In the aftermath of the CrowdStrike and Microsoft outage that crippled critical infrastructure worldwide—impacting airports, hospitals, schools, and government offices—the role of security experts has been thrust into the spotlight once more. Chief Information Security Officers (CISOs) and Chief Technology Officers (CTOs) are facing heightened responsibilities in safeguarding networks against an increasingly sophisticated range of cyber threats originating from the dark web.
Telecom networks, crucial for global communication, have emerged as prime targets due to the vast volumes of sensitive data they manage. Cybersecurity experts assert that telecom networks are particularly attractive to cybercriminals because they store extensive personal and financial information, thereby exposing them to serious risks such as malware, phishing, and ransomware attacks.
With the rise of hacktivist groups, ransomware gangs, and lone hackers, The Cyber Express offers effective CTO strategies for dark web threats. This easy-to-follow guide helps CTOs tackle the daily challenges of mitigating these digital adversaries.
Telecom Network Security: Challenges and Solutions
Securing telecom networks against hackers is an important part of CTO strategies for dark web threats. The industry faces numerous challenges, including the inherent complexity of telecom infrastructures themselves.
These infrastructures, characterized by interconnected systems and diverse technologies, necessitate comprehensive security measures to effectively cover every component. Notably, ransomware affected 72.7% of organizations globally in 2023, reported Statista, further highlighting the pervasive threat across diverse sectors.
The first challenge lies in the complexity of telecom infrastructures themselves. Interconnected systems and diverse technologies necessitate comprehensive security measures to cover every component effectively. This complexity heightens the difficulty of ensuring robust security across the entire network architecture.
Moreover, rapid technological advancements such as 5G deployment and IoT proliferation expand the attack surface, demanding enhanced mitigation strategies. Concurrently, phishing remains the most common email attack method, accounting for 39.6% of all email threats, as per data by Hornetsecurity’s Cyber Security Report 2024. Spear phishing attachments were used in 62% of these attacks, highlighting the need for targeted defenses, reported IBM X-Force Threat Intelligence Index 2024.
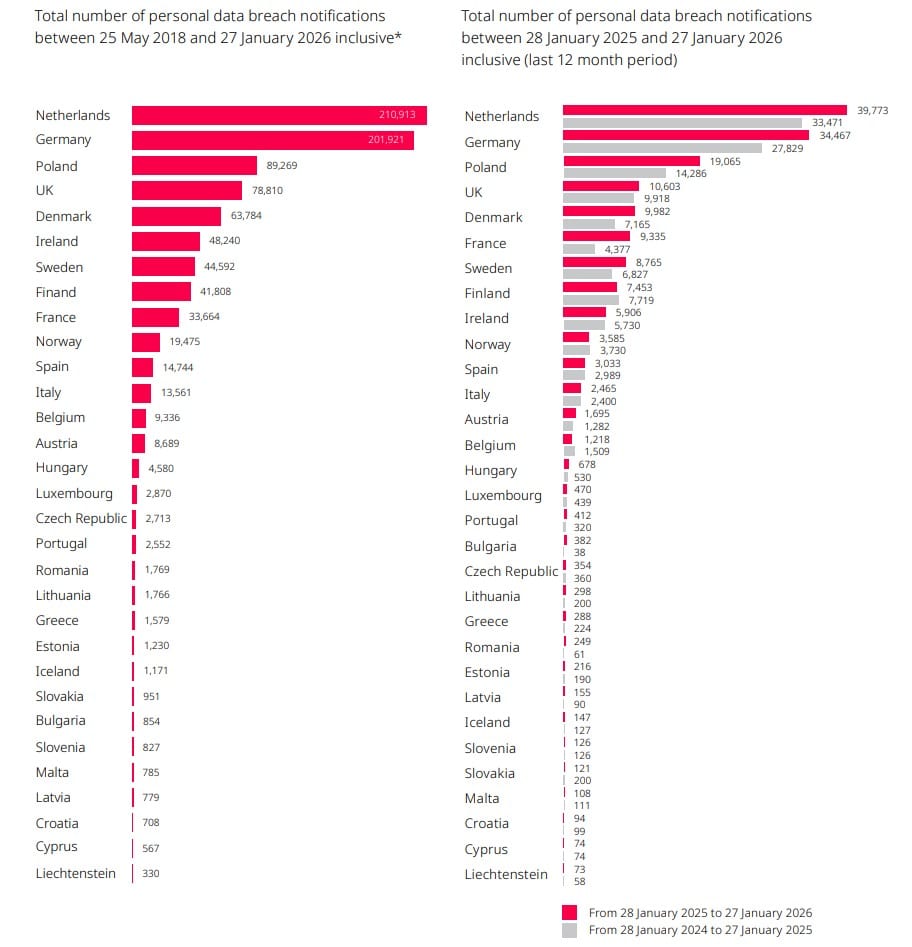
Another critical challenge for telecom companies is regulatory compliance. Meeting diverse regulatory requirements across regions, such as GDPR and PCI DSS, adds complexity to security operations. Strict adherence to these standards is essential not only to avoid legal repercussions but also to maintain trust with customers who expect their data to be protected according to established guidelines.
Resource constraints pose yet another obstacle. Budget limitations often restrict the implementation of comprehensive security measures. Therefore, telecom companies must prioritize their security needs and allocate resources efficiently to achieve the best possible security posture within their financial constraints.
