US cybercrime watchdogs have issued a joint warning on a PaperCut vulnerability exploited in the wild.
The FBI and the Cybersecurity and Infrastructure Security Agency (CISA) have issued a joint Cybersecurity Advisory (CSA) in response to the active exploitation of CVE-2023-27350.
According to the agencies, Bl00dy Ransomware Gang has gained access to the victim networks via PaperCut servers vulnerable to CVE-2023-27350 exposed to the internet.
This vulnerability affects specific versions of PaperCut NG and PaperCut MF and can be exploited by unauthenticated actors to execute malicious code remotely without credentials.
Print management software PaperCut had issues patches for two vulnerabilities — CVE-2023-27350 and CVE-2023-27351 in March 2023.
CVE-2023-27350, the PaperCut vulnerability exploited in the wild, is a remote code execution flaw while the high-severity CVE-2023-27351 was a user account data flaw.
PaperCut vulnerability exploited in the wild
“According to FBI observed information, malicious actors exploited CVE-2023-27350 beginning in mid-April 2023 and continuing through the present,” said a CISA announcement.
In early May 2023, also according to FBI information, a group self-identifying as the Bl00dy Ransomware Gang attempted to exploit vulnerable PaperCut servers against the Education Facilities Subsector.
The Bl00dy Ransomware Gang gained access to the victim networks across the Education Facilities Subsector where PaperCut servers vulnerable to CVE-2023-27350 were exposed to the internet.
Ultimately, this led to data exfiltration and encryption of victim systems. The Bl00dy Ransomware Gang left ransom notes on victim systems, demanding payment in exchange for decryption of encrypted files.
The PaperCut vulnerability exploited in the wild allows remote actors to bypass authentication and conduct remote code execution on affected installations of PaperCut.
Vulnerable PaperCut servers implement improper access controls in the SetupCompleted Java class, which allows malicious actors to bypass user authentication and access the server as an administrator.
Once accessed, actors can leverage existing PaperCut software features for remote code execution.
There are currently two publicly known proofs of concept for achieving RCE in vulnerable PaperCut software: using the print scripting interface to execute shell commands and using the User/Group Sync interface to execute a living-off-the-land-style attack.
Trend Micro discovered this vulnerability in March 2023 and alerted the company, after which the company issued a patch. The critical severity bug CVE-2023-27350 had a base score of 9.8, according to a PaperCut report.
The PaperCut vulnerabilities
The two vulnerabilities were publicly disclosed by PaperCut in March 2023. CVE-2023-27350 was a remote code execution flaw while the high-severity CVE-2023-27351 was a user account data flaw.
“The specific flaw (CVE-2023-27350) exists within the SetupCompleted class. The issue results from improper access control. An attacker can leverage this vulnerability to bypass authentication and execute arbitrary code in the context of SYSTEM,” said the Trend Micro advisory.
Even if your PaperCut application server isn’t directly reachable over the internet, could exploit this bug to pivot, or move laterally (which are fancy jargon words for “make the jump”), to a more privileged and powerful position inside your business, warned a Sophos advisory.
For that, the attacker should already have a basic foothold in your network, for example as a guest user on someone’s infected laptop, it explained.
While the former showed instances of being exploited in the wild, the latter did not, the company said in March.
The vulnerability bulletin by PaperCut read: “Please note that as of 18 April 2023 (see “When was the exploit first detected in the wild?” in the FAQs) we have evidence to suggest that unpatched servers are being exploited in the wild, (particularly ZDI-CAN-18987 / PO-1216).”
Unpatched systems are still exposed to hackers that can retrieve hashed passwords from PaperCut-created user accounts. Usernames, full names, email addresses, work-related data, and financial data from cards can also be accessible upon exploitation.
The Cyber Express has been tracking instances of the vulnerability being exploited in the wild over the past few weeks. A PaperCut executive replied to our requests for comments: “As you can imagine we’re 100% focused on our customers at the moment. We’ll have more to share publicly over time.”
