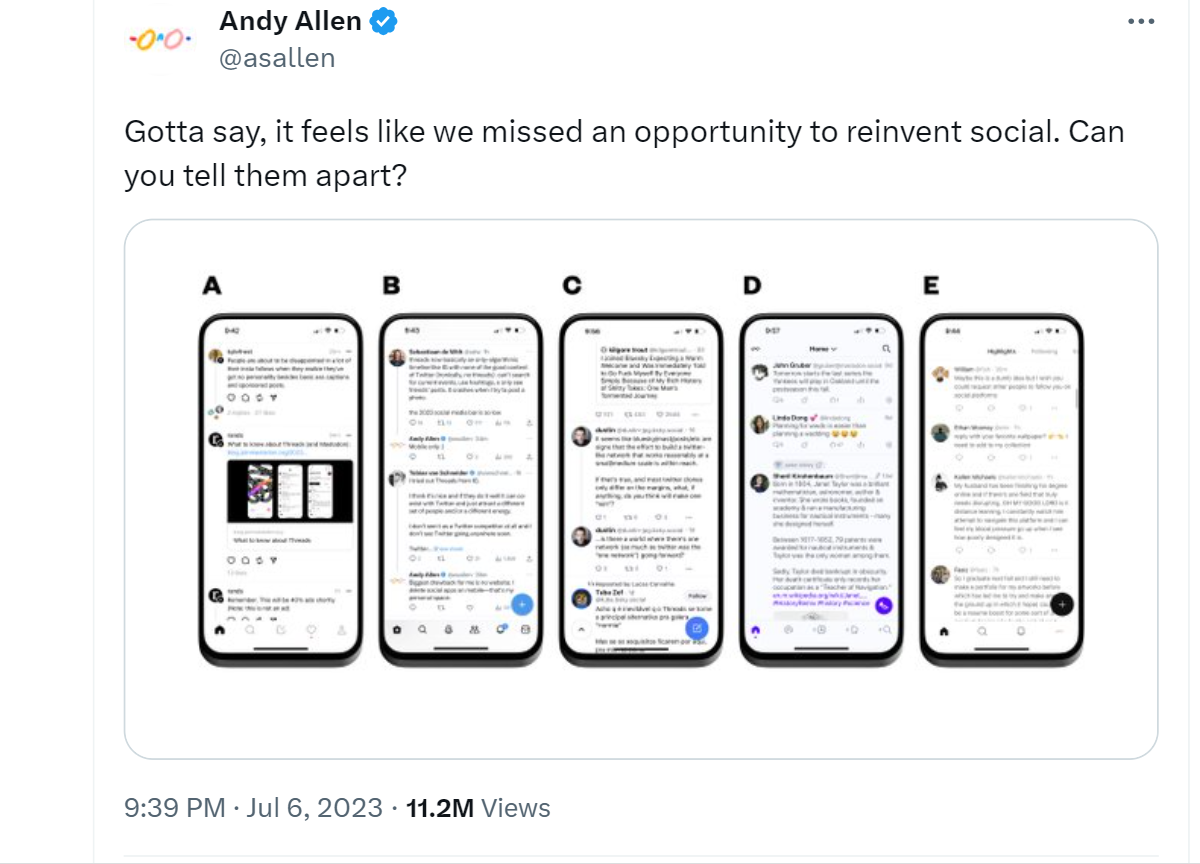
When Victoria Effer, Dublin Co-Lead of Women@LinkedIn, posted on LinkedIn about her new account in “Threads, an Instagram app”, the new social media platform launched by Meta, most of her contacts wanted to know how.
How did she manage to get an account despite being in the EU territory, where Instagram Threads is currently unavailable?
She was just the latest among several EU residents who managed to find workarounds to obtain a Threads account.
Instagram Threads has not yet been launched in the European Union, and there is uncertainty whether it will ever be available in the region.
This is primarily due to the EU’s stringent privacy regulations, which are more stringent compared to many other countries.
Meta, the company behind Threads, has faced challenges in complying with these regulations in recent years.
It is worth noting that the European Union did not directly block the app’s launch; rather, Meta is taking precautionary measures and being careful before introducing Threads in the EU.
Twitter vs. Threads vs. data privacy: Why this hue and cry?
It’s been hardly a day since Threads was launched by Facebook’s parent company, Meta, but it already has more than 30 million accounts. And many have started to pitch Twitter vs. Threads to understand where the two social media apps lie in terms of privacy.
It has also managed to raise significant privacy concerns, particularly in the European Union (EU).
The Cyber Express did a reconnaissance of the situation. Here are the red flags that we managed to spot.
Collection of sensitive personal information:
Threads collects highly sensitive personal information, including sexual orientation, race, ethnicity, biometric data, trade union membership, pregnancy status, politics, and religious beliefs.
This data may potentially be shared with “service providers” and “analytics partners,” which often refers to third-party advertising and marketing firms.
The sharing of such sensitive data raises concerns about user privacy and the potential for unauthorized use or exploitation.
Collection of employment-related data:
Threads collects information about users’ employment, such as their company, role on the team, job history, and performance evaluations.
This data may be shared with third parties, raising concerns about the confidentiality of employment-related information and potential misuse of such data.
Collection of body-related data:
Threads collects data about users’ health, fitness, and exercise habits, which may be shared with third parties.
The collection of such data raises concerns about privacy, as health-related information is highly sensitive and requires special protection.
Collection of web activity data:
Threads may collect users’ browsing history, web page interactions (including with ads), and the referring web page or source through which they accessed Threads links.
This information may be shared with third parties, potentially compromising user privacy and allowing for targeted advertising based on browsing behavior.
