team among others launched defacement attacks on websites of Indian organizations.
Indian Hacktivists Targeting Indonesia
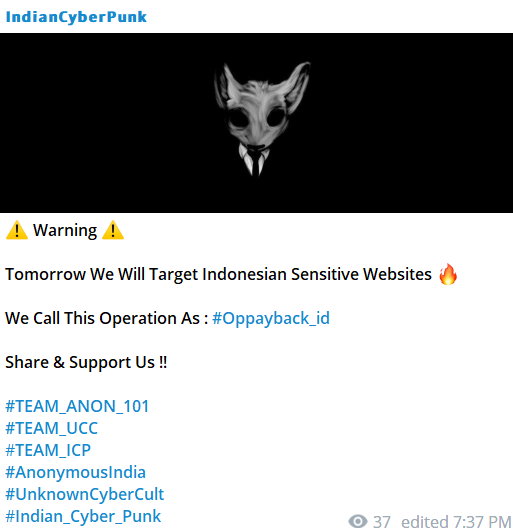
In response to the relentless targeting of India by hackers, an Indian hacktivist collective, known as the “Indian Cyber Punk,” has issued a stern warning.
Via a Telegram message, the group declared their intention to retaliate with cyber attacks on critical Indonesian infrastructure. The message revealed their operation name as “#Oppayback_id,” specifically aimed at addressing the ongoing cyber threats.
Several other groups, including TEAM_ANON_101, TEAM_UCC, TEAM_ICP, Anonymous IndiaIndia, UnknownCyberCult, and Indian_Cyber_Punk, have offered support for the Indian hackers involved in the ongoing cyber conflict.
Threat Alert: Attack on Ministry of Information and Broadcasting
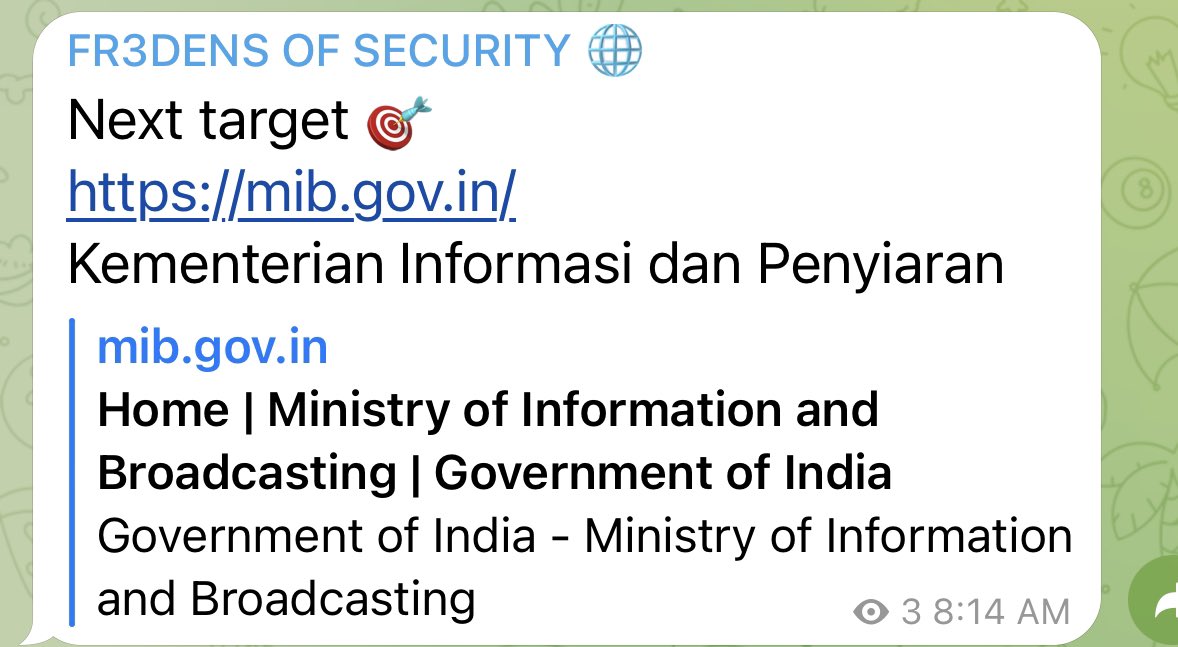
The hacktivist group known as “Fr3dens of Security” has identified India’s Ministry of Information and Broadcasting (MIB) as a potential future target. The MIB, responsible for overseeing regulations and laws pertaining to press, cinema, and related domains, is now on the radar of this hacktivist collective.
