The Python Package Index (PyPI) is a prominent hub for numerous software packages designed for the Python programming language. However, its popularity has made it a prime target for malicious actors seeking to exploit its widespread user base.
Recently, a large-scale campaign was discovered by Cyble Research and Intelligence Labs (CRIL) involving the distribution of malicious Python wheel (.whl) files that carry a new form named ‘KEKW malware’.
According to CRIL’s report, the malware is capable of can stealing sensitive information from compromised systems and performing clipper activities that allow it to hijack cryptocurrency transactions.
The packages under scrutiny were not in the PyPI repository, indicating that the Python security team had removed them.
It is impossible to determine the number of people who downloaded them, but the impact may have been minimal due to the prompt action, reads the report.
Moreover, several malicious packages were observed spreading KEKW malware, containing domains linked to the threat actors.
What is KEKW malware?
In the programming world, the primary function of the Python package file includes various capabilities, such as anti-debugging, persistence, collecting system information, stealing sensitive data from various applications, and more.
KEKW malware terminates its execution if it identifies pre-defined blacklisted hard-coded strings such as the username, computer name, system IP address, or hardware ID. It also checks for security-related processes running on the system.
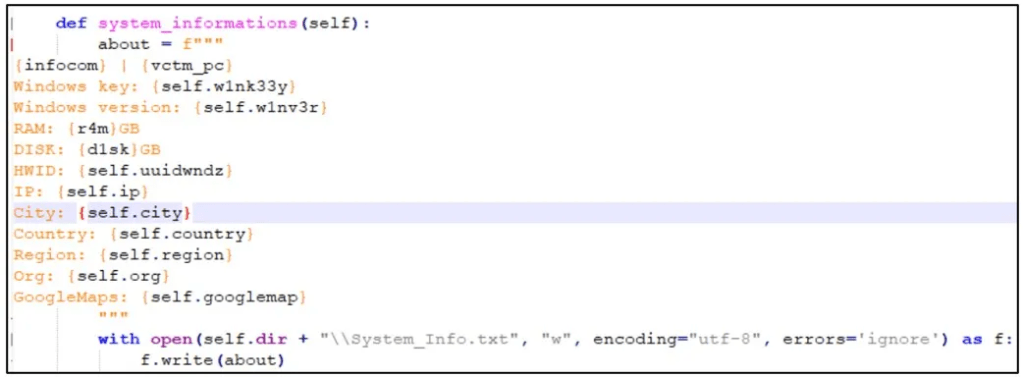
This function can extract the login username, computer name, Windows product key and version, RAM capacity, HWID, IP address, geographic location, Google Maps information, and other sensitive data.
By collecting this information, the malware can understand the infected system comprehensively, enabling it to carry out further malicious activities such as identity theft or financial fraud.
KEKW malware: Technical analysis
According to the report, the malicious Python script is designed with a singular goal in mind: to surreptitiously gather sensitive information from a target’s web browser.
This information can include passwords, cookies, browsing histories, credit card details, tokens, and user profiles.
However, the nefarious activities of the threat actors extend beyond mere data theft, as they have also incorporated clipper functionality and stealer payloads into their attacks.
These payloads contain various crypto addresses linked to the actors’ clipper activities, which can hijack cryptocurrency transactions and redirect funds to their accounts.
In fact, CRIL found that one Bitcoin address that was associated with over 20 packages has seen a sharp increase in transaction activity over the past month.
The majority of Python files within the packages contained the domain name “kekwltd[.]ru,” while only a few contained “blackcap[.]ru,” indicating a possible link between these domains and the threat actors.
KEKW malware: Conclusion
The discovery of malicious packages in the PyPI repository highlights the importance of the security measures that need to be taken by developers worldwide to prevent cyber attacks.
PyPI should continuously monitor the repository for suspicious activity and promptly remove malicious packages to prevent user damage.
Developers and users should also be cautious and avoid downloading software packages from untrusted sources.
Updating the software frequently and using reputable antivirus software to ensure maximum protection against cyber threats is essential.