The threat actor group known as NoName has claimed responsibility for targeting multiple websites in Italy.
The affected entities in the cyberattack on Italy, include prominent institutions such as Sinfomar, Guardia di Finanza, the National Commission for Companies and the Stock Exchange, Autorita’ Garante della Concorrenza e del Mercato, Torinese Transport Group, CTM SpA, Trentino Transport, and the Marina Militare.
Motive Behind Cyberattack on Italy
The message disseminated by the threat actor group suggests a political motive behind the Cyberattack on Italy.
It references agreements between Italy, the European Bank for Reconstruction and Development, and the Ukrainian government aimed at supporting the energy sector of Ukraine.
The threat actor accuses Italy of diverting resources towards supporting “Bandera’s supporters” instead of focusing on its citizens’ welfare.

The message further criticizes the Italian Foreign Ministry’s reported intention to sponsor President Zelensky’s administration, labeling them as “terrorists.” The threat actor group expresses frustration with Italy’s perceived lack of understanding of their intentions and demands, escalating their actions by launching another wave of Distributed Denial of Service (DDoS) attacks against targeted websites.

The tone of the message suggests a significant level of coordination and planning by the threat actor group, with a clear intent to disrupt Italy’s internet infrastructure and cause economic harm. By targeting key governmental and financial institutions, NoName aims to highlight their grievances and potentially exert pressure on Italian authorities.
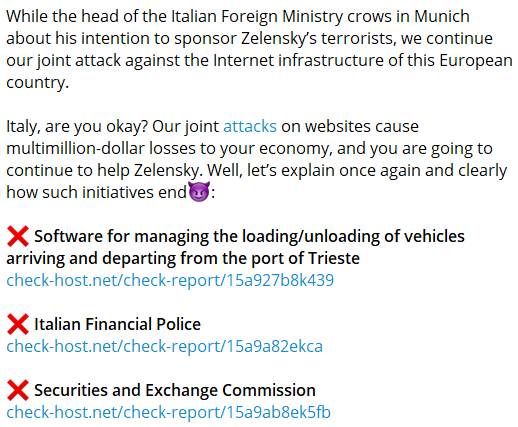
The reference to “joint attacks” implies potential collaboration with other threat actor groups, raising concerns about the scale and sophistication of the cyber threat landscape facing Italy and potentially other European countries. The message serves as a reminder of the vulnerability of digital infrastructure to malicious actors and the need for enhanced cybersecurity measures to mitigate such risks effectively.
The implications of a cyberattack on Italy extend beyond the immediate disruption caused to targeted websites. They highlight broader geopolitical tensions and the evolving nature of cyber warfare, where state-sponsored or politically motivated threat actors leverage digital tools to advance their agendas and exert influence on the global stage.
NoName Previous Cyberattack
This recent cyberattack on Italian websites follows a pattern of aggressive cyber activities attributed to the NoName group. In January, the group claimed responsibility for a sophisticated cyberattack on multiple high-profile websites in the Netherlands, including OV-chipkaart, the Municipality of Vlaardingen, the Dutch Tax Office (Belastingdienst), and GVB.
The sensitive nature of the information held by these entities raised significant concerns about data security and the potential impact on public services.
The January cyberattack was not an isolated incident. NoName has been linked to a series of cyberattacks across Ukraine, Finland, and the USA earlier in 2024. The group’s dark web channel specifically named eight organizations as victims, indicating a coordinated and widespread cyber offensive.
The organizations targeted in the prior attack included PrivatBank 24, Credit Agricole Bank, MTB BANK, Accordbank, Matek Systems (China), Pixhawk (Switzerland), SpetsInTech, and Kvertus.
These cyberattack incidents highlight the global reach and disruptive capabilities of the NoName group, posing significant challenges to cybersecurity efforts worldwide.






















