Collection of location data:
Threads may collect users’ location data, including photos, videos, or other recordings of their environment and IP-address-based location information.
This data may be shared with third parties, raising concerns about tracking and surveillance, as well as potential misuse or unauthorized access to location information.
The killer, of all, is this:
Inability to delete Threads without deleting Instagram:
The platform is named “Threads, an Instagram app” for a reason. Instagram is literally the entry point to the app. Once a user commits to Threads, they cannot delete it without also deleting their Instagram account.
This lack of independent control over Threads raises concerns about user autonomy and the difficulty of disengaging from the platform while maintaining access to other services.
Why would EU take stock of the Instagram Threads data privacy situation?
Threads’ data collection practices, particularly regarding sensitive information, may violate the General Data Protection Regulation (GDPR) and other data protection regulations in the EU.
Meta’s reliance on behavioral advertising and profiling users without explicit consent is not in line with current EU regulations and may face penalties under the DMA (Digital Markets Act) and DSA (Digital Services Act).
The absence of a general up-front choice to deny tracking and profiling, as well as the lack of specific permission for processing sensitive data, raises concerns about privacy compliance.
The European Court of Justice ruled against Facebook’s targeted ad model, questioning its justification of using “legitimate interest” to process user data for advertising purposes.
EU watchdogs can consider data privacy violations by tech giants in antitrust investigations, which adds further scrutiny to Meta’s practices.
Meta has been fined €1.2 billion and barred from transferring user data from the EU to the US, posing significant obstacles to Threads’ launch in the EU and raising doubts about its future in the region.
Meta itself faces legal uncertainty due to the incoming DMA regulations, which may restrict the sharing of user data across different platforms.
The central enforcement of penalties under the DMA, with fines up to 10% of global annual turnover, poses significant financial risks for Meta’s data-driven business model.
Meta may be more comfortable with legal risks in the UK – its largest market in Europe in terms of accounts open – due to the ICO’s historically inactive approach to systemic breaches.
The regulatory landscape in the UK differs from that of the EU, thanks to Brexit.
However, the UK’s plan to weaken domestic data protection standards and erode the independence of the ICO may have implications for privacy protections in the future.
Twitter vs. Threads: Is Twitter Under Threat?
Most of the sore points listed for Instagram Threads, incidentally, is applicable to literally all popular social media platforms.
The collection of sensitive personal information, employment-related data, body-related data, web activity data, and location data happens across all, and its potential unauthorized use is a universal threat.
Then why this special attention on Threads? Was Twitter – the obvious competition – any better? Is the
Twitter, across is 15 years of existence, raised these issues across the world.
Data collection and usage:
Similar to Threads, and almost all other social media platforms, Twitter collects a significant amount of user data, including personal information, posts, interactions, and browsing behavior.
Twitter analyzes user data to personalize the content of users’ timelines, suggest accounts to follow, and serve targeted ads based on users’ interests and behavior.
Concerns arise regarding how Twitter uses this data for targeted advertising, data mining, and profiling users.
Public nature of tweets:
Users often forget that tweets are public by default, leading to concerns about the potential for misuse or exploitation of shared information.
Users may inadvertently share sensitive personal details, opinions, or location information that can be accessed by anyone.
Imagine a user tweeting about their vacation plans, including the dates and the location they will be visiting. This information can potentially be used by malicious individuals for stalking or targeting purposes.
To be fair, it is a user issue than a platform issue. Twitter has the provision of keeping the tweets private. However, we still be sharing some information with our network, and all information with Meta and its affiliates.
Data sharing with third parties:
Users are concerned about Twitter’s data-sharing practices with third-party companies, advertisers, and analytics firms.
Sharing user data with these entities raises questions about user consent, control over personal information, and the potential for data misuse.
Twitter provides APIs (Application Programming Interfaces) that allow developers and third-party apps to access user data. Users worry that these third parties may have access to their personal information without their explicit knowledge or consent.
Retention and handling of deleted tweets:
Like Facebook, keeping a handle inactive or deleting it altogether does not remove your activity data.
Concerns about how Twitter retains and handles deleted tweets, including whether they are completely removed from Twitter’s servers, is rife.
Twitter itself is ambiguous about how it handles such data and how its associates will use it, considering that more than 10% of its 2022 revenue came through data licensing.
Users worry about the potential for deleted tweets to resurface or be used in ways they did not anticipate.
A user who deletes a tweet containing sensitive personal information assumes that it is permanently removed. However, there is uncertainty about how long the tweet remains in Twitter’s servers or if it may still be accessible through other means.
Lack of transparency:
Users raise concerns about the lack of transparency regarding Twitter’s data practices, algorithms, and how user information is used.
Users often feel uncertain about how their data is processed and whether they have control over their privacy settings.
In the post-Musk era, how Twitter’s algorithms that determine the content users see in their timelines or the ads they are served is expected to change drastically. The lack of clear explanations can lead to suspicions of data manipulation or biased content presentation.
Threads, Twitter and data privacy: Epilogue
It is safe to say that both Twitter and Threads face significant privacy issues. Twitter’s issues are about data collection, public nature of tweets, security risks, data sharing with third parties, retention of deleted tweets, and lack of transparency.
Threads, on the other hand, is in the red regarding the collection of sensitive personal information, employment-related data, body-related data, web activity data, location data, and the inability to delete Threads without deleting Instagram.
The issues are so similar that when we heard Elon Musk is going to sue Meta over Threads, we assume it’s a bid to retain the title of the largest data hoarder cum privacy violator!
In that case, we know who the winner is!