WordPress vulnerabilities are not a new topic even for The Cyber Express, and even we have listed several articles on the vulnerabilities and even fake campaigns running on the world’s most famous content management system. Researchers from MalwareBytes Labs revealed a few dozen WordPress sites that are backdoored with ad fraud plugins from popunder. But this one is pretty good and is called the Fuser master WordPress plugin.
For context, some people try to gain traffic using illegal and fraudulent means. These individuals buy traffic to their website from a popunder. Popunders are very common online and are usually used to launch a secondary page. They are not malicious but can be used by fraudsters to scam advertisers.
Researchers at MalwareBytes Labs found a few dozen WordPress blogs that were using a similar plug-in that mimics human activity. But these would automatically scroll through a page and follow links while displaying various ads, “all the while a number of ads were being loaded and refreshed. The blogs would only exhibit this invalid traffic behavior when launched from a specific URL created by this plugin, otherwise, they appeared completely legitimate.” This was the key specialty of the Fuser master WordPress plugin.
- The researchers noted that about 50 blogs were found to have been compromised with a Fuser master WordPress plugin.
- In January alone, one of the offending blogs had almost 4 million visits.
- The average visit duration during this period was 24:55 minutes.
- A large ad network was targeting these blogs — the traffic triggered the ad fraud scheme from a popunder, which was being purchased from a different page.
- The plug-in was created with JavaScript code that replicated the actions of real visitors. It automatically followed links and scrolled through a page.
- The Fuser master WordPress plugin detects the mouse movement of real visitors and stops the fake scrolling once that happens.
Fuser master WordPress plugin, a master indeed

The researchers could not find references for the plugin, such as the author or where to download it. They could only find one mention of a WordPress theme detector on themesinfo.com.
The majority of these blogs appear normal when visited directly, which means they would probably pass both human and manual verification. However, when the entry point for the special URL is entered with the associated parameters, it turns the site into an ad fraud hub.
We will focus on how it fakes user activity. The blogs will only display their ad fraud nature after they’ve been visited using the fuser master plug-in’s entry point. This occurs when a user clicks on a page, and a popunder is launched.
The user will be completely unaware of what’s happening as the blog opens in a new window behind the current window.
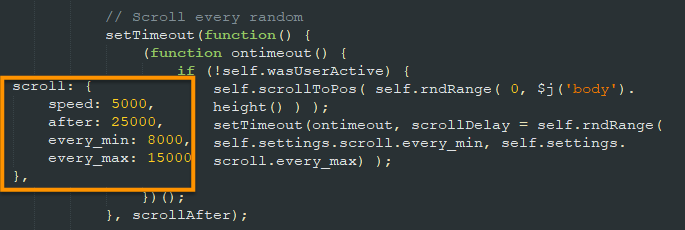
It quickly becomes apparent that something is not right when the popunder is displayed. Scrolling back and forth across the page makes the appearance of a human being doing something similar to what they would do while reading an article. The code in the Fuser master WordPress plugin checks for user activity and only performs this action if it has not been able to detect mouse movement on the page.
And then begins the freezing game, at some point the user will close their browser and the page they were visiting. As soon as that happens the blog will then become static. All of the fake activity on the background will stop.

According to the researchers, this is a clever way to avoid suspicion, similar to the “freeze game” kids play. The fraudsters can then detect when the mouse is placed over the page, and they can prevent the code from running.