Cybersecurity Jobs are a thriving field, and recruiters across sectors are looking for professionals to fill several positions. With the growing demand for cybersecurity professionals in 2023, individuals can begin looking for the position and area of work that interests them the most.
Several positions require a set of skills, awareness about threat landscapes, trends, and risks, and the caliber to learn and grow to fill the nearly one million positions that will be opened in 2023.
The following are the top 10 cybersecurity jobs that are in-demand for 2023. These positions are crucial for safeguarding businesses and individuals from cyber threats and data breaches.
Find out more about the duties and necessary skills for each job, as well as salary information from PayScale, eligibility requirements, etc. Note that salary ranges may vary based on factors such as the company, the candidate’s education, cybersecurity certifications, previous experience, and skill set.
The top 10 cybersecurity jobs in-demand for 2023:
Among the most coveted positions, such as the chief information security officer (CISO), the aspirant may choose the one best suited for them based on their credentials.
-
Chief Information Security Officer (CISO)
Strategies pertaining to cybersecurity Jobs are looked after by the company’s chief information security officer (CISO). They come with a balanced blend of education and relevant experience and make around $170,000 annually.Experience in threat intelligence, incident response, and network security is expected from applicants.They lend their expertise in identity access management, risk management of data privacy management of data, and information security operations center (ISOC), among others.
Average Annual pay range for a CISO according to PayScale: $108,000 – $233,000
-
Information Security Manager
Information security programs are under the watch of the information security managers. Their annual salary can be around $120,000. They require a bachelor’s degree in the field of information technology or computer science.
Besides the basics, they also need to possess adequate cybersecurity Jobs certifications, such as the certified information security manager (CISM) or the certified information systems security professional (CISSP). Having work experience in information security to gain expertise in compliance, risk management, security solutions, etc. can add to their candidature. As an employee of a company, an information security manager is expected to upgrade their leadership skills constantly.
Average Annual pay range for an Information Security Manager according to PayScale: $82,000 – $156,000
-
Security Architect
A security architect of business designs, implements, and looks after its complete security infrastructure making sure a defensive mechanism is in place to defend against threats. They are aware of the requirements of the company and oversee its implementation. They have knowledge of network hardware configuration, and cryptography, among others.
Their annual salary can be around $120,000.A candidate may apply with a degree in computer science and certification in related fields such as the certified information systems security professional (CISSP). Relevant work experience in the field also adds to the applicant’s profile.
Average Annual pay range for Security Architect according to PayScale: $87,000 – $158,000
-
Network Security Engineer
Overseeing the designing, implanting, and maintaining of the company’s network security systems is one of the core areas of work a network security engineer must take care of. They earn nearly $93,000 annually.
A bachelor’s degree in computer science or information technology combined with the certified information systems security professional (CISSP) certification or the certified ethical hacker (CEH) certification paves the way into this position. Besides pentesting and finding vulnerabilities in computer systems and programs, a network security engineer must aim for upgraded skills in network design, and network and security protocols. Having experience in network security enhances their chances of being considered for this position in combination with leadership skills.
Average Annual pay range for a Network Security Engineer according to Payscale: $63,000 – $140,000
-
Security Engineer
A security engineer of a company will, much like most Cybersecurity Jobs officials be designing and implementing system security. They will make sure every required solution and tool is put in place to combat risk and deter cyberattacks.
Having a bachelor’s degree in computer science, or information systems is required to apply for the position of security engineer. They also need related cybersecurity Jobs certification such as the certified ethical hacker (CEH) to be eligible for this position along with experience in information security. Having skills in cryptography, various security protocols, and security engineering helps. They earn anywhere around $92,000.
Average Annual pay range for a Security Engineer according to PayScale: $67,000 – $144,000
-
Security Consultant
A security consultant has expertise in maintaining security in a company and assessing its security posture. They typically earn around $85,000 annually. They require a bachelor’s degree with a major in the relevant field of interest.
Having a certification in homeland security, certified security consultant (CSC), certified protection professional, and intelligence management may be considered a plus in considering their candidature for this position. Security consultants may provide training in cybersecurity Jobs to all the departments of a company and conduct various security evaluations to ensure the safety of the systems.
Average Annual pay range for a Security Consultant according to PayScale: $52,000 – $128,000 -
Ethical Hacker
An ethical hacker or a penetration tester is paid nearly $84,000, depending upon experience, education, certification, and knowledge. They are required to have training in identifying security vulnerabilities, assessing regulatory measures, and offering quality assurance.
Experience of one to four years in information security would help an applicant in bagging this job. Hands-on knowledge of Windows, Linux, UNIX, Python, and C++ helps in demonstrating more skills to prove their acumen. Certified ethical hacker (CEH), certified expert penetration tester (CEPT), offensive certified professional (OSCP), or others in the relevant area add to the credentials.
Average Annual pay range for an Ethical Hacker according to PayScale: $59,000 – $115,000
-
Security Operations Center (SOC) Analyst
Monitoring and analyzing the security systems of a company is one of the primary functions a security operations center analyst must undertake. They ensure that systems are safe from threats and vulnerabilities and the security posture is strong. They earn around $75,000 per year.
