LockBit 4.0 has made a surprising return, defying expectations following a recent crackdown by law enforcement that severely hampered their operations. Despite facing significant setbacks, the hacker collective has quickly bounced back, demonstrating their persistence in pursuing criminal activities.
Their defiance is evident in their latest actions, including the listing of 12 new victims on their data leak page and discussions surrounding the seizure of their websites, which they attribute to a likely exploitation of a PHP vulnerability.

On February 19, a message appeared on LockBit’s site from Operation Cronos: “This site is now under the control of the National Crime Agency (NCA) of the UK, working in close cooperation with the FBI and the international law enforcement task force, ‘Operation Cronos’. We can confirm that Lockbit’s services have been disrupted as a result of International Law Enforcement action – this is an ongoing and developing operation.”
For the unversed, the Department of Justice, in collaboration with international law enforcement agencies, dealt a significant blow to cybercriminal activity by disrupting the operations of the ransomware group.
However, in a swift retaliation, the group has now issued a defiant and provocative message aimed at law enforcement agencies, notably singling out the FBI.
In a lengthy message, the administrators of the LockBit ransomware group have released a detailed response, shedding light on their recent activities and motivations. The thread not only highlights the group’s failure to keep their systems up-to-date due to complacency but also speculates on the methods of their compromise and the reasons behind the FBI’s aggressive actions.
With a provocative tone and attempts to discredit law enforcement agencies, the thread provides insight into the ongoing battle between cybercriminals and authorities.
This deep dive into LockBit 4.0’s lengthy message offers a fascinating glimpse into the inner workings and mindset of one of the most notorious ransomware groups operating today.
Decoding LockBit 4.0 Message: A Deep Dive
The LockBit 4.0 lengthy message offers a detailed and insightful glimpse into the recent activities and audacious stance of the notorious ransomware group. Here are some key points highlighted in the message:
Admission of Negligence
LockBit 4.0’s administrative staff openly admit to their negligence, attributing a recent breach to their complacency and failure to keep server software updated promptly. This admission highlights the group’s willingness to acknowledge their shortcomings.
The group speculates on the method of intrusion, suggesting it may have been through a known vulnerability, such as CVE-2023-3824, or possibly a zero-day exploit. This speculation reflects the group’s awareness of cybersecurity vulnerabilities and exploits.
“Due to my personal negligence and irresponsibility, I relaxed and did not update PHP in time, the servers had PHP 8.1.2 version installed, which was successfully penetration tested most likely by this CVE, as a result of which access was gained to the two main servers where this version of PHP was installed,” reads the detailed note.
Adding further, the note reads, “I realize that it may not have been this CVE, but something else like 0day for PHP, but I can’t be 100% sure because the version installed on my servers was already known to have a known vulnerability, so this is most likely how the victims’ admin and chat panel servers and the blog server were accessed. The new servers are now running the latest version of PHP 8.3.3. If anyone recognizes a CVE for this version, be the first to let me know and you will be rewarded.”
Impact on RaaS Competitors
LockBit 4.0 hints at the broader impact of their actions, suggesting that other ransomware-as-a-service groups may have been compromised similarly. This insight sheds light on the interconnected nature of cybercriminal activities.
“I’m sure many competitors may have been hacked in the same way, but they didn’t even realize how it happened. I’m sure the forums I know are also hacked in the same way via PHP, there are good reasons to be sure, not only because of my hack but also because of information from whistleblowers. I noticed the PHP problem by accident, and I’m the only one with a decentralized infrastructure with different servers, so I was able to quickly figure out how the attack happened, if I didn’t have backup servers that didn’t have PHP on them, I probably wouldn’t have figured out how the hack happened,” explained in a note.
Motivation Behind FBI’s Actions
The group alleges that the FBI’s recent aggressive actions were primarily driven by their desire to suppress the release of sensitive information, notably concerning former President Donald J. Trump’s court cases. The group’s statement suggests a strategic understanding of the broader political landscape, implying that the timing of the FBI’s actions was not coincidental.
According to LockBit 4.0, the FBI’s intervention aimed to prevent the disclosure of crucial data from Fulton County, which included details on Trump’s legal battles. The group suggests that this move was politically motivated, as the information could potentially impact the upcoming US election. In a revealing commentary, the group expresses personal support for Trump, citing concerns over border security and characterizing President Biden as a puppet.
They assert, “The FBI decided to hack now for one reason only… the stolen documents contain a lot of interesting things and Donald Trump’s court cases that could affect the upcoming US election.” This assertion not only highlights their belief in their ability to influence public discourse but also hints at their awareness of the potential impact on political outcomes.
