IT professionals, amateur developers, Telegram channel moderators, and analysts are being hired on the dark web to launch cyberattacks.
A research by Securelist revealed that several candidates are looking for jobs on the dark web and have applied for positions, often dealing in illegal activities. The research, conducted between 2020 and 2022, concluded that the incentive of earning money without having legitimate credentials or background got candidates to post their resumes in a large volume.
Statistics of candidates applying for jobs on the dark web
(Image: Securelist)
Researchers reviewed around 155 dark web forums between January 2020 and June 2022. They found that the highest number of job advertisements were witnessed in March 2020, at the time when the COVID pandemic had impacted the work scenario.
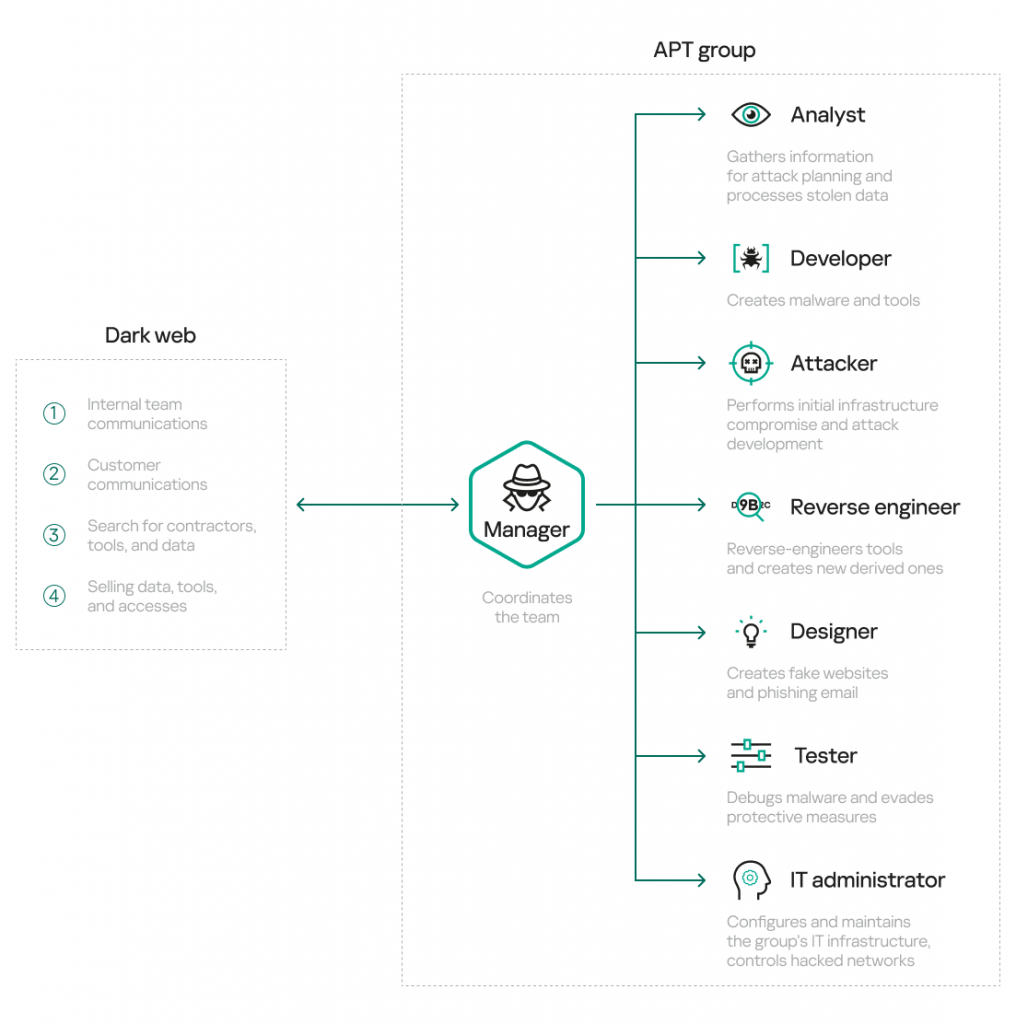
The employers were among hackers and APT groups looking for those candidates who could develop and launch malware attacks.
The demand for developers was at 61%, who were also the best paid with $20,000. In contrast, other IT professionals were offered between $1,300 and $4,000.
Some legal jobs, such as creating IT courses, were also offered. However, these courses could have also been to train new hackers.
(Image: Securelist)
According to the report, some candidates, who had applied for jobs on the dark web, did so because they did not have higher education, could not qualify based on military service requirements, or failed to provide for any additional requirements.
(Screenshot of an application. Image: Securelist)
Researchers pointed out that some of the jobs offered perks that included flexibility in not having a dress code, no fixed work, or work timings.
Besides IT-related jobs, about 200,000 job ads were posted during the duration of the survey. The candidates on the dark web were selected based on test assignments, reading their portfolios or resumes, interviews, and/ or after probation.
Ransomware gangs and recruitment
Ransomware groups operate like businesses and require a team of skilled employees to carry out their operations, wrote Digital Shadows. These groups can have multiple members specialized in areas such as malware creation, reconnaissance, encryption, and more.
However, unlike legitimate businesses, ransomware groups cannot use professional networks or recruitment platforms to find talent, making their recruitment process different. They often recruit through their public data-leak sites where they post information about their victims and contact details.
If a group likes an applicant, they may move forward to the next stage, but feedback is not provided for those who are not chosen. The dark web employers even tested candidates in ransomware attack skills, including encryption of malware executables and evading detection.
Benefits such as fixed pay, a close-knit team, paid vacation, and sick leave were also promised. However, it could not be verified since neither was the screening legal nor the jobs on the dark web.
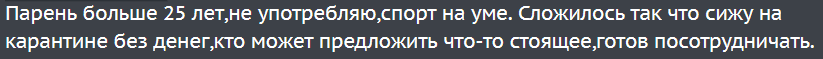
A job post calling itself legal also offered $100,000 per month for ‘pentesting.’ Several posts in the Russian language were also found as follows:
(Image: Securelist)
It translated to, “Guy over 25, no addictions, into sports. Quarantined without cash, looking for rewarding job offers, ready to cooperate.” The research noted that among the applicant were those who either lost their jobs, had pay cuts, or were asked to take mandatory breaks from work.
Hopelessness was also noticed as one of the prime reasons for candidates to turn to the dark web for jobs.
With corporates opening their door to employees and some others laying off employees, it is time for a reality check if extreme actions are leading candidates to desperately turn to places such as the dark web for job opportunities.
The police arrested a burglary gang that attacked homes and shops in Japan, according to a report posted in The Asahi Shimbun. The culprits testified that they were offered a high-paying job on the dark web that promised to pay up to 1 million yen. They were sentenced to jail after being found guilty.