Google has released new details on how artificial intelligence (AI) is being used across its platforms to combat a growing wave of online scams. In its latest Fighting Scams in Search report, the company outlines AI-powered systems that are already blocking hundreds of millions of harmful results daily and previews further enhancements being rolled out across Google Search, Chrome, and Android.
The move comes as part of a broader push to address evolving scam tactics—from fake customer service numbers and phishing websites to misleading browser notifications and fraudulent tech support messages.
AI-Driven Improvements to Google Search Results
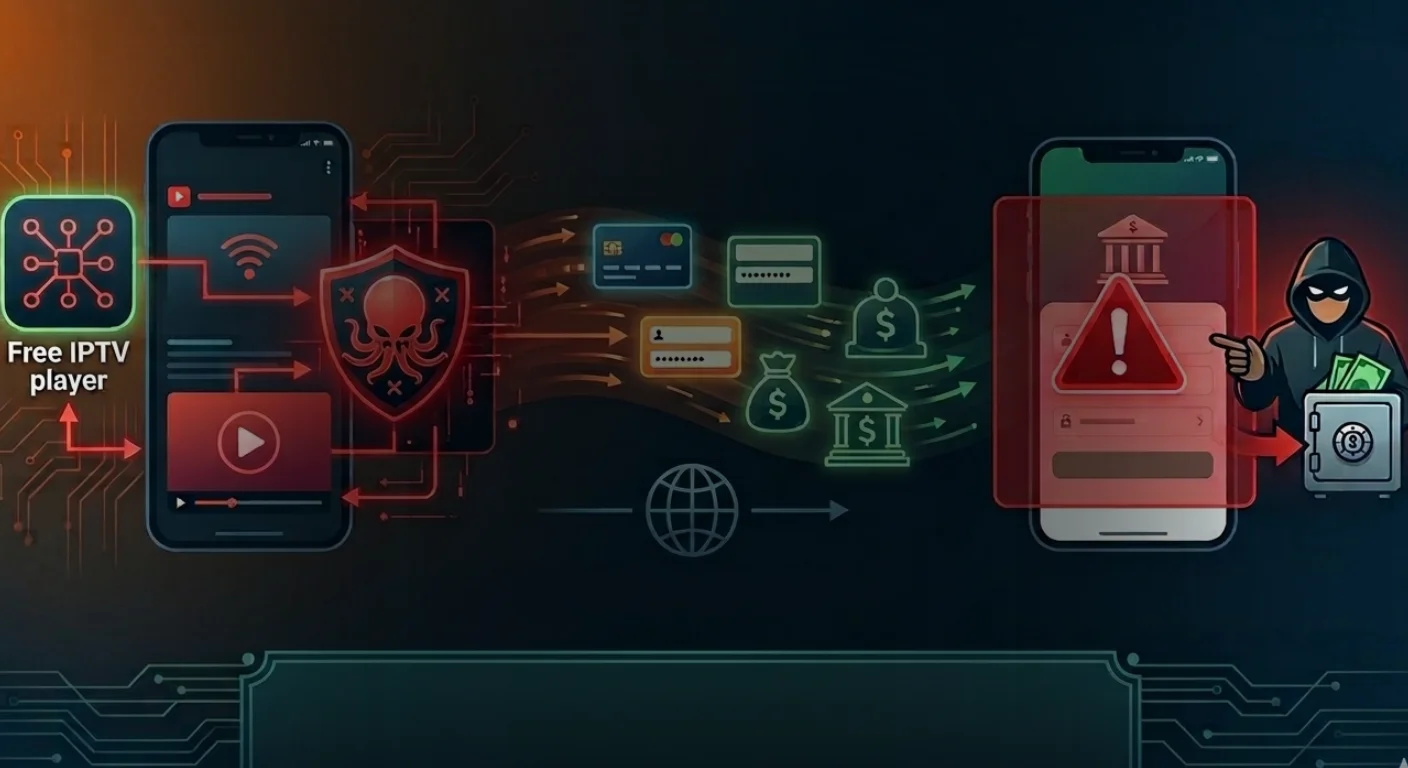
Scams that exploit search engines to mislead users into clicking harmful links or dialing fraudulent support lines have become increasingly organized. According to Google, updates to its AI-powered detection systems have enabled it to identify and remove deceptive content at a much higher rate than before.
