Several chunks of data belonging to Hewlett Packard Enterprise (HPE) are purportedly up for sale on the dark web. The disclosure about this alleged Hewlett Packard Enterprise data breach came through a post on February 1st by a lone hacker known as IntelBroker, who claimed to possess critical information about the organization.
IntelBroker’s claim includes having obtained CI/CD access, system logs, config files, access tokens, and passwords related to HPE. The hacker’s post on BreachForums Community states, “[Cyber Niggers] Hewlett Packard Enterprise by IntelBroker,” and provides details of the data on sale, including HPE StoreOnce files and access passwords, with an explicit mention of email services.
Hewlett Packard Enterprise Data Breach Dark Web Claims
The Hewlett Packard Enterprise data leak post reads “Hello Breach Forums Community. Today, I am selling the data I have taken from Hewlett Packard Enterprise. More specifically, the data includes: /CD access, System logs, Config Files, Access Tokens, HPE StoreOnce Files (Serial numbers warrant, etc) & Access passwords. ”

The post was also accompanied by screenshots of code provided as sample data to the dark web users. The shared code, presented in JSON format, delineates configurations for different tags such as “Observer,” “iLO,” and “vmware.” Each tag comprises username and password credentials, along with additional parameters for specific tags like “ilo_host” for the “iLO” tag.
Network configuration details, including IP addresses, subnet masks, gateways, and DNS settings, are provided under the “networks” key. The code also contains a section for “test_clients,” offering insights into capabilities, credentials, and networks, showcasing an example entry for an SMTP server.
The snippets suggest the involvement of REST API calls, including information about endpoints, methods (GET or POST) and input JSON data.
The Cyber Express reached out to Hewlett Packard Enterprise for a statement regarding the alleged data breach. In response, a spokesperson for Hewlett Packard Enterprise stated, “Based on our investigation so far, the data at issue appears to be related to information that was contained in a test environment. There is no indication these claims relate to any compromise of HPE production environments or customer information. “
The Previous HPE Data Breach
Notably, HPE recently disclosed a cyberattack orchestrated by the Russian state-sponsored actor APT29, also known as Cozy Bear or Midnight Blizzard. Microsoft’s security team detected the sophisticated nation-state attack on HPE’s corporate systems on December 12, 2023.
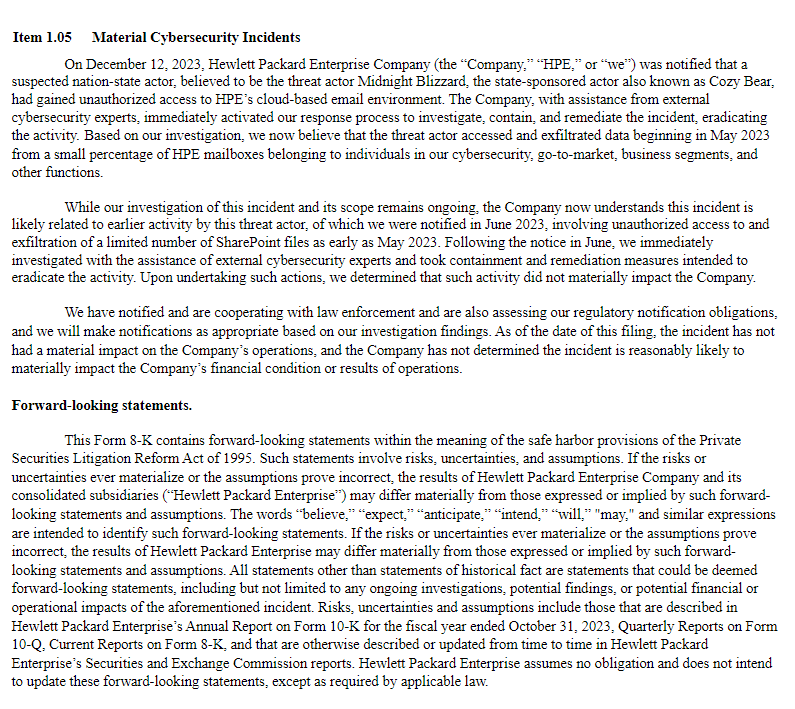
The threat actor, identified as Midnight Blizzard or Cozy Bear, gained unauthorized access to HPE’s systems. HPE promptly initiated an investigation, containment, and remediation efforts with the assistance of external cybersecurity experts, successfully eradicating the malicious activity.
The investigation revealed that the threat actor had accessed and exfiltrated data starting in May 2023 from a limited number of HPE mailboxes, particularly those belonging to individuals in cybersecurity, go-to-market, business segments, and other functions.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.