Web applications, databases, sub-domains, DNS configuration, and public_html are some of the online places where you can never allow a hacker in. If they do, sometimes forcefully, a full account takeover is just a matter of time.
Since these are the most targeted assets of a website/company, attackers have a hawk eye on them. However, white hat hackers, the red teams, and security companies also hack into these online services to perform pen testing on mobile apps, servers, and workflows.
A successful pen tester is not someone who can get inside into every system, but the one who can find multiple bugs within the same system. In 2026, organizations heavily rely on pen testers to hack into their system, report vulnerabilities to them, and support their data protection endeavors.
If you are a beginner in your pen testing journey, The Cyber Express has the perfect starter guide for you. In this article, we will discuss the basics of pen testing, why it is important, and what tools and methodologies are used to accomplish a successful and effective penetration test.
What Is Penetration Testing?
Penetration testing, often referred to as pen testing, is a structured security assessment technique that simulates real-world cyberattacks to identify and exploit vulnerabilities in systems, networks, or web applications. Unlike basic vulnerability scans, penetration testing actively tests weaknesses to determine the potential impact of an attack.
The penetration testing meaning extends beyond simply finding vulnerabilities; it evaluates how these weaknesses can be exploited, the severity of the risks, and the potential consequences for the organization. Penetration testers, commonly known as ethical hackers, employ the same tactics as cybercriminals but do so in a controlled and authorized manner, ensuring that testing is both effective and safe.
Essentially, what is a penetration test? It is a proactive security assessment that combines automated tools and manual techniques to uncover flaws before attackers can exploit them. Organizations use this process to strengthen their security posture, reduce risk, and improve incident response capabilities.
Why Penetration Testing Is Important
Cyber threats are updating in both size and complexity every second, making penetration testing in cybersecurity an essential practice. Common vulnerabilities such as SQL injection, cross-site scripting (XSS), broken authentication, and insecure file handling can lead to lethal consequences, including data breaches, financial loss, regulatory penalties, and reputational damage.
By performing penetration testing, organizations can:
- Identify and address vulnerabilities proactively
- Understand the real-world impact of potential attacks
- Strengthen compliance with standards like PCI DSS, HIPAA, and ISO 27001
- Improve incident response and security awareness
- Prioritize remediation based on risk rather than theoretical severity
Penetration testing is not just a technical exercise; it is a strategic component of a comprehensive cybersecurity program.
Types of Penetration Testing
There are several approaches to penetration testing, each targeting specific aspects of an organization’s environment:
- Network Penetration Testing: Focuses on internal and external networks, identifying vulnerabilities in routers, firewalls, and connected systems.
- Web Application Penetration Testing: Evaluates websites and applications for common flaws like SQL injection, XSS, CSRF, and broken authentication.
- Mobile Application Penetration Testing: Targets vulnerabilities in mobile apps across iOS and Android platforms.
- Cloud Penetration Testing: Assesses misconfigurations and weaknesses in cloud environments, including SaaS, PaaS, and IaaS platforms.
- Social Engineering Tests: Simulate phishing, pretexting, or baiting attacks to evaluate human vulnerabilities.
Understanding the types of penetration testing helps organizations select the right approach based on their systems, business logic, and threat exposure.
How Does Penetration Testing Work?
Penetration testing follows a structured methodology that ensures that all aspects of the system are evaluated thoroughly. The process typically includes the following stages:
Information Gathering
Testers begin by collecting as much information as possible about the target system. This includes domain names, IP addresses, subdomains, hosting environments, and technologies like web servers, frameworks, and databases. Passive techniques, such as analyzing public data, and active techniques, like DNS enumeration, help testers map the attack surface.
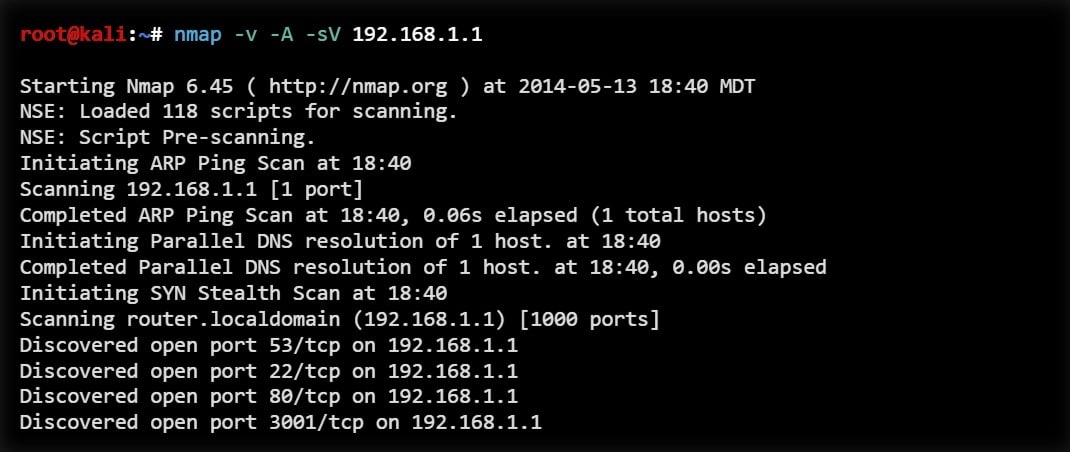
Reconnaissance and Scanning
Next, testers perform reconnaissance to identify open ports, running services, and exposed endpoints. Tools such as Nmap are used for network mapping, while Nessus and OpenVAS scan for known vulnerabilities. Both automated and manual validation are critical to eliminate false positives.