Besides a bachelor’s degree in a relevant field such as computer science or information technology, possessing the certified information systems security professional (CISSP) certification or the certified ethical hacker (CEH) can increase the chances of being accepted as the security operations center analyst.
Average Annual pay range for a SOC Analyst according to PayScale: $72,000 – $101,000
-
Security Administrator
A security administrator oversees the daily management and administration of an organization’s security systems. It is entrusted to them to monitor that the security framework is in place and well-implemented throughout the organization’s operations.
They need to have a degree in computer science, information systems, or a relevant field. Certification such as the certified information systems security professional (CISSP) or the certified information security manager (CISM) helps in being eligible for this role.Work experience in information security through jobs and internships with leadership qualities is sought by companies in a good security administrator. They must keep learning newer trends, threats, and developments in Cybersecurity Jobs to add value to the company’s security goals. They are paid around $73,000 per year.
Average Annual pay range for a Security Admin according to PayScale: $50,000 – $96,000
-
Security Analyst
A security analyst of a company monitors the security systems and detects threats and vulnerabilities to avoid exploitation of systems.
They earn around $71,000 per year and need a minimum of a bachelor’s degree in computer science, information technology or another relevant field to qualify. Beyond this, being certified with the certified ethical hacker (CEH) certification or the certified information systems security professional (CISSP) adds to their application for this position.
Work experience in information security, network security, and data analysis also helps in tackling potential challenges in the security infrastructure.
Average Annual pay range of a Security Analyst as on PayScale: $55,000 – $117,000
Growth opportunities Cybersecurity Jobs in 2023
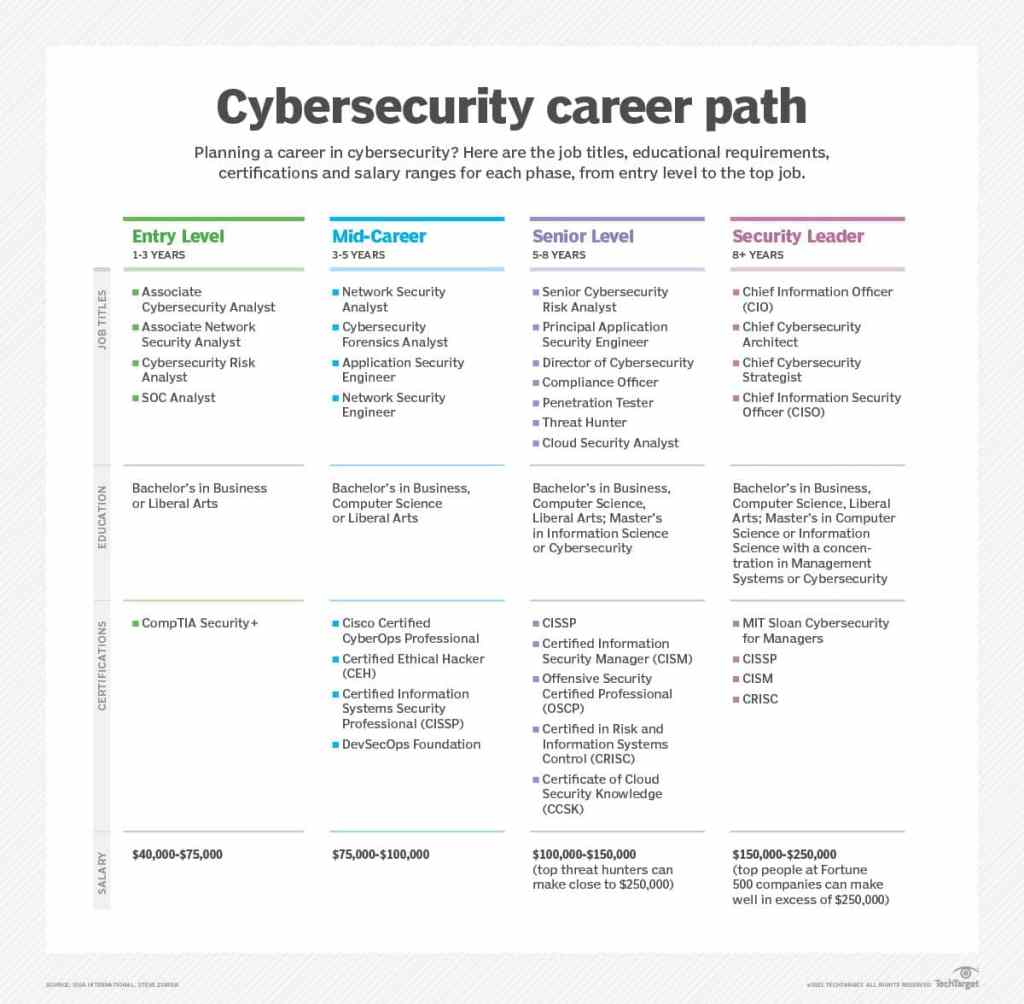
Professional growth in cybersecurity Jobs is considered to be endless when backed with relevant experience and certifications. A candidate can reach the highest position of chief information officer (CIO) after starting their career and earn nearly $200,000 per year.
Other C-level positions are chief experience officer, chief compliance officer, chief technology officer, and chief data officer among others.



















































