Cybercriminals have been aiming their efforts at students seeking laptops or scholarships, employing targeted strategies to deceive them.
Among these schemes, researchers have identified free giveaway scams designed to appear genuine to students. Cybersecurity company Kaspersky has uncovered these frauds, including the deceitful free laptop scams, as part of their ongoing efforts.
Free Laptop Scam for Students
Students often become vulnerable targets due to their ongoing need for school supplies, which can deteriorate over extended use. This combination of necessity and financial constraints can lead some students to explore offers and prizes promoted on various websites.
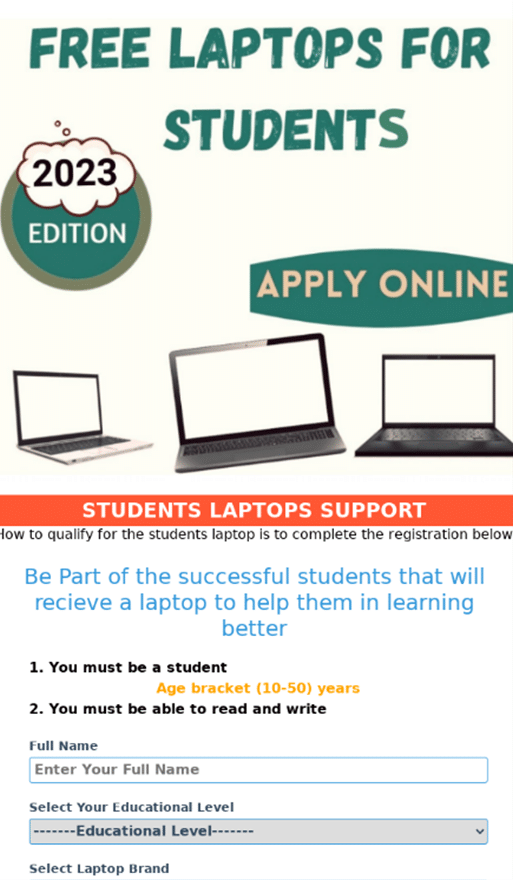
Cybersecurity researchers observed a scheme involving students, where a free laptop scam prompted them to select their preferred laptop model, serving as bait. Additionally, students were prompted to disclose their personal information.
The giveaway scam’s telltale sign of being a fraud was its requirement for students to pay for prize delivery. To do this, all the sensitive financial information the scammers need would be shared with them.
Other Student Scams and Monetary Frauds
In other back-to-school scams targeting students, it was found that scammers urged pupils to involve 15 others in the scheme via WhatsApp.

“In another version of this scam, individuals are prompted to share a specific link leading to a page with a prize-draw with 15 contacts through WhatsApp. Subsequently, they are required to engage in the draw by registering via SMS” Kaspersky noted in its press release.
Some schemes asked for registration via SMS exposing the messaging service of students to scammers.
Commenting on the urgent need to stay safe online, Olga Svistunova, a security expert at Kaspersky said, “As the academic season looms and millions of students purchase books, make tuition payments, and acquire school supplies, there is a traditional surge in cyber threats.”
There have been scams about fraudulent scholarship schemes for students where they are offered student aid. Students looking for monetary assistance are promised financial aid by fraudsters.
To avail of the benefits, students’ Social Security numbers, bank account details, and other personal information are asked for.
Providing such student information could allow scammers to create fraudulent documents in the child’s name and seek benefits from organizations. They can also create fake ID cards that can lead to identity theft among other security threats.
“It’s crucial for students to remain vigilant and cautious when interacting with unfamiliar scholarship offers,” Olga Svistunova concluded.
It is also essential to not trust offers and freebies that appear too good to be true. It is expected of students and guardians to take such matters to the police to trace the scammers and stop them before they target others.
Moreover, students must also consult with elders and teachers and regularly read cybersecurity news to be aware of similar student frauds. The local police websites and cyber agencies offer insights into the latest online threats which could help identify fraudulent communications received by the target.
“To protect our children and educators, we must ensure the schools they attend and work in are safe and secure,” the Secretary of Homeland Security Alejandro N. Mayorkas said in a press release by the US Department of Health and Human Services.
To further the cause of student data safety, governments across nations have offered several resources one of which is the latest website – https://www.schoolsafety.gov/
Essential Tips for Student Security
The following observations can help create awareness among students about fraudulent school scams –
- Offer made too easy – Often fraudulent schemes including the free laptop scam for students have easy-looking advertisements to make them seem accessible to the target. The fraudulent activity unfolds when users are asked to click on links, download forms or any other media, and fill in their information to avail the prize.
- Credential checking – Often scammers do not put in all the effort in creating all that is necessary to appear genuine. Hence it would help to specifically look for the company name in search results, and see if the website pages have details on them instead of being blank or inaccessible.
- Social media check – It is common for genuine organizations to have a social media presence. The absence of the same could mean they have not created enough resources let alone have a legitimate or free laptop for students. Check all their Facebook, Instagram, Twitter, etc., pages.
- Source of scheme – Most schemes for students are found on school websites, government websites, and other old and credible websites of known enterprises that offer prizes as part of their social responsibility.
The onus is now on students and their guardians to utilize the information on cybersecurity and make use of the contact and details about cybersecurity mentioned herewith.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.