Researchers found a new malicious software, named WikiLoader malware. It was named so because it made a request to Wikipedia for a response with the string “The Free” in the contents.
The WikiLoader malware has been found to target Italian organizations.
WikiLoader is an advanced download manager that aims to deploy an additional malicious payload. This malware incorporates clever evasion methods and unique code implementation, making it difficult to detect and analyze.
It appears that WikiLoader was probably created with the intention of being leased to specific cybercriminal threat actors.
“Based on the observed use by multiple threat actors, Proofpoint anticipates this malware will likely be used by other threat actors, especially those operating as initial access brokers (IABs),” said the Proofpoint report on WikiLoader.
Campaign distributing WikiLoader malware
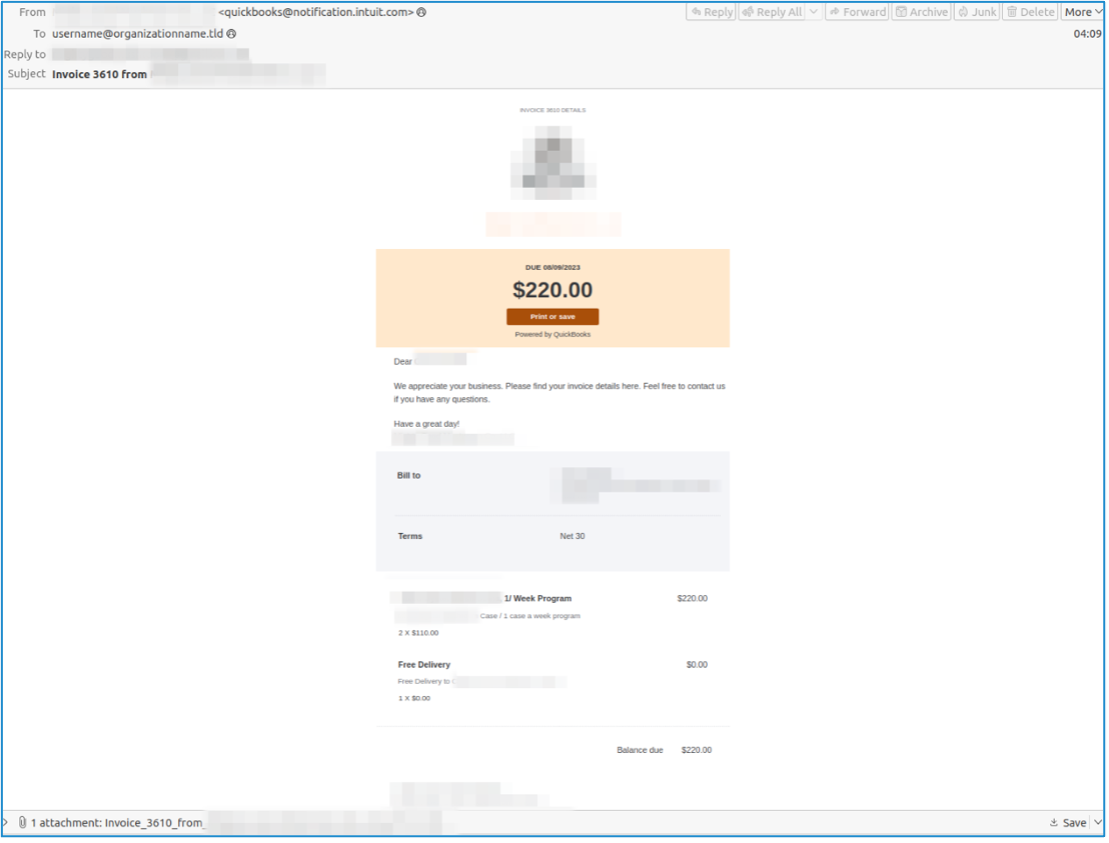
The WikiLoader malware gets sent to the user via emails with attachments of either Microsoft OneNote, a PDF document, or an Excel sheet as shown in the following screenshot –

The Excel attachment was created to look like the Italian Revenue Agency, however, it wasn’t.
In its blog post, Proofpoint, the cybersecurity company detailed the WikiLoader as a downloader that installs a second malware payload and can evade detection.
The actively developed malware can access web hosts, and exfiltrate host data via HTTP cookies. Cybercriminals were found using Discord’s CDN as a host for files. However, it was not confirmed if Discord was compromised.
Cybercriminals using the WikiLoader uploaded samples in any Discord chat and copied the Discord link to the attachment.
Cybercriminals employing the WikiLoader malware
WikiLoader was first found to be used by a cybercriminal group known as TA544. This group has been known to use the Ursnif malware to target Italian organizations. Researchers argue that the malware will mostly be used by cybercriminals operating as Initial Access Brokers (IABs).
Proofpoint researchers found nearly eight campaigns starting on December 2022 that distributed the WikiLoader malware. Another group known as TA551 used WikiLoader to attack Italian organizations.
In February this year, another updated version of WikiLoader was found being used against Italian organizations by TA544.
Again in March, TA551 with executables attached in OneNote documents sent emails in the Italian language.
The latest version of the WikiLoader malware was found employed on July 11 this year by TA544. This campaign sent over 150,000 messages, however, included targets outside of Italy.
Other details of the WikiLoader malware

The first version of WIkiLoader malware had shellcode without much obfuscation however the second version found on February 8, 2023, had added complexity and used encoded strings.
The third version of the WikiLoader malware had the following upgrades –
- Could make indirect syscalls
- Exfiltration of cookies from the loader that contained host data
- Execution of the loader in an hour
- Shellcode stages were written byte by byte using NtWriteVirtualMemory
The campaign in February saw the threat actors sending emails imitating an Italian courier service. The email contained VBA macro-enabled Excel documents that installed the WikiLoader malware.
“This version of WikiLoader contained more complex structures, additional stalling mechanisms used in an attempt to evade automated analysis, and the use of encoded strings,” read the Proofpoint blog.
The packed downloader used with the malware is to evade detection and analysis. The WikiLoader malware executable is smaller and worked to download the actual payload. This mechanism also allowed hackers to control the delivery of payloads.
They could control the timeframe for the downloads to be active and include features like IP filtering. Addressing how the malware is packed with features, the Proofpoint blog added, “This causes issues with common analysis tools such as IDA Pro and Ghidra.”




















