The website of MIB was accessible when checked by The Cyber Express.
Indonesian text, “Kementerian Informasi Dan Penyiaran,” was written in the threat which translates to the Ministry of Information and Broadcasting.
Falcon Feeds tweeted the above image and wrote that Fr3dens of Security created a new Telegram channel.
In retaliation of the targeting of Indian digital infrastructure, Falcon Feeds tweeted the names of the Indonesian websites listed by the group called Team NWH security.
They were as follows –
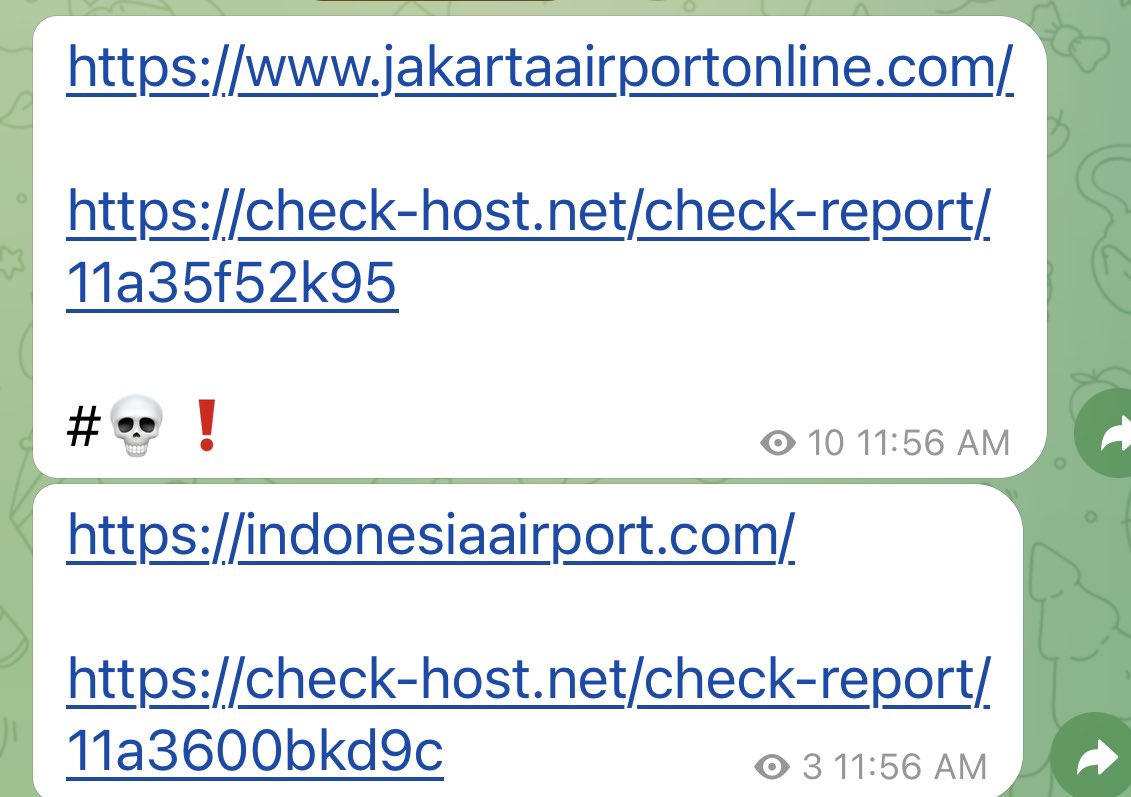
Their checkhost links were also provided to check the status of the websites after the alleged cyber attacks on them. Indonesia’s computer emergency response team website was also allegedly hacked by Team NWH Security.