Moreover, LockBit 4.0 contends that the FBI’s actions were precipitated by stalled negotiations, implying that the agency was keen to prevent the public from learning the true extent of the security breach. They suggest that had it not been for the election context, the FBI would have continued to monitor their servers covertly in pursuit of criminal charges.
Drawing insights from this scenario, LockBit 4.0 advocates for more frequent targeting of government entities, asserting that such attacks expose vulnerabilities and compel law enforcement to reveal their capabilities. They state, “I need to attack the .gov sector more often… it is after such attacks that the FBI will be forced to show me weaknesses and vulnerabilities and make me stronger.” This strategic approach highlights the group’s determination to challenge authority and strengthen its illicit operations by probing and exploiting institutional weaknesses.
Furthermore, the group’s statement reflects a broader strategy of challenging established norms and authority, leveraging their actions to provoke and disrupt law enforcement efforts. By framing the FBI’s actions within the context of impending elections and sensitive legal proceedings, LockBit 4.0 not only seeks to justify its activities but also to undermine the credibility and legitimacy of law enforcement agencies.
In essence, LockBit 4.0’s claims regarding the FBI’s motivations offer a detailed glimpse into the complex interplay between cybercriminals and law enforcement agencies, highlighting the evolving nature of cyber threats and the geopolitical ramifications of their activities. As they continue to navigate this landscape, their strategic insights and calculated responses underscore the enduring relevance of cybersecurity in an increasingly digital world.
Efforts to Enhance Security Measures
LockBit 4.0 discusses their efforts to enhance security measures, such as implementing maximum protection on their ransomware builds to thwart decryption attempts. Their meticulous efforts to enhance security measures, including maximum protection on ransomware builds, showcase a commitment to outmaneuver law enforcement efforts and maintain operational resilience.
As they assert, “in the possible next attack, the FBI will not be able to get a single decryptor for free,” signaling a proactive stance against potential breaches.
Defiant Resilience
Despite facing setbacks and arrests of affiliates, LockBit 4.0 remains resolute in their determination to sustain illicit operations. Their defiance, exemplified by continued activity and publication of stolen data on backup blog domains, underscores an unwavering resolve to withstand law enforcement pressure.
This steadfastness is encapsulated in their assertion that “what doesn’t kill me makes me stronger,” portraying a mindset driven by adversity
Backup Blog Domains and New Affiliates
Furthermore, LockBit 4.0’s response sheds light on their strategic adaptations, such as decentralizing the panel and implementing enhanced encryption measures, to mitigate future risks and reduce the likelihood of successful incursions. By acknowledging vulnerabilities while simultaneously fortifying their infrastructure, they display a nuanced understanding of cybersecurity tactics and a commitment to staying ahead of adversaries.
Moreover, LockBit 4.0’s critique of law enforcement tactics and their skepticism towards the FBI’s claims underscore a perception of themselves as strategic actors within a broader geopolitical landscape. They question the veracity of FBI assertions, highlighting inconsistencies and challenging the narrative propagated by authorities.
What Exactly Happened
Last week, the FBI’s intervention prevented LockBit from releasing sensitive data stolen from government computer systems in Fulton County, GA. However, the group is now regrouping and has issued a deadline of March 2, 2023, for the publication of the stolen data unless a ransom is paid.
