An added benefit of “Operation Magnus” that took down one of the biggest infostealer operations around the globe was the ability to track down the alleged handler of the RedLine infostealer operation, which infected hundreds of systems used by the United States Department of Defense members.
While the Dutch police took down three servers and its Belgian counterparts seized several communication channels linked to the Redline and Meta infostealers, the U.S. Department of Justice on Monday unsealed charges against perhaps one of the main handlers of the operations.
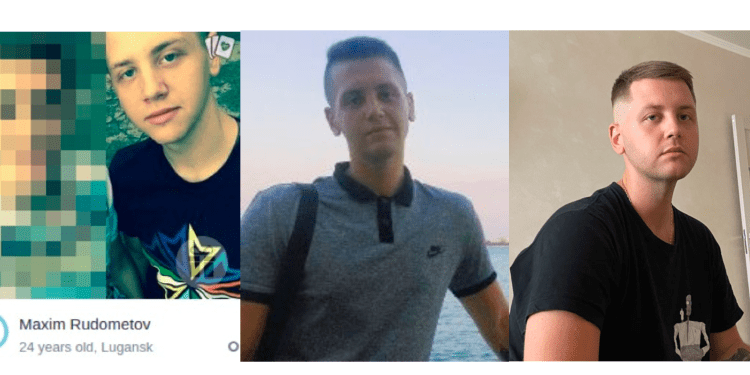
According to the Justice Department charges, Maxim Rudometov, a man in his mid-20s is one of the developers and administrators of RedLine Infostealer. The complaint said that Rudometov regularly accessed and managed the infrastructure of RedLine Infostealer since 2020.
Rudometov has several cryptocurrency accounts linked to him under multiple fake identities and used them to receive and launder payments received from customers of the RedLine infostealer. The stealer malware was sold to customers for a mere $100-$150 rental model popularly known as Malware-as-a-Service.
Rudometov has been charged on multiple counts including access device fraud, conspiracy to commit computer intrusion, and money laundering. If convicted on all counts, Rudometov faces a maximum penalty of 35 years in prison.
Linking Rudometov to RedLine
Rudometov’s alleged activities were uncovered after extensive tracking of online monikers – “Dendimirror” and “Alinchok” – and email addresses linked to the malware’s deployment. Investigators also tracked cryptocurrency payments associated with RedLine, uncovering transaction histories and specific account patterns.
Through cross-referencing IP addresses, investigators linked Rudometov’s known online accounts to RedLine’s operational servers. His accounts reportedly interacted with RedLine’s licensing server and his Apple iCloud, tying him to the malware configuration utility used to deploy RedLine.
Adding to the evidence, law enforcement identified accounts registered to Rudometov on GitHub that hosted encryption keys required by RedLine. This development provided critical clues, as these encryption keys are essential for malware deployment, allowing RedLine affiliates to build customized payloads targeting victims. These findings, combined with Rudometov’s other online activities and cryptocurrency transfers, cemented his alleged role in the RedLine operation.
Victim Impact Includes Active U.S. Military Personnel
According to federal authorities, RedLine has compromised millions of computers worldwide. In the U.S. alone, thousands of victims experienced data theft ranging from personal financial data to confidential business accounts. In several cases, RedLine even breached the digital defenses of U.S. military personnel, granting criminals access to sensitive government systems.
“On or about April 29, 2022, [a private cybersecurity] firm provided investigators with the logs of stolen information, which included over 2,000 individual records containing at least one credential for an account, service, or website, owned, or administered by the Department of Defense,” the court filing said.
The stolen credentials include those for websites like MyPay, the Department of Defense paycheck portal, the U.S. Army’s Office 365 email environment, and a website owned by the Defense Manpower Data Center, which serves as a repository for personal information including sensitive information about a service members’ dependents. Law enforcement confirmed that email addresses owned by the Department of Defense were legitimate and assigned to individuals actively serving in the U.S. Military.
For individuals, RedLine’s impact included losses in both privacy and finances. One victim, identified as “Victim A” in the court filing, lost approximately $370,000 in cryptocurrency after RedLine accessed their online wallet.
For organizations, the malware breached internal networks, exposing key resources and critical employee data. Affected organizations reportedly include U.S. defense contractors and tech giants, where stolen credentials and cookies were used to gain unauthorized access to internal systems.
