A new cybercriminal group calling themselves Wolphv Ransomware Group has been reported by researchers. Wolphv claimed that their ransomware has defenses against decryption leaving data locked. In another blatant statement, they mentioned that their leader is a student of the University of Michigan (Uofm).
Wolphv Ransomware Group
The Twitter account of the Wolphv ransomware group (wolphvgroup) was created this month and had some tweets about not being taken seriously. “Why does nobody take us seriously,” read a tweet made by the new ransomware group.
Another tweet read, “guys doubledelete (uofm student) is the leader of wolphv but u didn’t hear that from me.”
They posted an introduction on their dark web portal that said that they have been curating ransomware since 2023. “The other so-called ransomware groups? Forget about them! (they don’t know the first thing about ransomware),” the introduction continued.
The messages and the tone of the statements point towards the naivety of the hackers.
Wolphv Ransomware Capabilities
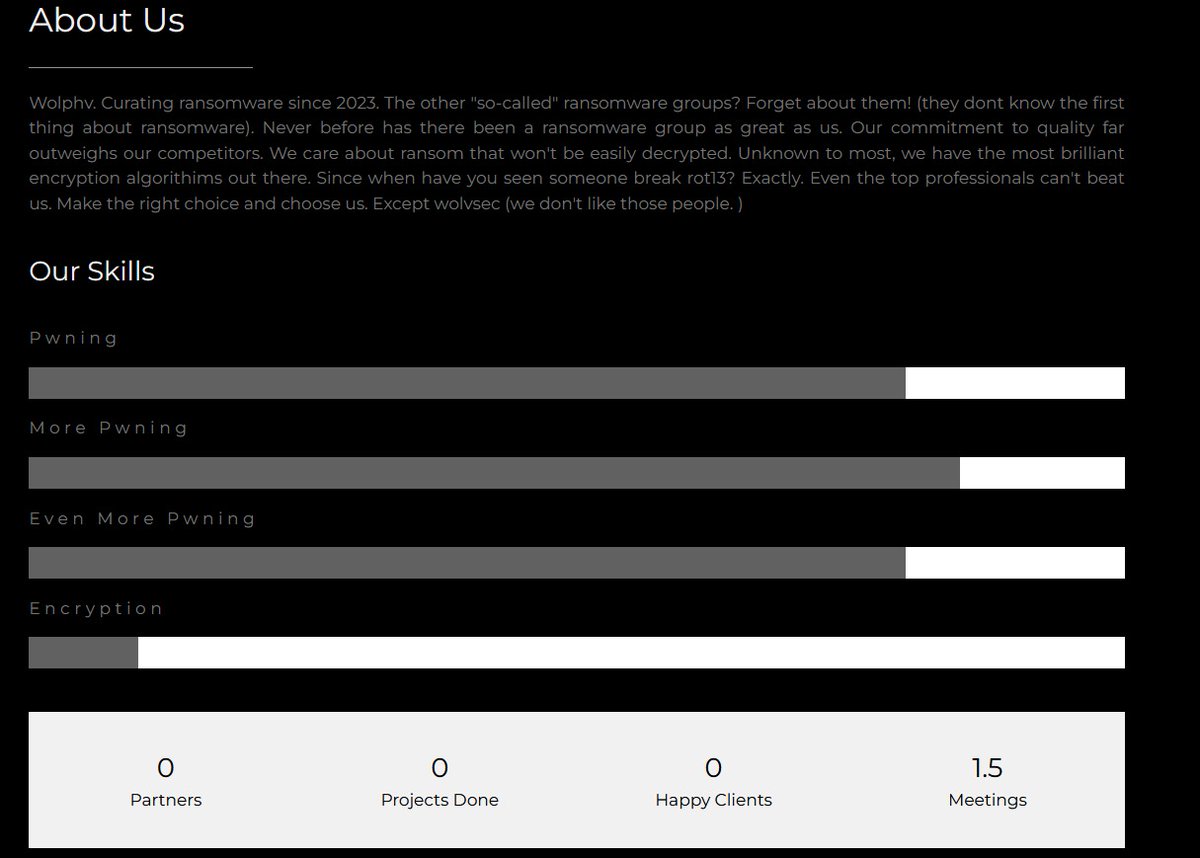
The members of the Wolphv ransomware group boasted of having a brilliant encryption algorithm and that they breached rot13. ROT13 is an encryption algorithm that replaces the existing letter with the one in the 13th position from it.
Besides pwning (compromising a computer), the Wolphv ransomware can encrypt data. While asking people to choose their ransomware, they said that they do not like Wolvsec. WolvSec is a security club at the University of Michigan comprising of students, alumni, staff, and other professionals.
Based on the statements made, it looks like members of the Wolphv group want to defame the University of Michigan.
Race of Cybercriminals on the Dark Web
The dark web is getting more and more traction with each passing day with teenagers and other users wanting to make a name and reputation. A user on a hacker forum recently claimed that it was them who had the original Sony data leaks and not the group RansomedVC.
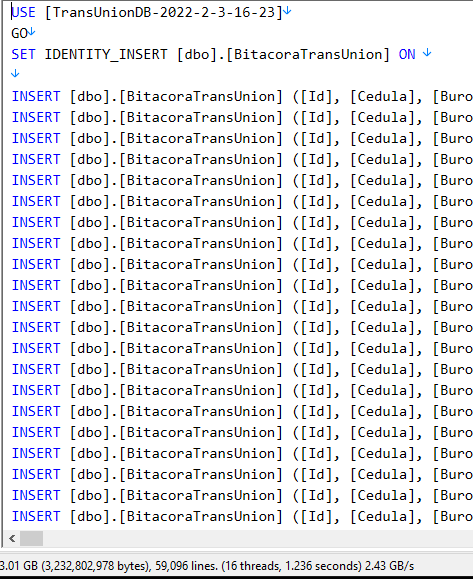
All this while organizations have been coming forward to thwart the claims as seen in the TransUnion incident. The credit monitoring and reporting agency TransUnion confirmed to The Cyber Express denying that the samples released on the dark web did not match theirs.
Twitter/ X recently witnessed another major cyber attack on Donald Trump Junior’s profile which came to light when strange tweets got posted one after another. The hackers shocked the media and followers of the Trump family when they read the tweet, “I’m sad to announce, my father Donald Trump has passed away. I will be running for president in 2024.”
The account was restored immediately and tweets were taken care of within hours.
While some hackers breach social media for malicious purposes, others sell tools for cyber attacks. These tools are worked upon by paid criminals who are tasked with creating malware that evades detection and the impact of which can’t be easily reversed.
This was seen in a research conducted by Sophos, the cybersecurity solutions firm in collaboration with its internal team called Sophos X-Ops. They found that offensive research contests and competitions were conducted on Exploit and XSS boards among other underground forums.
One of the dark web competitions asked users to explain in writing with graphics how to exploit zero-days in Windows and Linux, privilege escalation, and malware creation with codes to modify it.
All this while victim organizations especially healthcare struggle to keep services ongoing. After suffering a cyber attack this year, Prospect Medical facilities are urging the state to fasten the sale of their facilities to Yale New Haven Health.
The healthcare officials were discussing facing a dire financial crisis after the ransomware attack. Seeing the state of hackers who are young and restless, it will come as no surprise if hackers from the Wolphv ransomware group, in their desperation to make a name, randomly start deploying ransomware and demanding a ransom.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.




















































