In the aftermath of a successful takedown of Alphv ransomware infrastructure, an unexpected alliance has emerged. LockBit and BlackCat/APLHV, two prominent hacker collectives, have come together in an attempt to establish a ransomware cartel, presenting a unified front against crackdowns like the recent FBI action targeting ALPHV’s leak website.
The announcement came through cryptic messages posted on the dark web, where these cybercriminals usually communicate and plan their illicit activities.
Amidst these shifts, social media is buzzing with reactions, discussing the dynamics of this collaboration.
Tim Pappa, a certified former FBI profiler specializing in cyber deception and online influence, shared insights with The Cyber Express.
“This exchange is surely designed to manage impressions. It’s not a private conversation. This is a performance. Well, we might be seeing a real agreement; the agreement is likely on Lockbit’s terms given what has happened. The Lockbit collective and Lockbitsupp have always been keenly focused on managing impressions. Historically, they are especially reactive to any criticism or question of trust or distrust among their affiliates.” The opportunity to appear to be a benefactor to the communities of affiliates and ransomware personalities is surely a gift for Lockbit, worth more than any ransom pay day. This is a narrative that is purely opportunistic for Lockbit.”
Expanding on this, he added, “The LockBit collective and Lockbitsup typically express themselves in terms of principle and honor. This situation is another reflection of that ethos. LockBit is essentially conveying that we are here for each other; one day, it might be me in BlackCat’s position, and we look out for each other. If the true terms of this so-called agreement, hashed out in secret, were revealed, ransomware communities would likely perceive it differently.”
On the other hand, a Cyble researcher aptly notes that the seemingly diplomatic discourse may be a strategic move by BlackCat to mitigate the fallout from LOCKBIT’s attempts to poach their affiliates.
According to him, the ongoing battle for affiliates became evident when LOCKBIT sought to recruit from N0_Esc4pe and BlackCat groups. Speculation arises as to whether some affiliates, seeking improved operational security, might have defected to LOCKBIT.
Despite BlackCat’s efforts to project business as usual on their leak site, signs of disorientation emerge. The intricate dance between these cyber adversaries underscores the constant evolution and strategic maneuvers within the shadowy realms of ransomware cartels.
“Overall its a very preliminary situation and too early to conclude a collaboration because there are too many buts considering their history and being staunch rivals. We may have heard resentment from LOCKBIT affiliates but not much from BlackCat,” said Cyble Researcher.
Another user, @3xp0rtblog notably pointed out Alphv’s admission of mistakes, appreciation for LockBit’s backing, and their joint stance against the FBI’s actions.
Meanwhile, vx-underground’s tweet emphasized the unexpected show of mutual respect between ALPHV and Lockbit’s leadership, hinting at talks to establish the ALPHV/Lockbit ransomware cartel.
A Veiled Acknowledgment: BlackCat’s Message of Unity
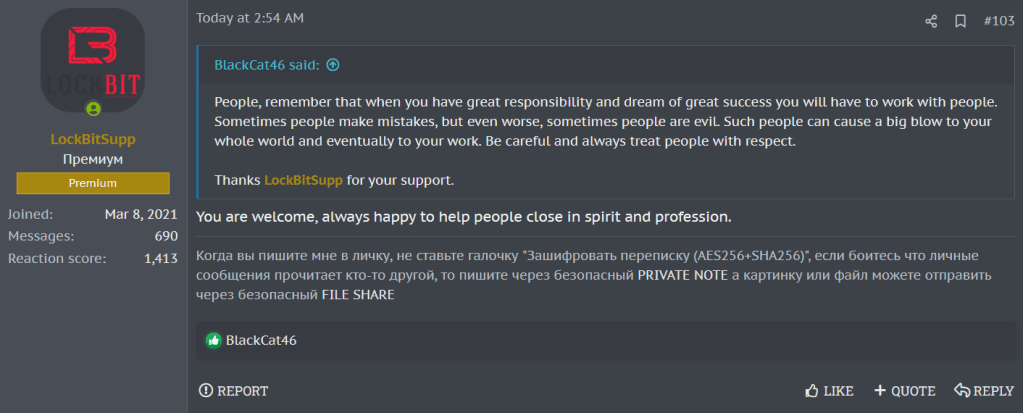
ALPHV/BlackCat initiated the conversation with an enigmatic message on the dark web, emphasizing the need for unity among hackers in the face of adversity.
The message contained a veiled reference to recent events, thanking LockBitSupp for their support. LockBit, in turn, replied with gratitude and expressed their willingness to support like-minded individuals.
A bystander on the dark web, recognizing the unusual camaraderie between two fierce rivals, commended their professionalism.
