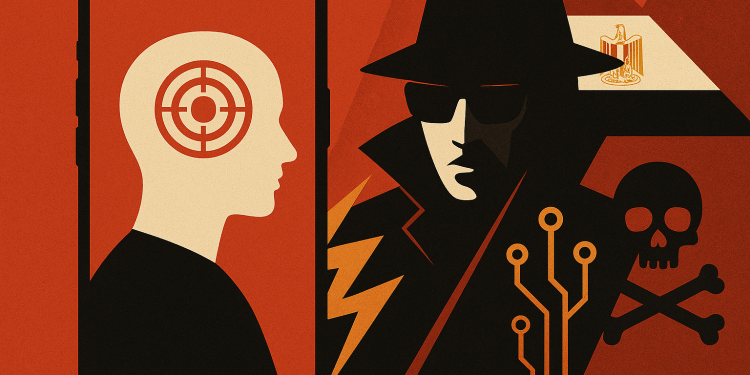
Google Threat Intelligence Group discovered a full iOS zero-day exploit chain deployed in the wild against targets in Egypt, revealing how sanctioned commercial surveillance vendor Intellexa continues purchasing and deploying digital weapons despite US government restrictions and extensive public scrutiny—underscoring the critical role of Cyber Threat Intelligence Platforms in uncovering and tracking such advanced attacks.
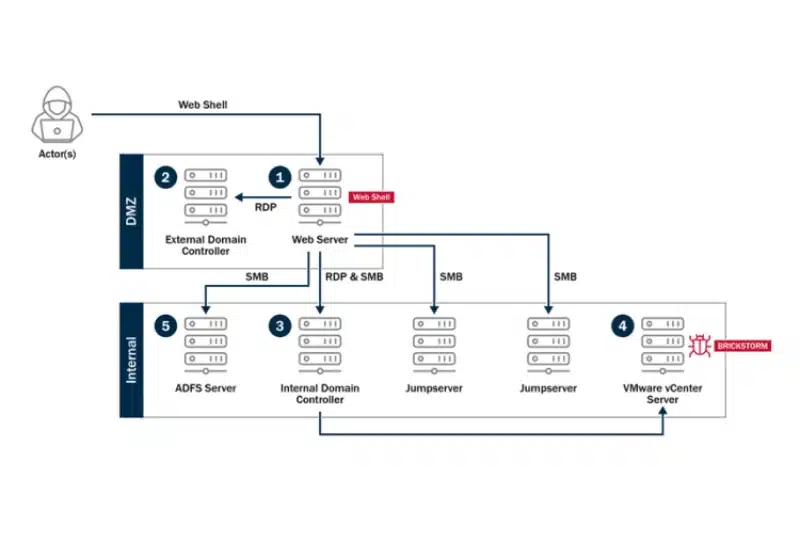
The three-stage attack chain was developed by Intellexa to install its Predator spyware onto victim devices, which is known to act as a surveillance tool for its government clients worldwide.
Google researchers partnered with CitizenLab in 2023 to capture and analyze the complete exploit chain after identifying attacks targeting individuals in Egypt. According to metadata, Intellexa referred to this exploit chain internally as “smack,” with compilation artifacts revealing the build directory path including the codename.
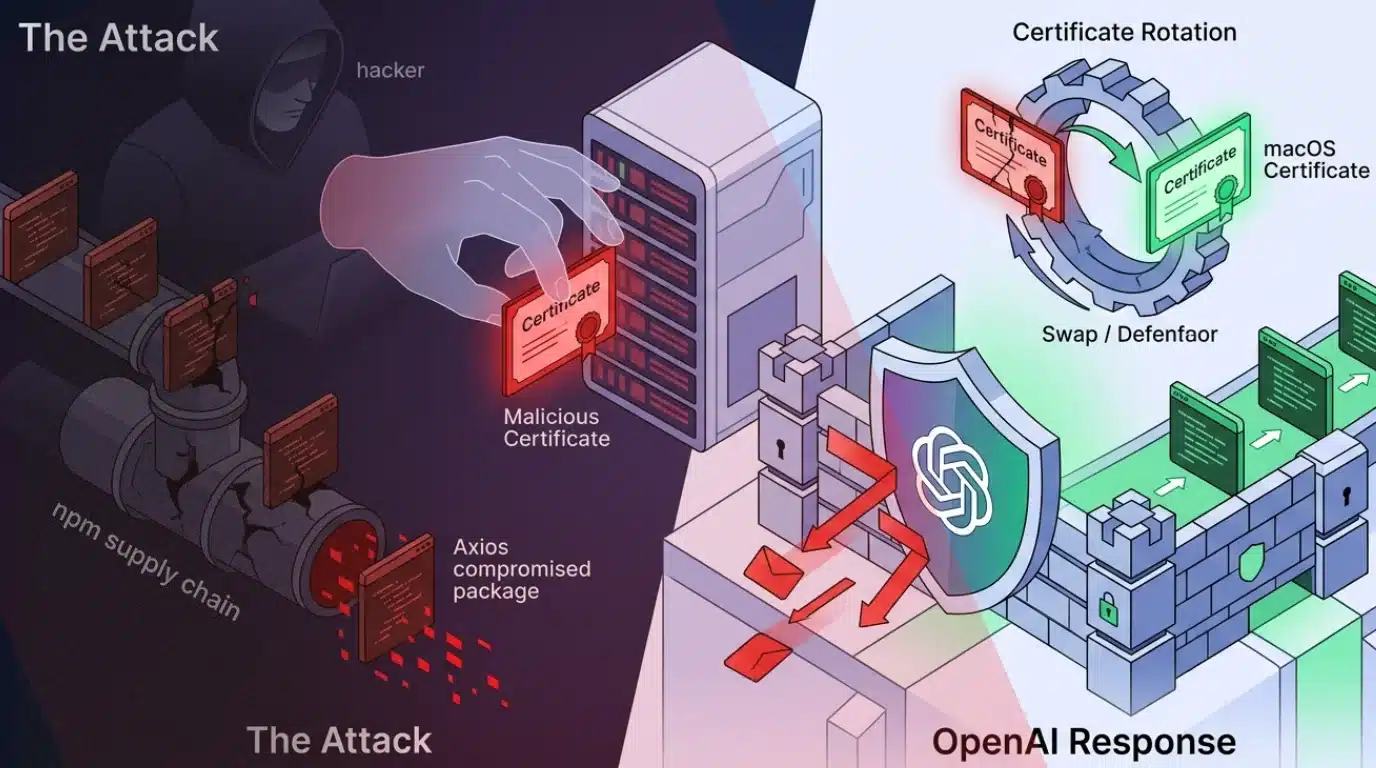
First Stage: Purchased Safari Exploit
The initial stage leveraged a Safari remote code execution zero-day that Apple patched as CVE-2023-41993. The exploit utilized a framework internally called “JSKit” to achieve arbitrary memory read and write primitives, then execute native code on modern Apple devices.
Google researchers assessed with high confidence that Intellexa acquired its iOS RCE exploits from an external entity rather than developing them internally. The identical JSKit framework has appeared in attacks by other surveillance vendors and government-backed threat actors since 2021.
In 2024, Google publicly reported that Russian government-backed attackers used this exact same iOS exploit and JSKit framework in a watering hole attack against Mongolian government websites.
Read: Russian State Hackers Using Exploits ‘Strikingly Similar’ to Spyware Vendors NSO and Intellexa
The framework also appeared in another surveillance vendor’s exploitation of CVE-2022-42856 in 2022. The JSKit framework is well-maintained, supports a wide range of iOS versions, and is modular enough to support different Pointer Authentication Code bypasses and code execution techniques. The framework can parse in-memory Mach-O binaries to resolve custom symbols and manually map and execute Mach-O binaries directly from memory, with each exploitation step tested carefully.
Debug strings at the RCE exploit entry point indicated Intellexa tracked it internally as “exploit number 7,” suggesting the external supplier likely possesses a substantial arsenal of iOS exploits targeting various versions.
Second Stage: Sandbox Escape and Privilege Escalation
