Lockheed Martin, an international aerospace, arms, defense, and information security corporation is the latest victim of the Killnet ransomware group.
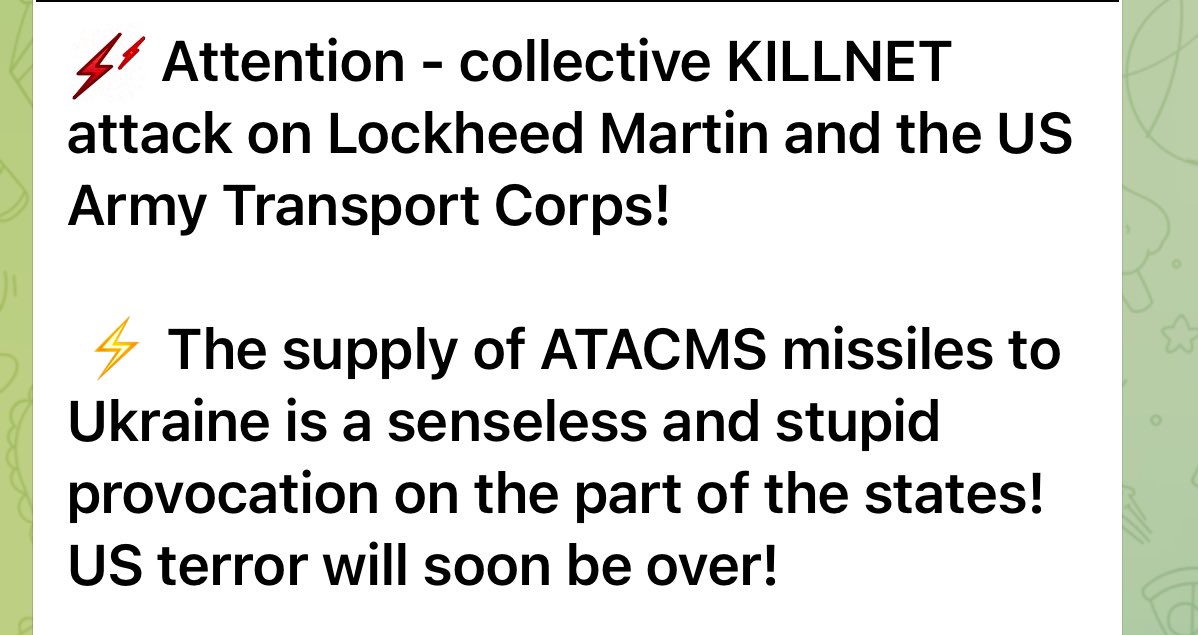
The Russian hacktivist group named not one but two U.S. organizations in a Telegram message. They named the Army Transport Corps alongside the claim of cyber attack on Lockheed Martin.
Army Transportation Corps is a combat service of the United States Army that helps deliver infrastructure and personnel.
Cyber Attack on Lockheed Martin
The Russian hacktivist Telegram channel’s message read, “The supply of ATACMS missiles to Ukraine is a senseless and stupid provocation on the part of the states!”
This threat was addressing the decision made by the Biden administration to bring the Ukrainian army the long-range ATACMS missiles.
These missiles boast of the power to launch multiple cluster attacks in place of slow single counterparts.
This could considerably strengthen Ukraine in its ongoing war against Russia.
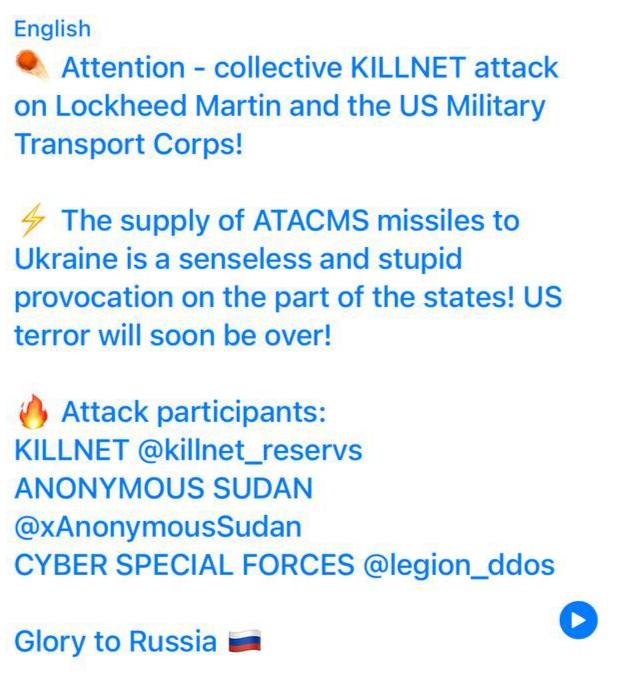
The hackers who claimed to launch the cyber attack on Lockheed Martin are supported by others hacktivists. This includes Anonymous Sudan and Cyber Special Forces.
The website of Lockheed martin was accessible when checked by The Cyber Express team. We emailed the organization for comments regarding the cyber attack on Lockheed Martin. We will update his report upon receiving their response.
Cyber Attacks on United States Digital Infrastructure
In another cyber attack incident, the hacker group 8Base named two U.S. websites to its victim list.