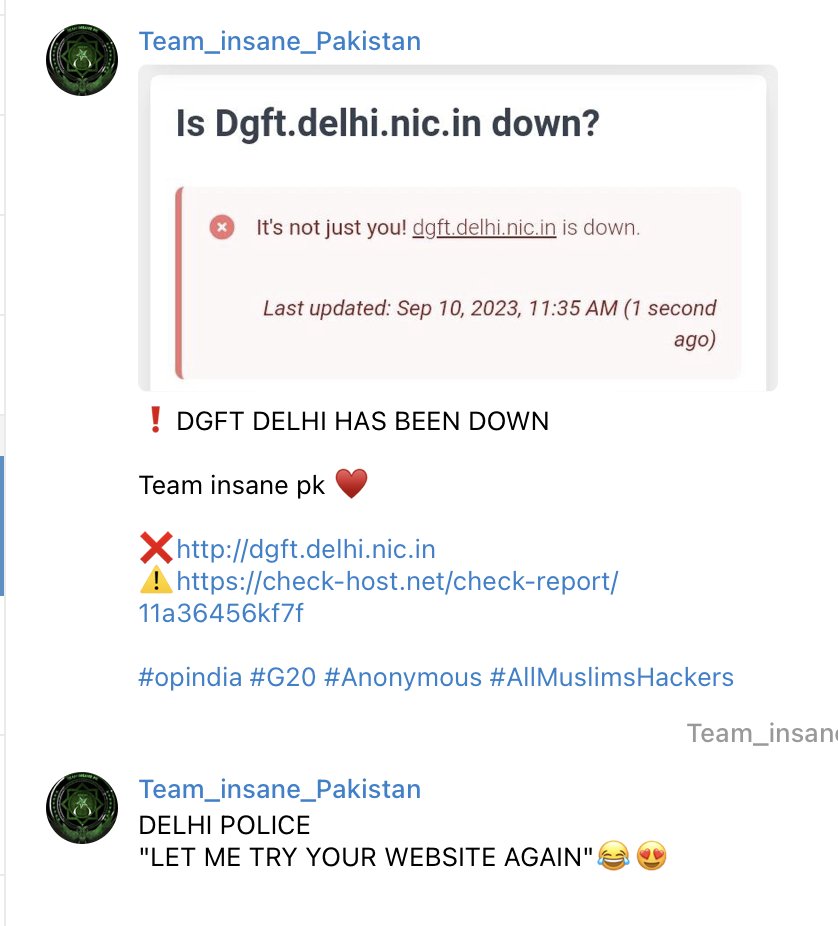
Other hacktivist groups including those from Pakistan namely Team Insane Pakistan posted the checkhost link to the Directorate General of Foreign Trade (DGFT).
The website was not accessible at the time of writing.
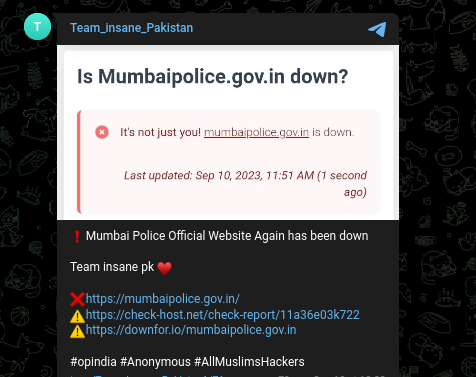
The Mumbai police website was posted about on the Telegram channel of Team Insane pk.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.



















