Best CTO Strategies for Dark Web Threats in 2024
Implementing effective strategies to counter cybercriminals is crucial for CTO strategies for dark web threats aiming to bolster security posture and foster a conducive business environment. One key strategy is leveraging artificial intelligence (AI) for immediate threat detection. Cybersecurity firms like Cyble provide specialized dark web monitoring services and threat monitoring services designed specifically to mitigate risk associated with the dark web. These solutions include ongoing scanning, instant alerts, and expert evaluation of potential threats.
Studies indicate that bad actors increasingly leverage generative AI, attributing an 85% rise in cyberattacks to its use, said CFO. By analyzing extensive datasets, AI can swiftly identify anomalies indicative of potential malicious activities, enabling proactive threat response.
Another critical area is securing the supply chain, particularly AI algorithms and data used for training AI models. Ensuring the integrity of third-party components is vital to prevent vulnerabilities that could compromise network security. Partnering with trusted vendors and enforcing stringent security protocols can effectively mitigate risks associated with supply chain vulnerabilities, thereby fortifying the telecom infrastructure against external threats.
Continuous monitoring plays a pivotal role in maintaining cybersecurity defenses. Automated monitoring systems provide real-time detection of suspicious activities, allowing telecom companies to promptly address emerging threats before they escalate. This proactive stance minimizes potential damages and reinforces network security, further promoting CTO strategies for dark web threats.
Enhancing employee awareness through comprehensive training programs is equally essential. Educating staff on identifying and mitigating cybersecurity risks specific to telecom networks and AI technologies helps cultivate a culture of security awareness. Notably, human error contributes to 74% of all breaches, emphasizing the need for proactive employee education and vigilance.
Krzysztof Olejniczak, Chief Information Security Officer (CISO) at STX Next, highlighted the crucial role that employee awareness and readiness play in mitigating cyber risks. “Data from our recent survey highlights that employees continue to be the weakest link in company security. Even with robust technological measures in place, ineffective implementation, inadequate support processes, or a lack of governance can undermine these efforts,” noted Olejniczak.
Adhering to regulatory standards such as GDPR and PCI DSS is non-negotiable for telecom companies aiming to uphold robust data protection practices. In 2023, fines under the General Data Protection Regulation (GDPR) in the EU reached approximately €2.1 billion, marking a substantial increase compared to previous years. The surge was driven by a landmark €1.2 billion penalty against Meta for improper data transfers to the U.S. Despite fluctuations, average fines have risen significantly since 2019, with notable penalties levied against Meta, Amazon, and Google, including a €746 million fine on Amazon in 2021.
By aligning with industry regulations, telecom companies demonstrate their commitment to safeguarding customer data and avoiding penalties linked to non-compliance. Ultimately, investing in cybersecurity initiatives is a pathway to profitability for telecom companies. This investment yields multiple benefits, including cost reduction from mitigating data breaches and operational disruptions, enhancing customer trust and loyalty, and creating new revenue streams through managed security services.
To optimize the effectiveness of CTO strategies for dark web threats, security officers must prioritize advanced security frameworks, harness AI-driven threat detection capabilities, and foster a pervasive culture of cybersecurity awareness.
The Role of Cybersecurity Framework
Frameworks such as ISO 27001 and the NIST Cybersecurity Framework offer structured approaches that telecom companies can adopt to bolster their cybersecurity measures. ISO 27001 emphasizes the management of information security risks, ensuring the confidentiality, integrity, and availability of sensitive data through a systematic approach. This framework provides a robust foundation for safeguarding critical information assets against potential threats.
On the other hand, the NIST Cybersecurity Framework provides guidelines tailored to identify, protect, detect, respond to, and recover from cybersecurity incidents. By following these guidelines, telecom companies can enhance their overall resilience against evolving cyber threats. The NIST Cybersecurity Framework aids in establishing a comprehensive cybersecurity strategy that addresses the specific challenges and risks faced within the telecommunications industry.
As telecom networks evolve, another crucial aspect of CTO strategies for dark web threats involves proactively investing in advanced security technologies. This includes leveraging artificial intelligence (AI) for threat detection and response capabilities to stay ahead of sophisticated cyber threats. Moreover, fostering a culture of cybersecurity awareness linked with security frameworks is crucial in mitigating human error, which remains a common vulnerability exploited by cyber attackers.
Understanding Dark Web Threats
The telecom industry faces a formidable challenge from dark web threats, which exploit the anonymity and encrypted nature of underground networks. Unlike the surface web, the dark web operates beyond conventional search engines, facilitating illicit activities such as the sale of stolen data, hacking tools, and specialized services aimed at exploiting vulnerabilities in telecom networks.
Dark web marketplaces serve as hubs for cybercriminals to trade sensitive information relevant to the telecom sector. This includes compromised customer data, login credentials, and insider details about critical network infrastructure. The availability of such data on the dark web poses a significant risk to telecom companies, potentially leading to identity theft, financial fraud, and targeted cyber attacks against subscribers and infrastructure.
A pressing concern for telecom security is the trade of telecom-specific vulnerabilities and exploits on the dark web. These include zero-day vulnerabilities in network equipment, malware crafted to compromise telecom networks, and tools enabling unauthorized access to subscriber data. The commodification of these threats highlights the urgent need for robust cybersecurity measures within the telecom industry to mitigate sophisticated cyber risks lurking in the shadows of the internet.
For robust protection against dark web threats and to safeguard your telecom infrastructure, Cyble offers advanced cybersecurity solutions tailored to your needs. Leverage Cyble’s AI-driven analysis and continuous threat monitoring to gain critical insights and enhance your organization’s defense. Take proactive steps with Cyble’s comprehensive cybersecurity services to mitigate risks and secure your digital ecosystem effectively.
Discover more by scheduling a demo today!