Zyxel Firewalls have become a key target in recent cyberattacks, with attackers exploiting a critical vulnerability to deploy the dangerous Helldown ransomware. The German CERT (CERT-Bund) has issued a warning alongside Zyxel detailing the extent of these attacks and outlining immediate steps that organizations must take to protect their network devices.
The attacks are tied to a vulnerability, CVE-2024-11667, within the Zyxel ZLD firmware that affects the Zyxel ATP and USG FLEX firewall series. Five German entities are believed to have been targeted by these attacks, stressing the growing risks of leaving such vulnerabilities unpatched.
CVE-2024-11667 Vulnerability in Zyxel Firewalls

The core issue is CVE-2024-11667, a directory traversal vulnerability in the Zyxel ZLD firmware (versions 4.32 to 5.38). This flaw allows attackers to bypass security measures and upload or download files via specially crafted URLs. By exploiting this vulnerability, cybercriminals can gain unauthorized access to the system, steal credentials, and create backdoor VPN connections, often without the knowledge of network administrators.
The devices that are most at risk are those running ZLD firmware versions between 4.32 and 5.38, with remote management or SSL VPN enabled. Importantly, devices managed through the Nebula cloud management system are not affected by this vulnerability.
The Rise of Helldown Ransomware
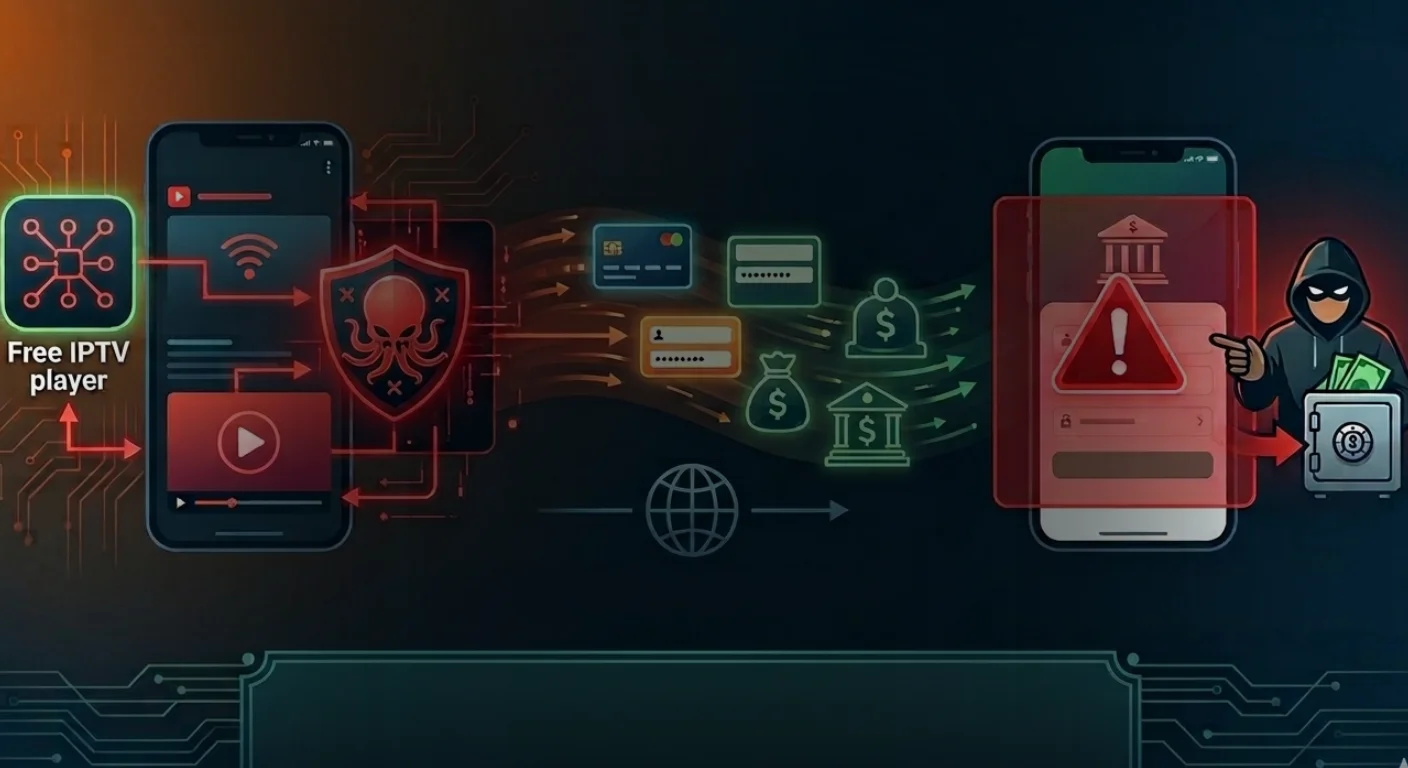
Helldown ransomware, first observed in August 2024, has quickly evolved into a malicious threat, leveraging CVE-2024-11667 to target vulnerable Zyxel firewalls. Helldown, which is derived from the infamous LockBit ransomware builder, uses advanced techniques to infiltrate networks and move laterally, often with the intent to encrypt valuable data and disrupt operations.
As of now, Helldown’s leak site has listed 32 victims worldwide, including five organizations in Germany, according to CERT-Bund. The ransomware’s ability to exploit this vulnerability is concerning, as even systems that have been patched may remain vulnerable if attackers can gain access using unchanged administrator credentials.
How the Attack Unfolds
The primary attack vector is the exploitation of the CVE-2024-11667 vulnerability to gain initial access to the targeted systems. Once inside, attackers often employ sophisticated post-exploitation tactics, including the creation of unauthorized user accounts such as “SUPPORT87” and “SUPPOR817.”
These accounts are used to facilitate lateral movement within the network, establishing persistent backdoors that allow for continued access even after the initial breach. The impact of these attacks is significant: organizations have reported data exfiltration, encryption of critical files, and operational disruptions, often with the goal of demanding a ransom for the decryption of files.
Identifying Compromise: Key Indicators
Organizations using Zyxel firewalls should be alert for signs that their systems have been compromised. Some of the key indicators include:
- Logs showing unusual VPN connections from unknown accounts such as “SUPPORT87” or “VPN” are a red flag. Attackers may also use VPN services to mask their IP addresses.
- Changes to firewall rules, such as unrestricted access between WAN, LAN, and SSL VPN zones, can indicate a breach. Similarly, attackers may alter NAT rules to allow unauthorized access from the WAN to the LAN.
- Unexplained logins or the creation of unauthorized admin accounts could suggest malicious activity. Security logs may show unusual administrative actions, especially those from unfamiliar IP addresses.
- Attackers may use stolen credentials to access Active Directory (AD) servers, potentially leading to the encryption of files stored within these systems.
Conclusion
Organizations using Zyxel firewalls should act quickly to detect and fix potential compromises by reviewing VPN logs, inspecting SecuReporter for suspicious activity, and checking firewall rules. Remediation involves upgrading to ZLD 5.39, changing passwords, removing unauthorized accounts, and tightening security policies.
Zyxel advises disabling unnecessary remote access, changing default ports, enabling two-factor authentication (2FA), and using Geo-IP filtering. Regular backups, encryption, and continuous monitoring are essential for securing systems. The rise of Helldown ransomware highlights the need for better security measures, including timely firmware updates and strong access controls.