The Ministry of Justice in France has reportedly fallen victim to a hacking event. The responsible entity behind the French Ministry of Justice cyber attack goes by the name ‘Garnesia Team,’ adding to the growing list of newly emerged hacktivist collectives.
Despite reports of the security breach at the Ministry of Justice, the website remained accessible.
The Cyber Express reached out to the French Ministry of Justice via email to confirm the security incident. In response, a spokesperson said that the group asserted responsibility for a DDoS-style attack, distinct from ransomware, as no ransom request has been made.
Moreover, no instances have been documented where the functioning of the justice.gouv.fr website was compromised and it continues to operate without issues.
French Ministry of Justice Cyber Attack
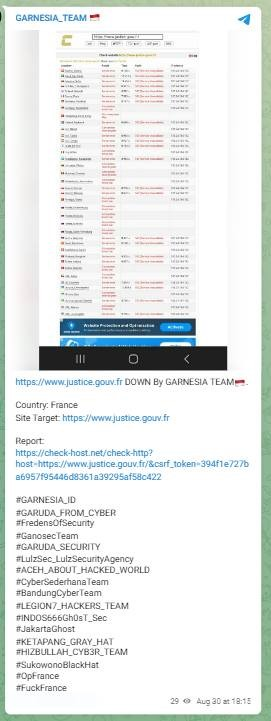
Threat Intelligence platform Falcon Feeds tweeted about the French Ministry of Justice cyber attack. They shared the above screenshot taken from the Telegram announcement of the Garnesia Team.
The security incident is suspected to be a Distributed Denial of Service (DDoS) attack.
A DDoS attack lasts between hours to months depending upon the tools used and the vulnerability of the target. It involves sending several requests to a server, or network that can potentially lead to a system crash because of leaving the infrastructure overwhelmed with the Internet traffic sent using botnets.
The network resources may remain unavailable to users wanting to use them after a successful DDoS attack.
Garnesia Team Posts About the French Ministry of Justice Cyber Attack
“https://www.justice.gouv.fr DOWN By Garnesia Team,” wrote the hackers on their Telegram page. They placed a checkhost link in the message to look for the accessibility of the targeted website.
The post also listed some of the hacker groups’ names associated with the DDoS attack on the French Ministry of Justice, who align themselves with the cybercriminal’s mission and appear to be working in collaboration.
There’s a possibility that they might have even assisted in orchestrating the cyber attack. The list includes the following names:
- Garuda from Cyber
- Fredens of Security
- Ganosec Team
- Garuda Security
- LulzSecurity Agency
- ACEH About Hacked World
- Cyber Sederhana Team
- Bandung Cyber Team
- Legion7 Hackers Team
- Indos 666 Ghost Sec
Defacement Attacks by Garnesia ID
The name of the hackers included Garnesia_ID which when investigated by The Cyber Express led to startling results.
The following two websites in India were defaced by a group of hacktivists including Garnesia_ID who claimed to be fighting for their ‘brothers in India’–
- Netaji Subhas Chandra Bose Cancer Research Institute – https://nscri.in
- Home Remedy – http://www.homeremedy.in
The following screenshots were captured from the website after the NSCRI defacement attack –
The attack was claimed by ‘XizB3f’ who sought Muslims to be treated properly in India. “Stop playing with my religion,” they stated in the message on the NSCRI website. The targeted website is of a cancer hospital in India.
The following screenshots were captured from the Homeremedy defacement attack –
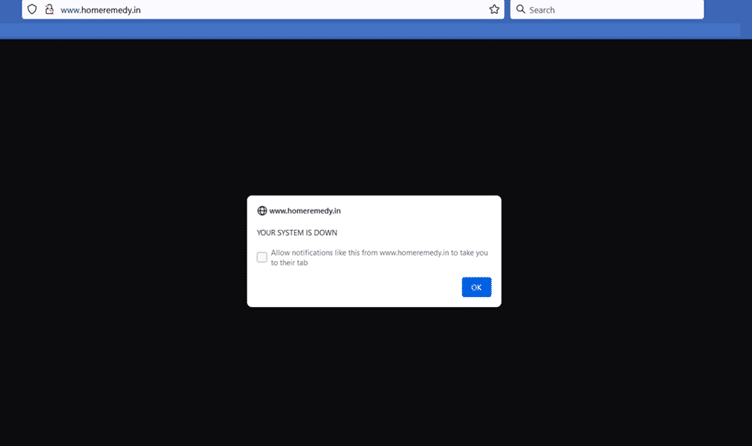
Home remedy is also an Indian website that offers information about plants and healthy living among others.
The website showed a message stating that the system was down. Upon clicking on OK reflecting in the popup, the hackers’ message displayed –
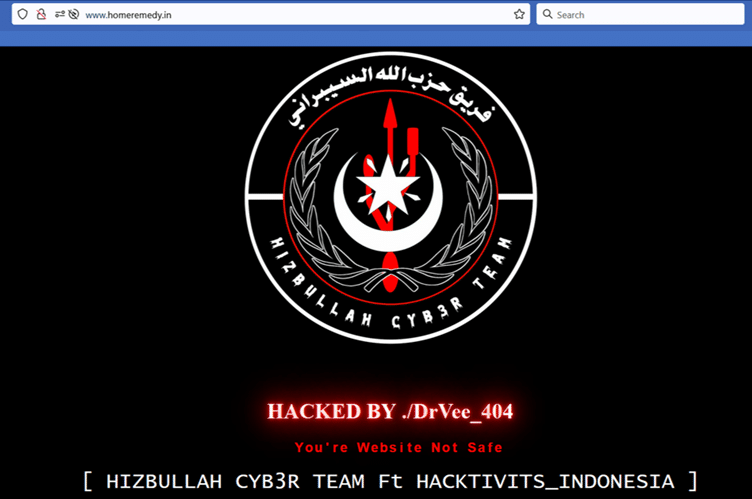
The homeremedy defacement attack was claimed by a hacker named DrVee_404. The hackers included hacktivists from Indonesia. The list of hacktivists noted in the list included Garnesia_ID.

“Happy 78th year of Indonesia and Happy Independence Day to my brothers (in) Pakistan,” read the message on the defaced website of Home Remedy.
They made derogatory comments about India for oppressing Muslims – “We Indonesian hackers will not hesitate to destroy your website.”
A list of hacking groups was mentioned with the threat to Indian people. It is not clear when the defacement attacks were launched. The Google search results displayed that the websites were hacked.
The home pages of both websites remained defaced with messages from the hackers. While other pages within the websites were accessible and were not impacted by the cyber attack.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.



















































