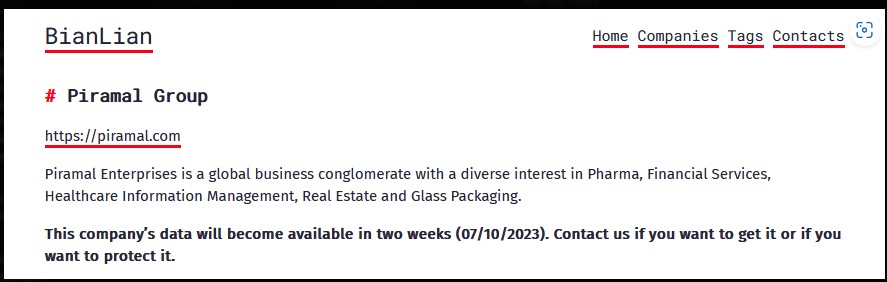
The BianLian Ransomware gang has claimed responsibility for the alleged Piramal Group cyber attack, listing the Indian business conglomerate as a victim on the ransomware gang’s leak site.
The ThreatMon Threat Intelligence team reported the alleged Piramal Group cyber attack incident on June 28, 2023. Threat intelligence service Falcon Feeds has confirmed the Piramal Group cyber attack.
The Piramal Group, an influential entity operating in sectors such as pharmaceuticals, healthcare, and financial services, has a global footprint and is widely recognized for its significant contributions to these industries.
The Piramal Group has yet to release an official statement regarding the incident.
The Cyber Express has reached out to the Corporate Communications and Investor Relations & Sustainability teams to get an official confirmation of the attack by the BianLian ransomware gang. We are yet to receive a reply.
BianLian ransomware gang and the Piramal Group cyber attack
The Piramal Group is a diversified conglomerate based in India with a global presence. It is involved in various business sectors and has established itself as a prominent player in each division.
The BianLian ransomware gang leak site post does not mention any business division it targeted in the Piramal Group cyber attack.
However, the threat actor claims to have access to 870 GB of data including financial information, accounting information of other companies, project data, technical details, and personal information.
The key divisions of the Piramal Group are:
Pharmaceuticals: The pharmaceutical division of the Piramal Group focuses on developing and manufacturing innovative medicines and healthcare products. They have a strong presence in areas such as contract development and manufacturing, over-the-counter (OTC) products, and critical care.
Financial Services: Piramal Group’s financial services division offers a wide range of financial solutions, including lending, investment banking, asset management, and real estate financing. They cater to diverse sectors such as real estate, infrastructure, renewable energy, and hospitality.
Real Estate: The group’s real estate division focuses on developing residential, commercial, and mixed-use properties. They are involved in various aspects of real estate development, including design, construction, marketing, and sales.
Philanthropy: Piramal Foundation is the philanthropic arm of the Piramal Group, an Indian conglomerate with diversified businesses. The foundation was established in 2006 with the aim of making a positive and sustainable impact on society. .
BianLian ransomware gang: Mode of operation
BianLian ransomware gang is among the most prolific ransomware groups by the number of victims.
Its recent targets include Mitcon Consultancy, St. Rose Hospital, and the Australian Real Estate Group (AREG).
In May, the Federal Bureau of Investigation (FBI), Cybersecurity and Infrastructure Security Agency (CISA), and the Australian Cyber Security Centre (ACSC) issued a cybersecurity advisory regarding the activities of the BianLian ransomware gang.
The BianLian gang has been active since at least 2019 and has been known to use multiple tactics, including phishing emails, exploit kits, and remote desktop protocol (RDP) brute-force attacks, to gain access to victims’ networks.

One of the notable characteristics of the BianLian group is their exfiltration-based extortion approach, reported Picus Security.
Initially, they employed a double-extortion model where they encrypted victims’ systems after stealing sensitive data. However, around January 2023, they shifted their focus primarily to exfiltrating data and threatening to release it unless a ransom is paid.
“BianLian group engages in additional techniques to pressure the victim into paying the ransom; for example, printing the ransom note to printers on the compromised network,” said the CISA advisory.
“Employees of victim companies also reported receiving threatening telephone calls from individuals associated with BianLian group.”
According to the CISA advisory, the group utilizes various techniques throughout their attack lifecycle.
They implant custom backdoors written in Go, install remote management and access software, and create or activate local administrator accounts.
To evade detection, BianLian actors use PowerShell and Windows Command Shell to disable antivirus tools and modify Windows Registry settings. They also employ network and Active Directory enumeration techniques and harvest credentials to move laterally within the network.
Once inside the victim’s environment, the group searches for sensitive files using PowerShell scripts and exfiltrates them using File Transfer Protocol (FTP), Rclone, or Mega file-sharing service.
They encrypt the victim’s files with a distinct .bianlian extension and leave a ransom note in each affected directory. If the victim refuses to pay the ransom, BianLian threatens to publish the exfiltrated data on a leak site maintained on the Tor network.