The second stage represents the most technically sophisticated component of the chain, breaking out of the Safari sandbox and executing an untrusted third-stage payload as system by abusing kernel vulnerabilities CVE-2023-41991 and CVE-2023-41992. This stage communicates with the first stage to reuse primitives like PAC bypass and offers kernel memory read and write capabilities to the third stage.
The technical sophistication of these exploits, especially compared to the less sophisticated spyware stager, supports Google’s assessment that Intellexa likely acquired the exploits from another party rather than developing them internally.
Third Stage: Spyware Deployment and Anti-Detection
The third stage, tracked by Google Threat Intelligence Group as PREYHUNTER, comprises two modules called “helper” and “watcher.” The watcher module ensures the infected device does not exhibit suspicious behavior, generating notifications and terminating the exploitation process if anomalies are detected while monitoring crashes.
The module detects multiple indicators including developer mode, console attachment, US or Israeli locale settings, Cydia installation, presence of security research tools like Bash, tcpdump, frida, sshd or checkrain processes, antivirus software from McAfee, Avast or Norton, custom HTTP proxy setup, and custom root certificate installation.
The helper module communicates with other exploit components via a Unix socket and can hook various system functions using custom frameworks called DMHooker and UMHooker. These hooks enable basic spyware capabilities including recording VOIP conversations, running keyloggers, and capturing pictures from the camera. The module hooks into SpringBoard to hide user notifications caused by surveillance actions.
Google researchers believe these capabilities allow operators to verify the infected device is the correct target before deploying more sophisticated spyware like Predator.
Prolific Zero-Day Exploitation Record
Intellexa is responsible for 15 unique zero-day vulnerabilities out of approximately 70 discovered and documented by Google’s Threat Analysis Group since 2021, including Remote Code Execution, Sandbox Escape, and Local Privilege Escalation vulnerabilities. All have been patched by respective vendors.
Beyond iOS exploitation, Intellexa deployed a custom Chrome framework with CVE-2021-38003, CVE-2023-4762, CVE-2023-3079, CVE-2023-2033, and most recently CVE-2025-6554 in June 2025, observed in Saudi Arabia. All these vulnerabilities in Chrome’s V8 engine can leak TheHole object for code execution.
Google delivered government-backed attack warnings to several hundred accounts across Pakistan, Kazakhstan, Angola, Egypt, Uzbekistan, Saudi Arabia, and Tajikistan associated with Intellexa customers since 2023. The company added all identified websites and domains to Safe Browsing to safeguard users from further exploitation.