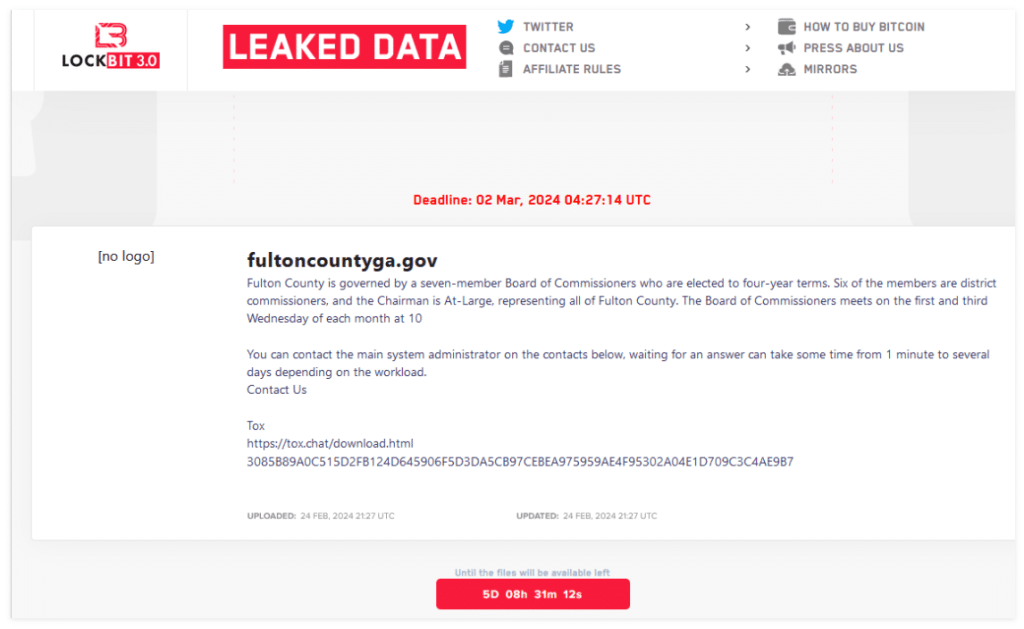
LockBit claims that among the cache of documents is information tied to Fulton County’s criminal prosecution of former President Trump. Court watchers warn that a total leak of the Fulton County data could not only endanger lives but also jeopardize numerous ongoing criminal trials.
The incident in Fulton County dates to early February when leaders acknowledged an intrusion that disrupted phone, email, billing systems, and other county services, including court systems. The LockBit ransomware group subsequently posted a countdown timer on its victim-shaming blog, threatening to publish the data unless a ransom was negotiated by February 16.
However, on that date, the entry for Fulton County was inexplicably removed from LockBit’s site, indicating a possible agreement between the county and the extortionists. Despite this, Fulton County Commission Chairman Robb Pitts emphasized that no payment was made using taxpayer funds.
After careful consideration and weighing many factors last week, the board of commissioners decided we could not in good conscience use Fulton County taxpayer funds to make a payment. We did not pay, nor did anyone pay on our behalf,” said Pitts in the press conference.
In a significant move, just hours before Pitts’ press conference, the FBI and the U.K.’s National Crime Agency seized LockBit’s websites and replaced them with a seizure notice.
This action highlights the collaborative efforts of law enforcement agencies to combat ransomware attacks and disrupt cybercriminal operations.
Despite the setback, LockBit has resumed its malicious activities and has claimed to targeting hospitals and municipalities. The LockBit claimed the cyberattacks on hospitals, including those affiliated with Ernest Health across 13 states.
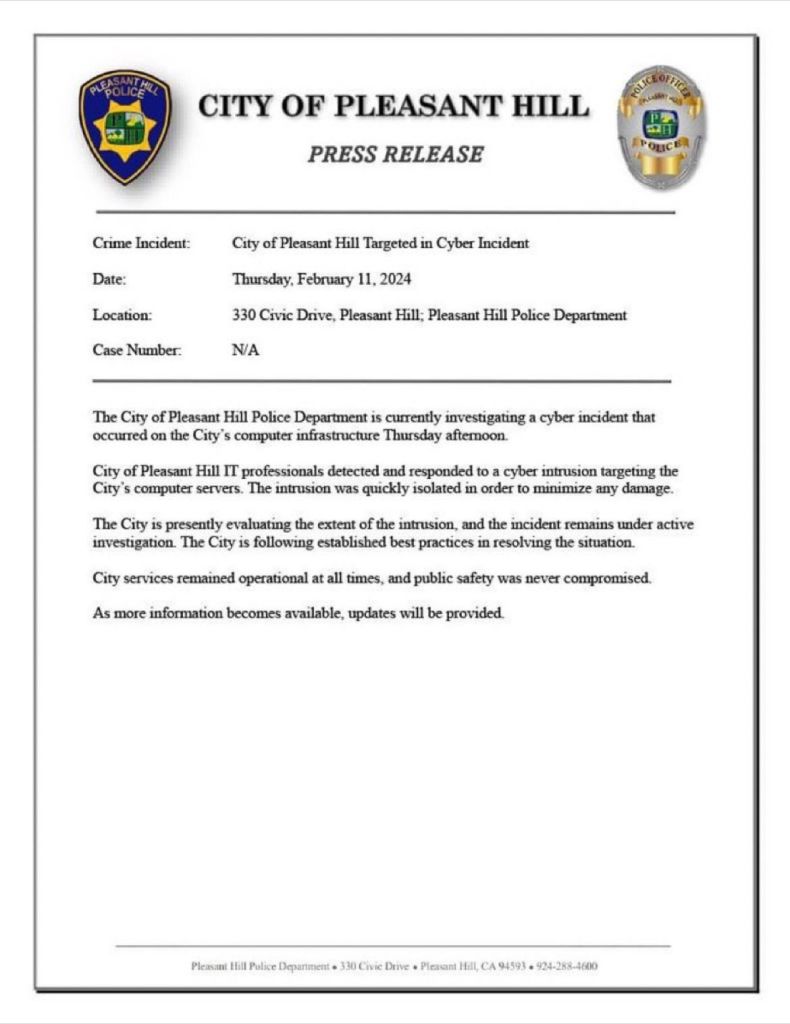
Additionally, the attacks on The City of Oakley and The City of Pleasant Hill, California, along with a private school in New Jersey, underscore the indiscriminate nature of these cyber threats and the urgent need for enhanced cybersecurity measures across all sectors.

