In a cunning ploy to compromise Windows PCs, hackers have turned to Facebook ads featuring provocative images to entice unsuspecting users into downloading the NodeStealer malware.
Bitdefender recently uncovered this sophisticated malvertising campaign involving compromised Facebook Business accounts being used to distribute the notorious NodeStealer malware.
This new form of malvertising campaign aims to pilfer valuable information, such as browser cookies, saved usernames, and passwords, ultimately jeopardizing a user’s online security.
NodeStealer Malware and Malvertising Campaigns

Cybercriminals are increasingly leveraging social media networks, with a focus on exploiting Meta’s ad network on Facebook. This approach allows them to target a vast user base and compromise their privacy.
Researchers at Bitdefender Labs identified several key elements of this malvertising campaign, including 10 compromised business accounts that distribute malicious ads, perpetually exposing users to online threats.
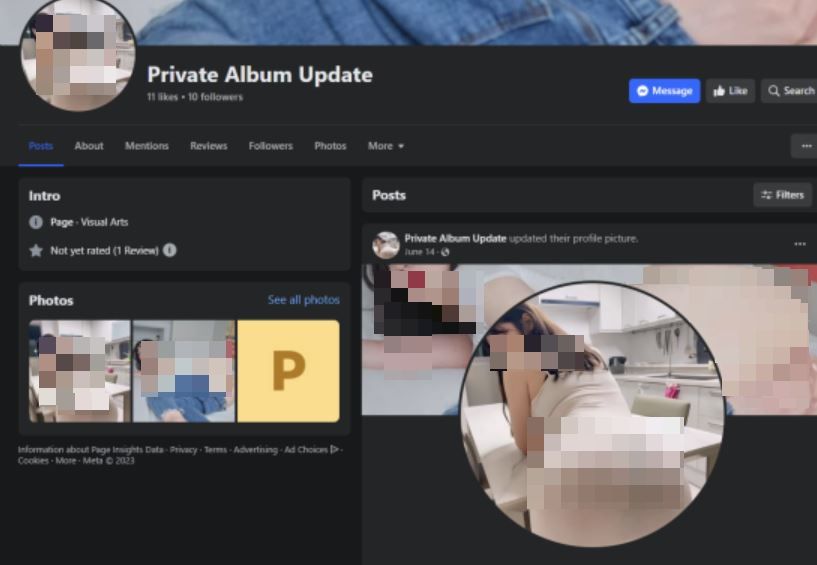
An upgraded NodeStealer malware version enhances data theft capabilities. Profiles featuring enticing images lure engagement. 140 diverse ad campaigns broaden outreach. Tactical ad management evades detection with rotating ads.
In a previous encounter with NodeStealer malware on Facebook, the malware masqueraded as fake PDF and XLSX files. However, the recent resurgence of NodeStealer malware via a malvertising campaign on the platform demonstrates its adaptability and the attackers’ commitment to refining their techniques.
Enhanced Functionality of NodeStealer Malware and Previous Campaigns
The attackers have not only revived NodeStealer malware but have also introduced new features, including the ability to target cryptocurrency wallets and facilitate the download of additional malware.
Previously, Netskope Threat Labs monitored a campaign that employed malicious Python scripts to pilfer Facebook users’ credentials and browser data. This campaign primarily focuses on Facebook business accounts, employing counterfeit Facebook messages containing malicious files.
The attacks have primarily affected victims in Southern Europe and North America, with the manufacturing services and technology sectors being the most heavily targeted.
The campaign seems to be a fresh iteration of the Python-based NodeStealer, still geared towards compromising Facebook business accounts. However, unlike earlier iterations of NodeStealer malware, this variant also harvests all available credentials and cookies, not limited to Facebook alone.
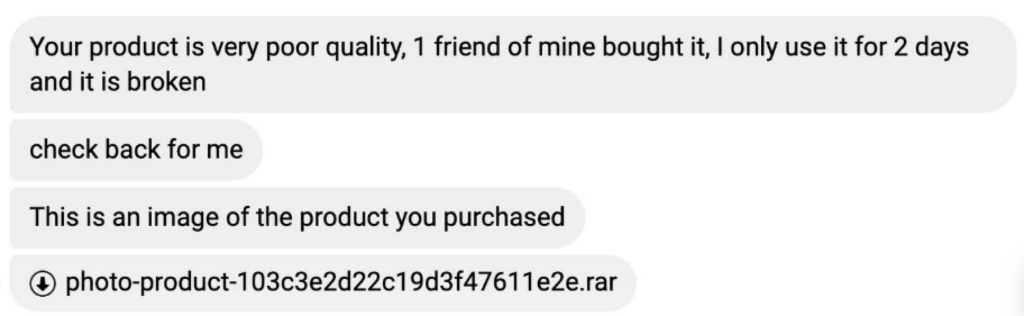
According to Netskope, this particular variant of NodeStealer was hosted on the Facebook Content Delivery Network (CDN) and distributed to victims as an attachment within Facebook messages.
The attackers utilized images of defective products as lures to persuade owners or administrators of Facebook business pages to download the malware payload. Unlike previous NodeStealer campaigns, this one employs a batch file instead of an executable as the initial payload.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.






















