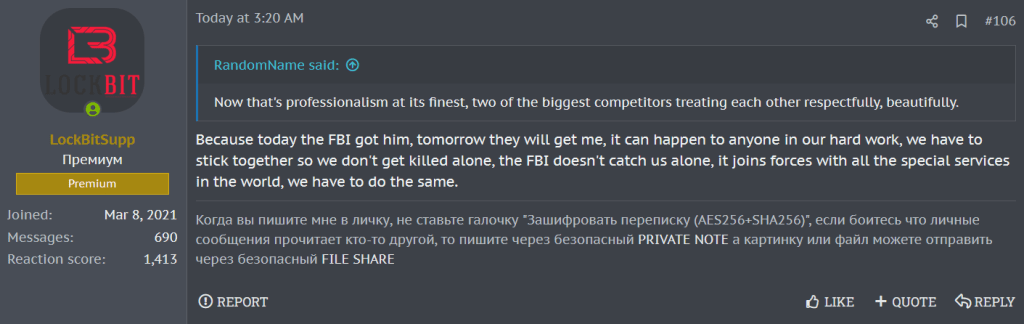
LockBit responded, shedding light on the harsh reality of their perilous profession. They highlighted the constant threat of law enforcement agencies worldwide and advocated for unity to face these challenges collectively.
“The FBI doesn’t catch us alone; it joins forces with all the special services in the world; we have to do the same,” warned LockBit.
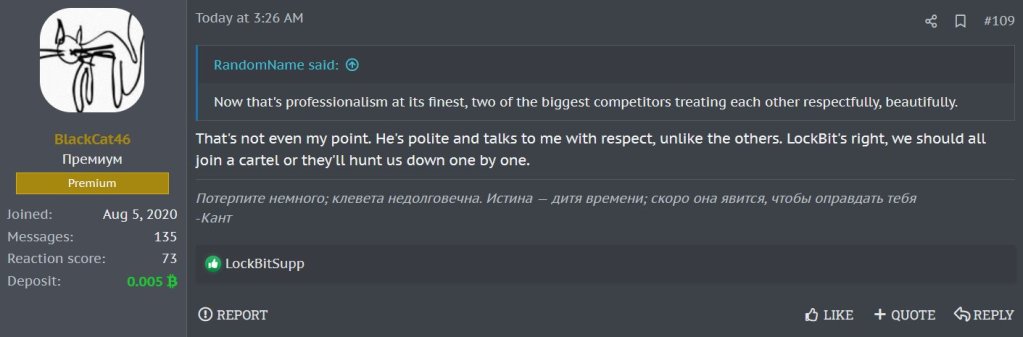
In a surprising turn, BlackCat responded, emphasizing the importance of mutual respect and collaboration. “LockBit’s right, we should all join a cartel or they’ll hunt us down one by one,” BlackCat asserted.
The statement suggests that these cybercriminals recognize the strength in numbers and the need to stand united against the growing pressure from global law enforcement agencies.
This collaboration between LockBit and BlackCat is particularly alarming given their notorious histories. Both groups have been implicated in major cyberattacks, and their union could amplify the scale and impact of their future operations.
The potential formation of a hackers’ cartel raises concerns about the sophistication and audacity of cybercriminals, posing a significant challenge to cybersecurity efforts worldwide.
This development follows the recent disruption of the BlackCat ransomware group by the U.S. Department of Justice (DOJ) and the FBI’s efforts.
Despite the FBI’s success in developing a decryption tool and seizing the BlackCat threat group’s website, the hackers retaliated by reestablishing control and issuing a defiant message directed at the FBI.
Implications of LockBit and BlackCat Collaboration
The unexpected collaboration between LockBit and BlackCat raises significant concerns within the cybersecurity world. If this alliance materializes into a full-fledged hackers’ cartel, the potential consequences could be far-reaching and impactful, albeit challenging to predict with certainty.
Shift in Threat Landscape: The collaboration signifies a strategic shift in the tactics employed by cybercriminals. Traditionally viewed as individual entities competing for dominance, this collaboration highlights a recognition among hackers that collective strength may provide a more enhanced defense against law enforcement efforts.
Increased Operational Scale: A merger between LockBit and BlackCat would likely result in a considerable increase in operational scale and sophistication. Combining the expertise and resources of two formidable groups could lead to more potent and widespread cyberattacks, posing a heightened challenge for cybersecurity professionals and organizations.
Global Cybersecurity Challenges: The formation of a hackers’ cartel would necessitate an enhanced, coordinated response from global cybersecurity forces. The collaboration of two major threat groups could potentially lead to a surge in cyber threats, requiring international cooperation to mitigate the risks effectively.
Adaptation of Defense Strategies: The cybersecurity community would need to adapt its defense strategies to counter this evolving threat landscape. Collaboration among cybercriminals demands a mature and united response from defenders, emphasizing the importance of information sharing and joint efforts in mitigating the impact of cyber threats.
Increased Regulatory Scrutiny: The collaboration may prompt increased regulatory scrutiny and international collaboration among law enforcement agencies. As cybercriminals join forces, governments, and regulatory bodies are likely to intensify efforts to strengthen legal frameworks and enhance cross-border cooperation to combat cybercrime effectively.
Heightened Importance of Cybersecurity Education: In the face of a growing and collaborative cyber threat, the importance of cybersecurity education and awareness becomes even more critical. Businesses, governments, and individuals must prioritize cybersecurity measures to minimize vulnerabilities and potential impacts of cyberattacks.
The impact of this unholy alliance remains to be seen, but one thing is certain: the digital world is witnessing a new era of collaboration among cybercriminals that demands a united response from global authorities.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.