IBM’s annual Cost of a Data Breach Report released today found that the global average cost of a data breach grew by 10% to $4.88 million in 2024, as breaches have become more disruptive and often overwhelmed security teams.
One bright note: The IBM-Ponemon report – now in its 19th year – found that organizations that extensively use AI and automation across prevention workflows saved $2.2 million on average data breach cost over organizations that aren’t using those technologies.
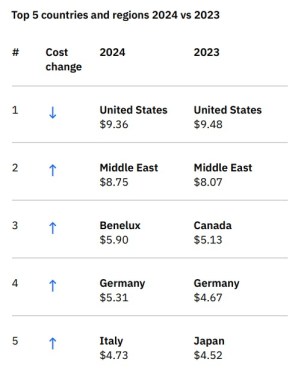
In the U.S., the average data breach cost actually declined – from $9.48 million in 2023 to $9.36 million in 2024 – yet remains the highest in the world, followed by the Middle East region, which saw the average breach cost increase from $8.07 million to $8.75 million. If current trends continue, the Middle East could overtake the top spot from the U.S. as early as 2025.
Mega breaches – defined as a million or more records compromised – were excluded from the calculations because of their huge cost, starting around $42 million per breach.
Healthcare, Breach Containment Time Improve
Among industries, healthcare took the top spot again, even as the cost per breach dropped substantially, from $10.93 million to $9.77 million. Financial firms were a distant second at $6.08 million, up slightly over 2023. Here’s the data broken down by industry:

The average time to identify and contain a breach fell to a 7-year-low of 258 days. Compromised credential and insider breaches took even longer to contain (chart below).

The most common initial attack vectors were:
- Stolen or compromised credentials (16%)
- Phishing (15%)
- Cloud misconfiguration (12%)
- Unknown zero-day vulnerability (11%)
- Business email compromise (10%)
- Malicious insider (7%)
Social engineering, known unpatched vulnerabilities, accidental data loss and stolen devices, physical security compromise, and system errors all came in at around 6% each.
Factors Contributing to Data Breach Cost
Factors contributing to higher breach costs included understaffed security teams, shadow data, and data spread across multiple environments.
AI tools, along with detection by internal tools and teams (as opposed to hearing from third parties or attackers), were positive factors, and bringing in law enforcement in ransomware cases saved nearly $1 million per incident, and 63% of ransomware victims who involved law enforcement were able to avoid paying a ransom.
Interestingly, any investment in AI and automation saved on breach costs (chart below).

Also noteworthy, the IBM report includes an extensive look at the security tools and factors that decreased breach costs, in descending order:

Data Breach Recovery Takes Time
Only 12% of the organizations queried in the report said they had fully recovered from the breach.
In the context of the study, full recovery from a breach means:
- Business operations back to normal in areas affected by the breach.
- Compliance obligations met, including paying fines.
- Customer confidence and employee trust restored.
- Controls, technologies and expertise in place to avoid future breaches.
That third point – customer confidence – is the toughest to restore, and a reason to invest in effective cybersecurity controls in the first place.