Details of the PaperCut vulnerability exploited in the wild
The exploit for the PaperCut vulnerability CVE-2023-27350 was predicted to expose nearly 87 systems from Australia belonging to small and big education entities, according to OSINT. The exploitation has been ongoing on unpatched devices since mid-April with the earliest instance discovered on April 14, 2023.
CVE-2023-27351 or ZDI-23-233 was an improper access control authentication bypass bug that did not need to be approved to gain access. The vulnerabilities were alerted about through Trend Micro’s Zero Day Initiative (ZDI).
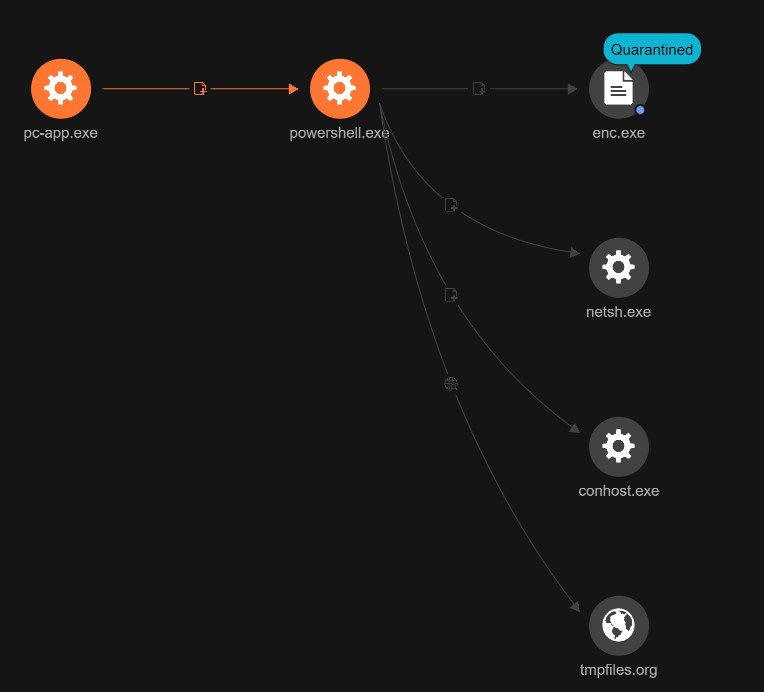
In one instance detected by researchers of the PaperCut vulnerability exploited in the wild showed that hackers ran a PowerShell script that in turn downloaded and ran a payload. To evade firewall detection, the malicious software used netsh.exe.
Moreover, it was found that the presently undetected hackers exploiting the PaperCut vulnerability in the wild used a temporary hosting site that deleted all the uploaded files after 60 minutes of its use.
The found binary in the Download folder of the targeted system led to the firm belief that the ransomware was of LockBit.
PaperCut released patches for PaperCut MF and PaperCut NG – 20.1.7, 21.2.11, and 22.0.9 to secure vulnerable systems.
The products that are vulnerable to the CVE-2023-27350 include PaperCut MF/ PaperCut NG version 8.0 or later, across platforms. PaperCut MF/ PaperCut NG Application Servers and PaperCut MF/ PaperCut NG Site Servers.
PaperCut, the print management software solution has a customer base of nearly 100 million globally.
To mitigate the threat posed by the PaperCut vulnerability exploited in the wild, FBI and CISA strongly encourage users and administrators to immediately apply patches and workarounds if unable to patch.
If potential compromise is detected, organizations should apply the incident response recommendations included in the CSA.
FBI and CISA recommend organizations to upgrade PaperCut to the latest version. If they are unable to patch immediately, they should ensure vulnerable PaperCut servers are not accessible over the internet and implement network controls.
In addition, organizations should follow best cybersecurity practices in their production and enterprise environments, including mandating phishing-resistant multifactor authentication (MFA) for all staff and services, the advisory said.