MetaStealer is a new and sneaky enemy that has emerged in the field of cybersecurity. This software, which was created using the Go programming language, has infected macOS devices, notably those used by corporate users.
As per findings by SentinelOne researchers, a multitude of malware samples are actively targeting macOS business users.
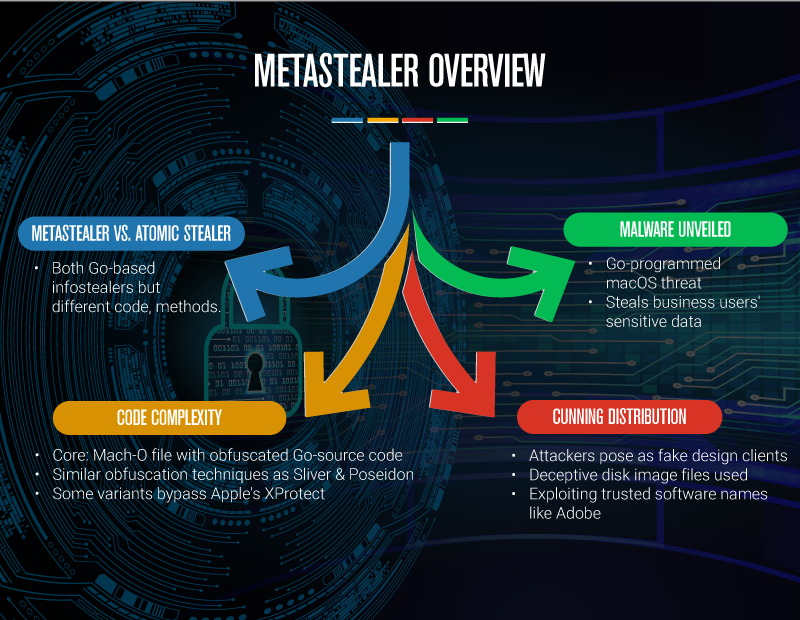
These attacks employ social engineering tactics, with cybercriminals masquerading as design clients. They entice unsuspecting victims into executing malicious payloads, highlighting the threats faced by macOS users.
This report reveals distribution strategies, complicated coding, and the alarming pattern of online threats of MetaStealer focusing on Mac users.
Distribution Techniques of MetaStealer
MetaStealer has infiltrated the macOS ecosystem by employing distribution techniques. Cyber attackers deftly pose as phony design clients to seduce victims into unintentionally activating potentially harmful payloads.
Their deceptive strategy includes impersonating well-known software firms like Adobe, allowing them to camouflage their malicious intent.
Malware Details: Atomic Stealer vs. MetaStealer
A Mach-O file written in Intel x86 assembly language that houses precisely obfuscated Go source code is at the heart of MetaStealer.
This degree of code obfuscation is similar to methods used by other well-known viruses, such Sliver and Poseidon.
Notably, some variations can get past XProtect, Apple’s built-in antivirus program. Atomic Stealer and MetaStealer both use the Go programming language and are classified as infostealers, but their approaches to distributing their code are very different.
Each intrusion presents a different difficulty due to the diverse threat actors and their specialized strategies that make up the constantly changing cyber threat landscape.
Consequences on Cybersecurity
MetaStealer’s appearance underlines the expanding pattern of cyber threats that target macOS users, especially in the corporate sector. Although it offers some protection, Apple’s XProtect is not perfect.
Organizations need to maintain a high level of alertness. Examining malware signs, putting in place strong security measures, and training staff on how to protect sensitive data are all required to achieve this.
Threats against macOS have increased significantly in recent years, which suggests a change in cybercriminals’ priorities. Macs are more appealing targets as they grow more common in the business sphere.
Elusive Origins, Potential Motives
Cybersecurity specialists have had difficulty unraveling MetaStealer’s origins.
Even though it was developed with great sophistication, it has traits with other infostealers, suggesting that it may have contacts with other cybercriminals.
The precise identity of the threat actors who are responsible for MetaStealer is yet unknown. For effective countermeasures to be developed, it is essential to comprehend the reasons behind MetaStealer.
While monetary gain is a frequent motivation for cybercriminals, the theft of sensitive data from macOS users raises the possibility of a more sinister plan. It makes one wonder about possible business espionage or espionage actions.
MetaStealer uses social engineering techniques to exploit people’s weaknesses. Cybercriminals take advantage of consumers’ trust and manipulate them, effectively turning them into unwitting allies in the propagation of this threat.
The ongoing evolution of MetaStealer is concerning.
As security professionals create protections, this virus evolves, making earlier defenses ineffective due to its capacity of avoiding detection. Hence, it is essential to take proactive cybersecurity measures to stay secure.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.






















































