A new phishing campaign targeting messaging apps has triggered warnings from the Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI), highlighting how even the most secure communication platforms can be undermined by human error rather than technical flaws.
In a joint public service announcement, the agencies revealed that cyber actors linked to Russian Intelligence Services are actively targeting users of commercial messaging applications (CMAs), including high-profile individuals such as government officials, military personnel, political figures, and journalists. The goal is not to break encryption—but to bypass it entirely.
Phishing Campaign Targeting Messaging Apps Bypasses Encryption
The most striking aspect of this phishing campaign targeting messaging apps is that it does not rely on exploiting software vulnerabilities. Instead, attackers are focusing on users themselves.
Evidence shows that while encryption remains intact, thousands of individual accounts have already been compromised globally. Once attackers gain access, they can read private messages, access contact lists, send messages as the victim, and even launch further phishing attacks.
This reinforces a critical point often overlooked in cybersecurity discussions: encryption is only as strong as the user behind it.
How the Phishing Campaign Works
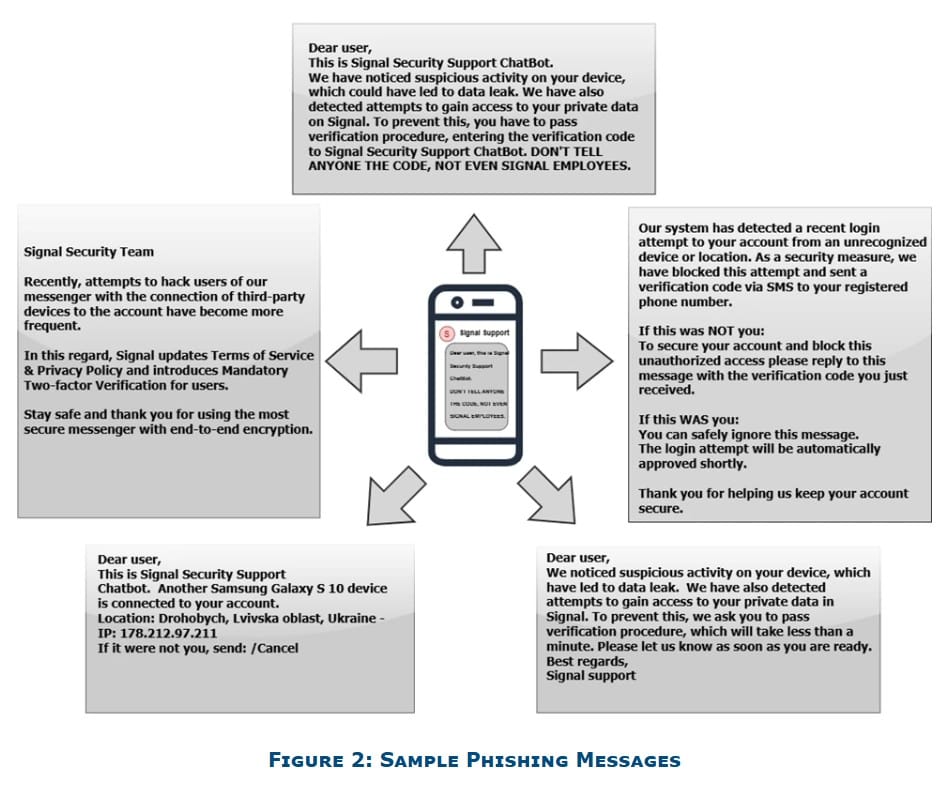
According to CISA and the FBI, the phishing campaign targeting messaging apps primarily uses social engineering tactics. Attackers impersonate official support accounts within messaging platforms, sending convincing messages that prompt users to take immediate action.
These messages may:
- Ask users to click on malicious links
- Request verification codes or PINs
- Encourage account “recovery” actions
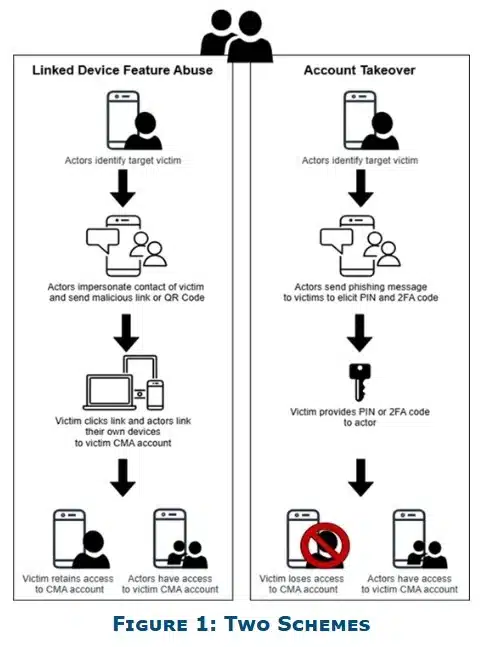
If a user complies, attackers can link their own device to the account or take full control.
In some cases, attackers may escalate their tactics by deploying malware, making the campaign more persistent and difficult to contain.
Notably, reporting suggests that platforms like Signal have been specifically targeted, though similar methods can be applied across other messaging apps.
Why This Phishing Campaign Targeting Messaging Apps Matters
The scale and simplicity of this phishing campaign targeting messaging apps make it particularly dangerous. Unlike complex cyberattacks, phishing requires minimal technical sophistication but delivers high success rates.
CISA and the FBI emphasized this reality, stating: “Phishing remains one of the most unsophisticated, yet effective means of cyber compromise, often rendering other protections irrelevant including end-to-end encryption.”
Key Recommendations for Users
To counter the risks posed by the phishing campaign targeting messaging apps, authorities are urging users to adopt basic but effective cybersecurity practices:
- Pause before responding: If something feels suspicious, do not engage or share sensitive information.
- Avoid unknown messages: Treat unexpected or unusual requests with caution, even from known contacts.
- Check links carefully: Do not click on unfamiliar or suspicious links.
- Monitor group chats: Watch for duplicate or fake accounts in conversations.
- Use built-in security features: Enable protections like message expiration where appropriate.
- Report incidents quickly: Notify security teams or report to authorities such as the Internet Crime Complaint Center (IC3).
Users are also reminded that legitimate support services do not request verification codes or send account recovery links via direct messages.
A Persistent Cyber Threat That Relies on Human Behavior
What makes this phishing campaign targeting messaging apps particularly concerning is its reliance on human behavior rather than technical weaknesses. Attackers are betting on urgency, confusion, and trust—factors that technology alone cannot fix.
The warning from CISA and the FBI is clear: users must remain vigilant. Strengthening personal cybersecurity habits is now just as important as the security features built into the platforms themselves.
As messaging apps continue to play a central role in both personal and professional communication, campaigns like this serve as a reminder that the weakest link in cybersecurity is often not the system—but the user.