Cyber attacks on Malaysia by Indian fringe groups continue. In an operation named #OP_PAYBACK_MALAY, a group of Indian hackers have allegedly targeted the Energy Commission of Malaysia.
The Energy Commission of Malaysia breach was announced on Twitter by the admin and hackers of the group Kerala Cyber Xtractors (KCX). The group has been targeting Malaysian entities to take revenge for attacks on Indian websites.
Speaking about the Energy Commission of Malaysia breach, the KCX tweeted: “Energy Commission of Malaysia taken down for straight 1 hours by Kerala Cyber Xtractors….” It was likely a DDoS attack going by the hashtags on the tweet.
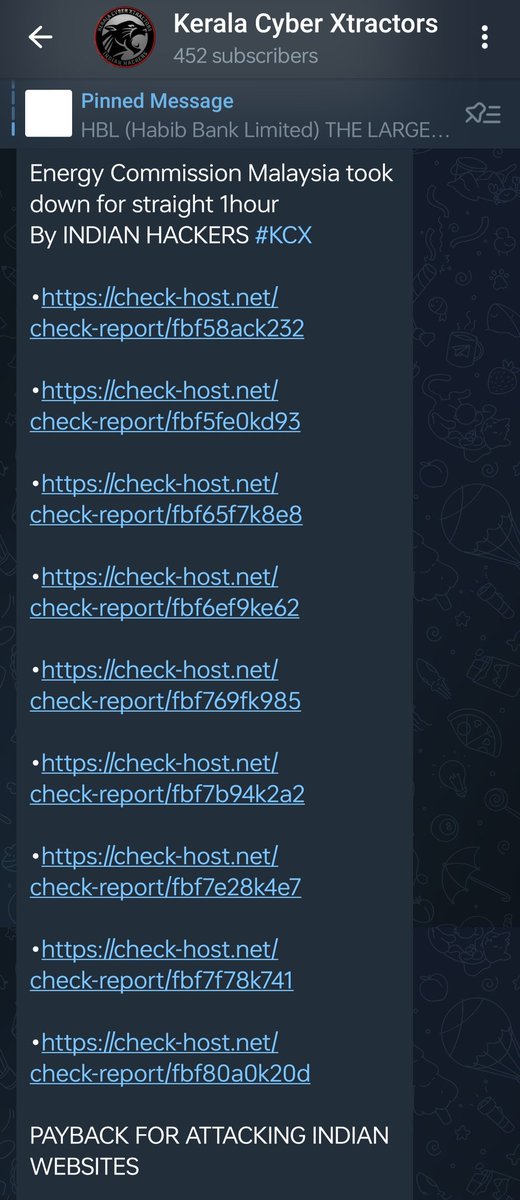
Cyber attacks on Malaysia by Kerala Cyber Xtractors
This is the latest instance of cyber attacks on Malaysia by Kerala Cyber Xtractors. The Cyber Express last week reported about the hacker group claiming responsibility for the cyber attack on Malaysia’s central bank.
Kerala Cyber Xtractors tweeted, claiming to take down the Malaysian Central Bank, on April 26. The bank’s website was inaccessible for two hours, the group claimed.
The KCX also targeted a leading payment gateway in Malaysia. They claimed that the website ipay88.com was down for 30 minutes, according to a tweet on April 30.
The Malaysian Central Bank disclosed that it has suffered a cyber attack, which resulted in unauthorized access to a third-party service provider’s computer systems. The bank assured that it has been working with relevant authorities to investigate the incident.
The central bank has assured its customers that there was no disruption to its services and that its own systems were not compromised. However, the bank has advised its customers to remain vigilant and report any suspicious activity related to their accounts.
The bank has not disclosed the identity of the third-party service provider, nor the extent of the data breach. However, it has stated that it is taking all necessary measures to strengthen its security systems and prevent any further unauthorized access.
Cyber attacks on Malaysia and blown-up hitlists
Kerala Cyber Xtractors also listed the Civil Aviation Authority of Malaysia as a target in a Facebook status. The hacker group has claimed to have halted the website of the Energy Commission of Malaysia post the alleged breach.
However, The Cyber Express is yet to confirm the veracity of these claims. The websites of both organisations were fully functional at the time of publishing this news report.
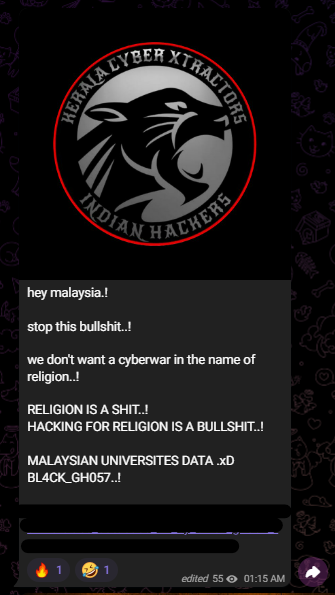
Kerala Cyber Xtractors have also allegedly targeted Malaysian educational institutes. SQL files with names, email addresses, and passwords were stolen by the group.
A captured screenshot of the cyberattack claim on Malaysian universities read, “We don’t want a cyberwar in the name of religion…!” The group said that they denied hacking in the name of religion, and went ahead with the cyberattack.
Kerala Cyber Xtractors and hacktivism
The Facebook page of Kerala Cyber Xtractors calls it a non-governmental organization. Kerala Cyber Xtractors is the latest example of fringe groups popping up in the guise of hacktivism, as reported by The Cyber Express last month.
There has been a rise in hacktivism in India, with several groups emerging to voice their concerns and protest against various social and political issues. However, many of these groups have also faced crackdowns and arrests by authorities.
Hacktivism refers to the use of hacking and cyber attacks as a means of political activism or protest. In India, hacktivist groups have targeted a range of issues, including corruption, censorship, and human rights violations.
One of the most prominent hacktivist groups in India is Anonymous India, which has carried out several high-profile attacks against government and corporate targets.
However, the group has also faced arrests and crackdowns by authorities, with several members being charged with cybercrime offenses.
Other hacktivist groups in India, such as Kerala Cyber Xtractors, have also carried out attacks against various targets, but they have not received as much attention as Anonymous India.




















