Vulnerability Identification
Once reconnaissance is complete, vulnerabilities are identified. This phase targets issues such as:
- SQL injection
- Cross-site scripting (XSS)
- Cross-site request forgery (CSRF)
- File inclusion vulnerabilities
- Broken authentication and session management
- Insecure access controls
Testers combine automated tools like Burp Suite, Nessus, and Qualys with manual testing to uncover complex logic flaws often missed by scanners.
Exploitation
The exploitation phase assesses the real-world impact of vulnerabilities. Testers attempt to leverage weaknesses to gain unauthorized access or escalate privileges. Common tools include Metasploit, sqlmap, and Burp Suite. Successful exploitation demonstrates how attackers could compromise systems and help organizations prioritize remediation.
Post-Exploitation
After initial access, testers evaluate the potential damage by accessing sensitive data, moving laterally, or maintaining persistence. This step reveals the broader consequences of a breach without causing actual harm.
Reporting and Remediation Guidance
Finally, testers prepare a detailed report documenting vulnerabilities, exploitation methods, impact, and recommended mitigation steps. A high-quality penetration testing report provides actionable guidance for technical teams and management, prioritizing risks based on real-world severity.
Penetration Testing Tools and Their Uses
Penetration testing tools are specialized software used to identify, exploit, and assess vulnerabilities in systems, networks, and applications.
They support different phases of a penetration test, including reconnaissance, scanning, exploitation, post-exploitation, and reporting.
Network Discovery and Reconnaissance
- Nmap: Scans networks to identify live hosts, open ports, and services. Supports OS detection and custom scripts.
- Masscan: High-speed port scanner for large networks; often used before deeper scans with Nmap.
Vulnerability Scanners
- Nessus: Commercial scanner that detects outdated software, misconfigurations, and known vulnerabilities.
- OpenVAS: Open-source alternative to Nessus for identifying system weaknesses.
- Qualys: Cloud-based scanner for vulnerability management and compliance monitoring.
Web Application Testing
- Burp Suite: Intercepts and manipulates web traffic; finds SQL injection, XSS, CSRF, and logic flaws.
- OWASP ZAP: Open-source web proxy with automated scanning and fuzzing.
- Nikto: Web server scanner for outdated software and insecure files.
Exploitation Tools
- Metasploit: Framework for exploiting vulnerabilities, gaining access, and performing post-exploitation.
- Core Impact: Commercial exploitation platform with automated attack paths and reporting.
Database and Injection Tools
- sqlmap: Automates detection and exploitation of SQL injection vulnerabilities across multiple database platforms.
Password and Credential Tools
- Hydra: Performs network login brute-force attacks on multiple protocols.
- John the Ripper: Cracks password hashes using brute-force or dictionary attacks.
- Hashcat: GPU-accelerated password recovery tool for large-scale hash cracking.
Wireless and Network Attack Tools
- Aircrack-ng: Captures and analyzes Wi-Fi traffic, tests WPA/WPA2 encryption, and performs deauthentication attacks.
Post-Exploitation Tools
- Mimikatz: Extracts passwords, hashes, and tokens from Windows memory.
- BloodHound: Maps Active Directory environments to identify privilege escalation paths.
Reporting Tools
- Dradis, Faraday, Serpico: Help organize findings, assign severity, and produce professional penetration testing reports.
Penetration Testing vs Vulnerability Assessment
It is important to differentiate penetration testing vs vulnerability assessment. A vulnerability assessment identifies potential weaknesses but does not attempt to exploit them, providing a theoretical overview of risk. Penetration testing goes a step further by actively exploiting vulnerabilities to measure real-world impact, offering actionable insights that can directly guide remediation and risk prioritization.
Real-World Examples
The necessity of penetration testing is evident in high-profile vulnerabilities. For example, recently, the open-source workflow automation platform n8n was affected by CVE-2025-68668, a critical flaw rated 9.9 on the CVSS scale. The vulnerability allowed authenticated users to execute arbitrary system commands due to a sandbox bypass in the Python Code Node.
The flaw was mitigated in n8n version 2.0.0 through architectural changes, highlighting that effective security solutions often require more than patches; they may necessitate structural improvements. Penetration testing identifies such systemic risks before they can be exploited in production.
The Future of Penetration Testing
As technologies like AI, machine learning, IoT, and cloud computing expand the digital landscape, penetration testing must evolve. Modern attackers employ automation and highly advanced techniques, requiring testers to continually update their skills, tools, and methodologies.
Continuous penetration testing is replacing periodic assessments, integrating security into DevSecOps pipelines to identify vulnerabilities early. This proactive approach reduces the window of opportunity for attackers and ensures security remains a core component of system design.
Penetration testing is no longer a one-off exercise; it is a critical, ongoing strategy that strengthens an organization’s overall cybersecurity posture, informs risk management, and enhances incident response.
Penetration testing explained shows it is far more than a technical procedure; it is a strategic necessity in today’s cybersecurity environment. From network and web application assessments to social engineering and cloud testing, penetration testing provides a comprehensive view of real-world risk. By combining skilled testers with tools and ethical practices, organizations can defend their systems, protect critical data, and strengthen trust in their digital operations.
To sum up, understanding the penetration testing definition, how penetration testing works, and applying it effectively is indispensable for any organization serious about cybersecurity.
Caution: The Cyber Express does not endorse or approve any tools, methods, or activities described here. This content is for informational purposes only and should only be used in authorized, legal environments.