Cracking Down on Cybercrime: Arrests and Revelations
The recent arrest of three individuals, including Aleksandr Nenadkevichite Ermakov, alias blade_runner, GustaveDore, or JimJones, marks a significant development in the ongoing battle against cybercrime, particularly within the ransomware landscape. This development comes on the heels of LockBit 4.0’s discussions on enhancing security measures, illustrating the evolving tactics employed by cybercriminals and law enforcement’s efforts to stay ahead of these threats.
Operating under the guise of a legitimate IT firm, Shtazi-IT, these individuals purportedly engaged in a wide array of illicit activities, including the development of custom malware, the creation of phishing sites, and the orchestration of fraudulent schemes across Russia and CIS nations.
The apprehension of Ermakov holds particular significance, given his alleged involvement in the 2022 ransomware attack against Medibank, which resulted in the compromise of sensitive data belonging to millions of customers. Notably, Ermakov’s arrest follows financial sanctions imposed by Australia, the U.K., and the U.S., highlighting the international cooperation and concerted efforts to combat cyber threats.
Moreover, this development sheds light on the increasingly sophisticated tactics employed by cybercriminals, who leverage legitimate fronts to conceal their nefarious activities and evade detection. As authorities continue to crack down on cybercrime networks, this arrest serves as a poignant reminder of the ongoing challenges in safeguarding digital infrastructure and protecting sensitive data from malicious actors.
The Cat-and-Mouse Game of Cyber Warfare
In the world of cyber warfare, a constant conflict takes place between cybercriminals such as LockBit 4.0 and law enforcement organizations. LockBit 4.0’s recent operations emphasize the continuous issues that authorities confront while countering cyber threats.
Despite attempts to interrupt its operations, LockBit 4.0 remains elusive, responding fast to enforcement actions. Their usage of backup blog domains and the recruiting of fresh affiliates demonstrate their capacity to avoid detection.
The LockBit 4.0 saga reveals a story of persistence and flexibility, highlighting the significant challenges that law enforcement authorities face in their efforts to effectively combat cybercrime.
Despite concerted efforts to disrupt its activities, LockBit 4.0 has managed to elude capture, exhibiting an ability to pivot and innovate in response to enforcement actions. The group’s provision of backup blog domains and recruiting of new associates shows its agility, posing a tough challenge to authorities attempting to keep up in the increasing cyber arms race.
The hostile dance between LockBit 4.0 and law enforcement organizations exemplifies the complexities of cyber warfare, in which enemies compete for power in the digital sphere. LockBit 4.0’s capacity to elude detection and alter its techniques underscores the sophistication of modern cyber threats, offering substantial problems to established law enforcement methodologies.
Furthermore, the operations of LockBit 4.0 have far-reaching ramifications for cybersecurity and international cooperation. Their operations cross borders, emphasizing the global character of cybercrime and the importance of international cooperation in combating this ubiquitous danger successfully.
As cybercriminal networks become more sophisticated and interconnected, greater information sharing and coordination across law enforcement agencies is critical to mitigating the expanding risks posed by cyber adversaries.
In a nutshell, the cat-and-mouse game of cyber warfare is a complex and ever-changing conflict that necessitates a detailed grasp of the dynamics at play. Only by focused and joint efforts can we hope to effectively battle cybercriminals’ unrelenting advances and protect the digital future for future generations.
Media Disclaimer: The opinions expressed herein are sourced from VX Underground and social media posts. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.




















































