The BlackByte ransomware group has claimed responsibility for the cyber attack on the City of Augusta, ending days of speculation and countering the administration’s claim of a “cyber incident”.
BlackByte, known for targeting critical infrastructure sectors in the United States such as government facilities, financial institutions, and food and agriculture, listed Augusta on its data leak site late on 25 May.
According to the post, the ransomware-as-a-service gang has stolen approximately 10GB of sensitive data.
“We have lots of sensitive data, Many people would like to see that as well as the media. You were given time to ‘connect us but seems like you are sleepy. We will help you to wake up,” said the BlackByte leak site post.
“Here is a leak of 10GB of your data and very soon there will be much mare free to everyone.”
The information posted is yet to be verified. The Mayor is expected to announce an update on the cyber attack on the City of Augusta on Friday, 26 May, The Resister reported.
The cyber attack on the City of Augusta: Timeline
Augusta city officials confirmed an “unauthorized access” to the city’s computer systems, FOX54 reported on 23 May.
Mayor Garnett Johnson, along with commissioners and the city attorney, addressed the incident and assured the public that the Information Technology (IT) department is actively working to resolve the issue.
The officials then emphasized that an investigation is underway to determine the source of the attack, but said could not confirm whether any sensitive data was compromised.
Later Mayor Garnett Johnson said a statement posted on the city’s website on 24 March, acknowledged a “network outage” that began on Sunday, May 21, causing disruptions to some of the city’s computer systems.
An investigation revealed unauthorized access to the system, prompting the Information Technology Department to work diligently to assess the incident’s impact, restore functionality, and investigate any potential data theft.
The FBI was investigating the cyber attack on the City of Augusta, FOX54 reported on 24 May.
The cyber attack on the City of Augusta: The list goes on
“Ransomware continued to be a significant challenge for subnational governments and adjacent entities,” noted an Emisoft report on the US ransomware attacks in 2022.
Dallas (Royal ransomware), Modesto (Snatch extortion group), Lakewood (ALPHV/BlackCat ransomware), Collegedale (BlackByte ransomware group), and Oakland (Play ransomware), were among the few incidents The Cyber Express reported this year.
The number of ransomware attacks targeting state or municipal governments and agencies increased in 2022, with 106 reported incidents. This marks a significant rise from the 77 attacks recorded in 2021, said the report.
Notably, the figures for this year were heavily influenced by a single incident in Miller County, AR, where a compromised mainframe resulted in the spread of malware to endpoints in 55 different counties.
This incident had a substantial impact on the overall statistics for the year.
“Data was stolen in at least 27 of the 106 incidents (25 percent). However, if the 55-county incident in Arkansas is disregarded, that increases to 53 percent. In 2021, data was stolen in 36 of 77 incidents (47 percent),” the report said.
BlackByte ransomware group and government bodies
BlackByte ransomware has been making waves in the cybersecurity landscape since its discovery in the summer of 2021. Over time, it has spawned numerous variants, with the latest ones surfacing in recent months.
Operating as a Ransomware-as-a-Service (RaaS) model, BlackByte employs a highly effective double extortion technique that combines data exfiltration and encryption to maximize the impact on victims, noted the BlackBerry Research & Intelligence Team
The double extortion approach adopted by BlackByte enables threat actors to not only encrypt victims’ data but also exfiltrate it beforehand, noted the report.
This dual tactic provides them with additional leverage when demanding ransom payments, as they can threaten to expose or sell sensitive information on the dark web if their demands are not met.
“In addition, recent BlackByte operators have been spotted leveraging a custom exfiltration tool which has been dubbed ‘ExByte’ in order to steal the victims’ data, pre-encryption. Once exfiltrated, the stolen files are uploaded to the Mega cloud storage service,” the report said.
Like many modern ransomware strains, BlackByte utilizes legitimate tools, known as living-off-the-land binaries, to blend in with normal system activity, noted a threat assessment report by Trend Micro.
The researchers spotted a recent spike in the ransomware gang’s targets in the government and local administration sector.
“Up to the end of April 2022, the technology sector saw the most BlackByte detections, however, in May, detections in the government sector also shot up,” the report said.
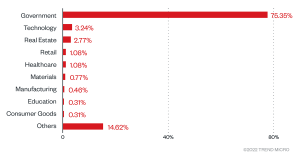
“One way to interpret these observations is that the drastic increase stemmed from a single attack that affected several machines,” said the report.
“Aside from the reports on ransomware groups targeting Latin America, this explanation is also based on the report that, by their own claim, BlackByte operators had compromised a Peruvian government entity around the time of the increased activity.”
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.






















