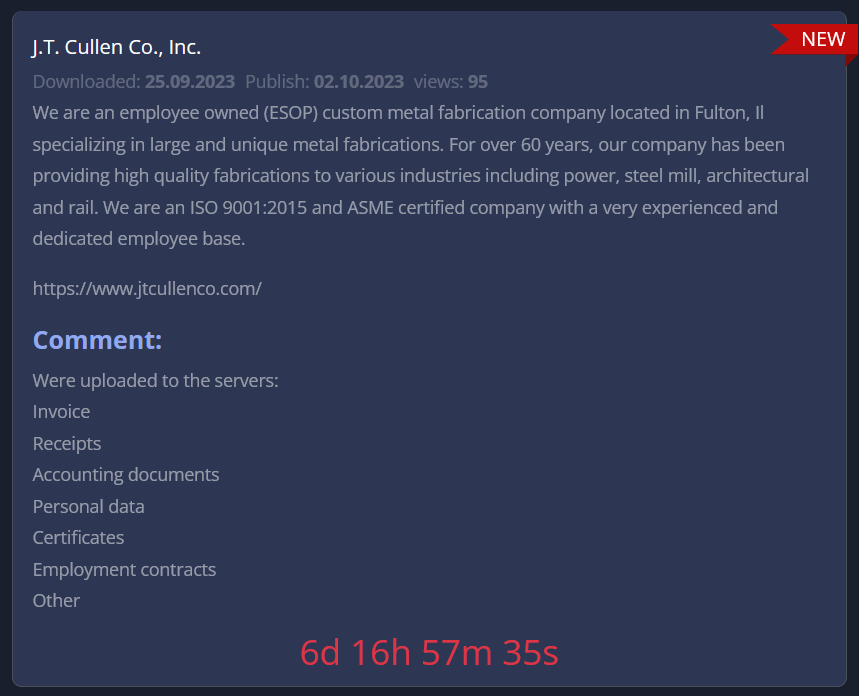
Springer Eubank Company and J.T. Cullen Co, Inc. were among the targets of the 8Base ransomware group.
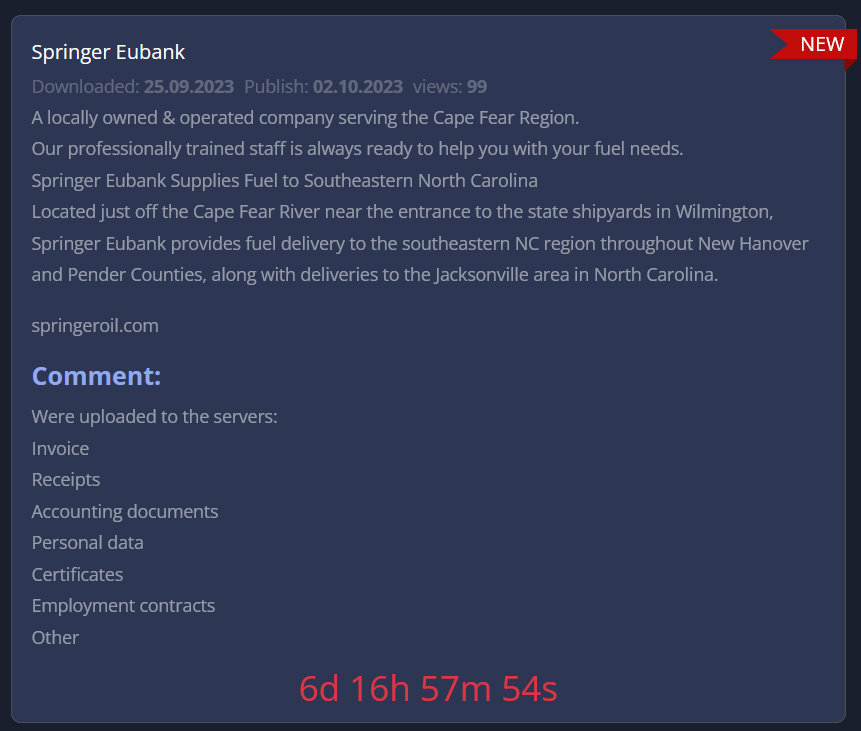
The dark web post by the group claimed that they exfiltrated among other data invoices, receipts, accounting documents, and employment contracts after the Springer Eubank ransomware attack.
The cyber attack threat concluded with a ransom payment deadline of 6 days 16 hrs and 57 mins being given to the organization.
Springer Oil Co. is located in Connecticut and offers home heating oil, and burner services among others.
The J.T. Cullen ransomware attack message by 8Base had the same deadline and details about the database stolen in the cyber incident. J.T. Cullen Co., Inc. is a metal fabrication firm based in the United States.
About Killnet Group Behind the Cyber Attack on Lockheed Martin
In an advisory, the Health Sector Cybersecurity Coordination Center (HC3) alerted about the Killnet hacktivist group. They have wreaked havoc on the U.S. healthcare industry, the note read.
Active since 2022, Killnet often launches Distributed Denial of Service attacks on countries supporting Ukraine in the Russia-Ukraine war.
Almost all NATO countries were attacked by not just Killnet, but other pro-Russian groups as well for various missions.
“Killmilk, a senior member of the KillNet group, has threatened the U.S. Congress with the sale of the health and personal data of the American people because of the Ukraine policy of the U.S. Congress,” the alert further added.
“NoName057(16), also known as NoName05716, 05716nnm or Nnm05716, is a relatively underreported hacktivist group supporting Russia since March 2022, alongside Killnet and other pro-Russian groups,” a Sentinel One report stated.
Hackers have been using Telegram channels to announce victims based on their mission or geopolitical tensions, supporting one nation in the Russia-Ukraine war.
The police have been suspending accounts of ransomware and hacktivist groups’ social media accounts.
The Twitter account of a subgroup of LockBit ransomware group was taken down, reported VX-Underground.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.