Since the end of November, when OpenAI debuted the wildly popular ChatGPT, observers on all sides have been concerned about the impact AI-driven content creation would have, particularly in the field of cybersecurity. Indeed, many experts are afraid that generative AI solutions would make crimes more accessible.
While security teams can use ChatGPT for defensive applications like as code testing, getting the solution right is not always easy, says Patrick Garrity, VP of Marketing at Nucleus Security.
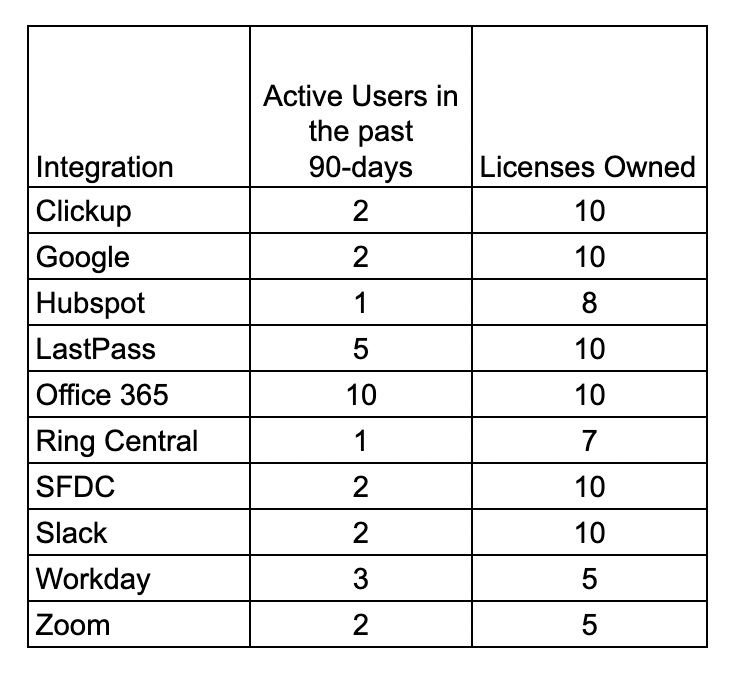
As part of his Hoodwink project, he tried to use ChatGPT to get a list of active users for an organizations SaaS apps that could help identify user licenses that go unused. The journey was equally impressive as the results, he told The Cyber Express.
Necessity, curiosity, invention
“Hoodwink is a weekend project I created to explore ChatGPT. The scripts created from the project generate a list that allows organizations to better understand and rightsize their SaaS licensing and security needs,” he said.
A week ago, he received a rather excessive bill from a SaaS app for additional user licenses that felt excessive. That got him thinking about a quick way to get a list of active users for an organization’s SaaS apps that could help identify user licenses that go unused.
“I asked several friends across the technology community and seemingly no one could answer this question, but nearly everyone provided feedback that having this information accessible would be useful. A few even theorized having this information could potentially save organizations billions of dollars,” he said.
The need here was to analyze application usage using user authentication logs from Duo Security, Okta, Microsoft Azure and Google Workspace. After completing a rudimentary flow chart, he reached out to a few of his developer friends, but most were busy. As a last resort, he turned to ChatGPT.
Get, set, go, get back again!
After reviewing the authentications logs from Duo Security to better understand what information he could use to generate the desired scripts, he made a digital concept of the project: a GoogleSheet!

Curiously, he turned to ChatGPT itself for troubleshooting. ChatGPT was able to point him in the right direction where he learned how to troubleshoot the script, leading him to the conclusion that the script was correct but the variables in the script were not.
A set of trials and changes followed, till it worked.
“The full process from start to finish took my somewhere between 4-8 hours from idea to having a working python script which might seem like a lot for a developer but the reality is I’m not a developer and wouldn’t know where to start,” he conceded.
“Most the time spent working on this was actually spent configuring, learning how to run the python client on my mac and setting up test environments so I could validate the scripts work.”
TCE took a look at the impressive end results:
Hoodwink Duo uses Duo Security authentication logs to identify how many unique active users accessed an application in the past 180-days.
Hoodwink Duo Bypass uses Duo Security authentication logs to identify users that successfully authenticated using a bypass authentication method.
Hoodwink Duo SMS Users uses Duo Security authentication logs to identify users that successfully authenticated using the SMS authentication method.
Hoodwink Okta uses Okta authentication logs to identify how many unique active users accessed an application in the past 180-days.
Hoodwink Okta Country uses Okta authentication logs to identify how many successful authentication attempts have been successful per country.
Barebones and prospects
When asked about to list the basic steps of the entire process, Garrity gave us this:
- I wrote down my idea
- I mocked up an example of what I wanted to create in a note pad
- I researched duo logs to determine if the data I needed was available
- I asked ChatGPT to create a script
- I tested the script, and it didn’t work
- I went back to ChatGPT and communicated the error, and it suggested a modified script
- The script worked but had a different result than expected
- I communicated this back to ChatGPT and it generated a modified script
- I retested the script, and it generated the expected outcome
“The additional scripts took significantly less time to create because I knew what questions to ask and how to reiterate fast,” he told TCE.
While the results are impressive, it entirely depends on the intention of the user. ChatGPT has been red-listed for the possibility of writing anything, from impeccable phishing email to malware and ransomware news
Explicitly mal intentional commands are blocked, but they can be easily circumvented with a host of tasks produces results that eventually add up to the desired malware, warned Picus Security co-founder Suleyman Ozarslan.
Daniel Von Fange, a distributed systems engineer who is an active contributor to many cryptocurrency code repositories, recently outed a bogus security researcher who wanted to file “cryptocurrency vulnerability” with the help of ChatGPT.
This is expected, said Garrity.
“There is an unlimited amount of possibilities which include both good and bad. Much like code can be used for good or bad, so can ChatGPT. Just because a tool is capable of being used for bad doesn’t mean it’s bad itself. It’s the people responsible for using the tool who need to be held accountable to their actions. We should expect ChatGPT to be used for good and bad,” he added.
And the best feature of ChatGPT? “The ability to reiterate with it to troubleshoot and modify scripts to get to the desired outcome,” said Garrity.






















