In one instance an unnamed Redmond headquartered tech giant – likely Microsoft – had the “Lapsus$” threat group use the RedLine Infostealer to obtain passwords and cookies of an employee account. According to information published in public domain, the employee’s access was used to obtain, and subsequently leak, limited source code owned by the tech company.
About Operation Magnus
The DOJ, in collaboration with the FBI, the Netherlands, Belgium, and Europol, led the effort through the Joint Cybercrime Action Taskforce (JCAT), targeting RedLine and META’s command-and-control networks.
Operation Magnus, as it’s called, resulted in the seizure of crucial assets, including servers, domains, and Telegram accounts used by the infostealers’ operators. By disrupting this network, officials believe they’ve delivered a significant blow to a top malware-as-a-service (MaaS) operation that has preyed on organizations and individuals across the globe.
Also Read: Operation Magnus Takes Down RedLine and Meta Infostealers
Why RedLine and META Stand Out
RedLine and Meta operate through a MaaS model, allowing cybercriminals to license the malware and independently run campaigns to infect victims. Unlike traditional malware, this decentralized approach has made RedLine and Meta highly adaptable and widely distributed.
RedLine and Meta infiltrate systems stealthily, using malware loaders that first install and then deploy the infostealer or additional malicious software. These loaders commonly spread through cracked software, illegal downloads, and fake updates. Phishing emails, malvertising, and unpatched software vulnerabilities also play a role.
Once active, these infostealers check if they’ve recently been on the system by placing unique markers. RedLine, for instance, creates a folder in “%LOCALAPPDATA%\Microsoft\Windows” using a Cyrillic “o” in “Windows.” Meta marks its presence with a folder in “%LOCALAPPDATA%\SystemCache.” By verifying these markers and their timestamps, the malware determines if re-infection is needed.
Once downloaded, these infostealers hunt for valuable information on the infected system. The goal? Extracting sensitive data such as usernames, passwords, banking details, cryptocurrency accounts, and session cookies that bypass multi-factor authentication (MFA) security protocols.
These “logs” of stolen data are sold on cybercrime forums, giving hackers a lucrative trove to exploit further. Security experts note RedLine’s notoriety due to its ability to infiltrate even the most secure corporate networks, raising alarms across industries.
Tactical Wins and Ongoing Investigation
Law enforcement’s tactics involved targeted seizures of domains and servers, halting RedLine and META’s access to infected devices. By seizing Telegram channels used for customer support and updates, officials disrupted the malware’s operational lifeline and hindered its spread. This seizure marks a high-impact move against threat actors relying on popular platforms to communicate and coordinate.
But despite these successes, investigators acknowledge that this operation only scratches the surface. Officials estimate millions of credentials, credit card numbers, and other sensitive records remain in circulation. “The U.S. does not have all stolen data in its possession, and the investigation continues,” a DOJ representative commented.
While the U.S. seized two domains and the Netherlands along with the same number of domains additionally took down three servers used in the operations, Eurojust, the European crime coordination agency said the authorities had detected almost 1200 servers linked to these stealers’ operations.
For victims or those concerned about potential exposure, authorities have launched an information portal, www.operation-magnus.com, offering details and resources to assist in remediation. Concurrently, security firm ESET, who initially flagged the infostealer operations to the Dutch police, have released a one-time online scanner for potential victims to check for infections.
RedLine and Meta Remain a Persistent Threat
While RedLine and META stand among the most dangerous infostealers, they’re part of a broader trend toward accessible, powerful malware that even novice hackers can deploy. MaaS-based models, where malware licenses are sold as easily as software subscriptions, have created a burgeoning market on dark web forums. Cybersecurity analysts warn this trend democratizes malware distribution, making sophisticated attacks feasible for a much larger pool of cybercriminals.
According to security research, RedLine has rapidly risen to one of the most prevalent malware types worldwide, often taking advantage of themes like COVID-19 alerts or critical system updates to bait victims into downloading the malware. These socially engineered ploys add a layer of believability that catches even seasoned users off guard, underscoring the need for ongoing user awareness and strong corporate defenses.
*UPDATED (Oct 29, 11:15 AM ET): The article was updated to include details from the unsealed complaint that was shared by the U.S. Justice Department with The Cyber Express.