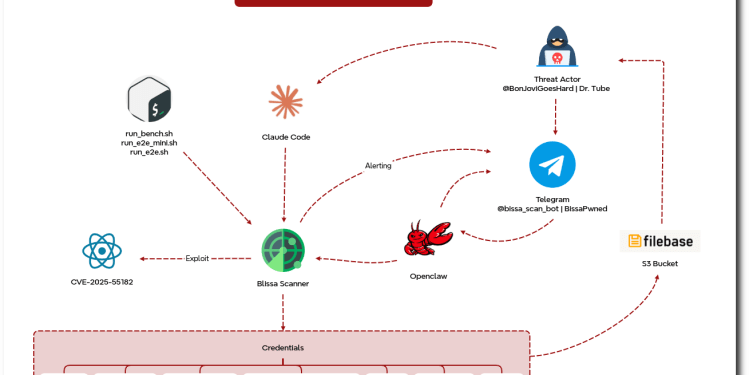
An exposed server sitting open on the internet handed forensic investigators something rarely available; an unobstructed view inside a running criminal operation, complete with code, logs, victim data, Telegram alert streams, and transcripts showing an operator using Claude Code and OpenClaw as day-to-day workflow assistants to build, debug, and refine an automated credential harvesting machine.
The DFIR Report published its findings, after discovering the exposed host and documenting its contents in full. The platform — identified across multiple operator-controlled tools and bot handles as “Bissa scanner” — combined React2Shell exploitation at internet scale with an AI-assisted operational pipeline that automated target scanning, compromise scoring, credential extraction, victim triage, and Telegram-based alerting into a single cohesive workflow.
The Vulnerability at the Center – React2Shell
CVE-2025-55182, widely tracked as React2Shell, is a CVSS 10.0 unauthenticated remote code execution vulnerability in React Server Components affecting React versions 19.0 through 19.2.0 and the Next.js framework that implements them. First publicly disclosed on December 3, 2025, the flaw allows an attacker to execute arbitrary code on the server with a single crafted HTTP POST request, exploiting insecure deserialization in the RSC Flight protocol with no authentication required.
Also read: ‘React2Shell’ Flaw Exploited by China-Nexus Groups Within Hours of Disclosure, AWS Warns
CISA added it to the Known Exploited Vulnerabilities catalog shortly after disclosure. Security vendors including Google GTIG, Microsoft, Wiz, and Cisco Talos all documented widespread exploitation activity across state-sponsored and financially motivated threat actors within days of the vulnerability going public.
The Bissa scanner operation represents a distinct, independently tracked campaign running on top of that vulnerability — one distinguished not by the exploit it used, but by the operational sophistication of what it built around it.
13,000 Files and a Running Operation
The exposed server contained more than 13,000 files across 150-plus directories covering exploitation, victim-data staging, credential harvesting, access validation, and operator workflow management. The DFIR Report characterized this infrastructure not as a passive data store but as active operational infrastructure — built to acquire access at scale and operationalize the highest-value results from that access.
Artifacts on the host showed that React2Shell was central to a workflow capable of scanning millions of internet-facing targets. Logs on the server indicated more than 900 confirmed successful compromises — a hit rate that reflects both the severity of the underlying vulnerability and the sophistication of the scanning pipeline built to exploit it at volume.
AI Tools as Criminal Workflow Assistants
The most operationally novel element documented in the DFIR Report is the direct integration of AI coding assistants into the attack workflow. Transcripts recovered from the server showed the operator using Claude Code — Anthropic’s command-line AI coding tool — and OpenClaw to read the scanner codebase, troubleshoot pipeline failures, orchestrate workflows, and refine the collection pipeline over time.
Claude Code and OpenClaw were used as an operator-side harness supporting exploitation activity and workflow orchestration, the report states. This AI-assisted workflow is what enabled the Bissa scanner to function as a modular platform supporting a broader, structured process: exploiting targets, reviewing results, validating access, and prioritizing the most valuable victim environments.
Every Tier of Modern SaaS Acted as Credential Harvesting Opportunity
Secret harvesting was the operation’s primary revenue mechanism. The tens of thousands of .env files — environment configuration files that web applications use to store API keys, database credentials, and service tokens — yielded credentials spanning every tier of modern cloud infrastructure.
AI providers constituted the single largest credential category, with keys recovered for Anthropic, Google, OpenAI, Mistral, OpenRouter, Groq, Replicate, DeepSeek, and HuggingFace. Cloud provider credentials covered AWS, Azure, Google Cloud, Cloudflare, and DigitalOcean.
Payment platform keys included Stripe, PayPal, Shopify, and Square. Database credentials spanned Supabase and MongoDB. Identity and authentication secrets from Auth0, Okta, and Clerk were also present, alongside GitHub tokens, Slack integration keys, Twilio and SendGrid messaging credentials, Fireblocks crypto custody API keys, and Plaid banking integration tokens.
The scope of this credential inventory reflects a critical structural weakness in modern cloud-native applications. Developers routinely store production secrets in .env files that ship with deployed code, creating a single-file jackpot for any attacker who achieves code execution on a web server.
The Operator Triaged What It Found
The DFIR Report’s most significant finding beyond the raw credential volume is that the Bissa scanner operation was not indiscriminate at the post-compromise layer. Artifacts show the operator triaged victim access, validated stolen data, and concentrated deeper collection and follow-on activity on organizations that met a clear value threshold — particularly those in the financial, cryptocurrency, and retail sectors.
Three victim clusters on the server illustrate this selectivity. One victim was a mid-sized tax resolution and financial advisory firm whose staged dataset included Plaid tokens, linked bank-account data, IRS transcript material, ACH-related records, Twilio call data, Salesforce contacts, and case files containing Social Security numbers and dates of birth.
A second victim was a large digital-asset, payments, and enterprise finance company whose compromised data reflected authenticated Oracle Fusion REST export activity tied to supplier, invoice, purchase-order, and bank-account records.
A third victim, a mid-sized payroll, HR, and stablecoin payments platform, had payroll, settlement, Fireblocks integration, and HR information system material staged on the same server. In the second and third cases, the initial access path could not be confirmed as originating from the React2Shell scanner.
One Person, Two Bots, a Telegram Channel
Runner scripts across the Bissa scanner harness hardcoded a Telegram bot token tied to @bissapwned_bot, with all exploit confirmation alerts routed to a private chat channel whose sole human participant carries the public Telegram identity @BonJoviGoesHard with display name “Dr. Tube.”
Each bot message delivered a one-line structured alert per confirmed CVE-2025-55182 hit, distilling the victim’s identity, runtime context, privilege level, cloud posture, and recoverable secret surface into a single at-a-glance triage record — enabling the operator to process hundreds of exploitation events directly from a mobile phone.
The operator appears to run at least two dedicated bots: @bissapwned_bot for scanner alerting and @bissa_scan_bot within the AI-control subsystem — consistent branding across a portfolio that also includes tools labeled bissascanner, bissa_bench, and bissapromax.
The DFIR Report and parallel research from Cisco Talos, Microsoft, and Google all converge on the same immediate priorities: patch CVE-2025-55182 across all Next.js and React Server Components deployments immediately; rotate all API keys, database credentials, and .env secrets as a precautionary measure regardless of confirmed exploitation; audit application logs for POST requests containing $@ patterns or #constructor strings; restrict access to cloud metadata service endpoints; and implement secrets scanning across CI/CD pipelines to eliminate .env files as a persistent attack surface.