Specifically, improvements to its classification models have led to a 20-fold increase in the number of scam pages being caught. These changes allow Search to more effectively block results that may try to harvest personal information, install malware, or promote fraudulent services.
One example detailed in the report involves fake airline customer service numbers—a scam that preys on users seeking flight assistance. By applying advanced AI to analyze and flag these patterns, Google has reduced such scams by over 80% in Search results.
The company says these AI systems are now better equipped to detect coordinated scam campaigns and new cyber threat trends by analyzing web content at scale, including subtle language shifts and emerging fraud signals.
Gemini Nano Brings On-Device Protection to Chrome
Beyond Search, Google is turning to on-device artificial intelligence to enhance browser security. A key update comes in the form of Gemini Nano, Google’s compact large language model now integrated into the Enhanced Protection mode of Chrome.
Gemini Nano operates directly on the user’s device, analyzing websites in real-time to detect potentially fraudulent behavior—particularly useful for scams that emerge quickly and may not yet be included in blocklists or threat databases.
Chrome’s Enhanced Protection mode already offers higher security standards compared to the default setting, with Google reporting it makes users twice as safe from phishing and other web-based threats. The addition of Gemini Nano enables faster detection and more adaptive responses to scams, especially those involving fake tech support alerts.
Currently, the system is being used to counter remote tech support scams, where users are tricked into believing their devices are compromised and are pressured into handing over control or making payments. Google says this feature will eventually expand to Android devices and cover a broader range of scam types.
Smarter Notification Controls on Android
Web-based scams have also shifted tactics by using browser notification permissions to push deceptive messages directly to users’ devices. To counter this, Chrome on Android is introducing new AI-driven warnings that aim to block scammy or spam-like notifications before they reach users.
The feature relies on on-device machine learning to assess the content and behavior of sites requesting notification access. If a site is flagged, users receive a warning and can either opt out of notifications or proceed to view the message. The system includes an override option for users who believe a warning was issued in error.
This update is designed to reduce the misuse of push notifications by malicious actors who exploit them for scams, fake alerts, or misleading content.
Call and Message Protection Using On-Device AI
Scams initiated through calls and text messages continue to affect mobile users, with many involving impersonation, urgent requests, or links to fraudulent websites. To address this, Google has introduced AI-powered scam detection into its Messages and Phone by Google apps on Android.
Unlike cloud-based filters, these systems operate entirely on-device, allowing them to function without internet access and minimizing privacy concerns. The AI models analyze patterns and language cues commonly associated with scams—such as requests for sensitive details or coercive tactics—and warn users before a risky interaction progresses.
This layer of protection is aimed at detecting increasingly sophisticated scam methods that often appear harmless at first but can quickly escalate into harmful situations.
A Strategic Shift Toward Localized, Adaptive Protection
The recent developments reflect a broader shift in Google’s security strategy—one that favors local, real-time AI capabilities over centralized scanning or delayed responses. By embedding AI models like Gemini Nano directly into devices and apps, Google can respond more quickly to emerging threats and adapt to new scam tactics as they develop.
This approach also supports user privacy by processing sensitive data locally rather than transmitting it to cloud servers for analysis.
While the tools outlined in the Fighting Scams in Search report mark an improvement in automated defenses, the company acknowledges that no system can catch every threat. Ongoing user awareness and regular software updates remain essential.
Key Features Rolling Out
- Search Protection: AI systems block scammy search results, reducing fake support scams by over 80%.
- Chrome Enhanced Protection: Uses Gemini Nano for on-device scam detection, starting with tech support fraud.
- Android Notification Control: AI-powered prompts block spammy or malicious site notifications.
- Call & Message Defense: On-device AI in Google Messages and Phone detects scam patterns in real-time.
Staying Ahead of Online Threats
The arms race between scam operators and security systems is ongoing. As scam tactics grow more coordinated and harder to detect, Google is betting on AI as its most scalable and adaptive line of defense. The systems being deployed aim not only to recognize today’s threats, but to anticipate and neutralize tomorrow’s.
For users, these updates may be largely invisible—but the impact could be significant. By filtering out fraudulent content earlier in the process, reducing exposure to misleading information, and flagging suspicious activity as it happens, Google is adding layers of friction to scam operations, making it more difficult for them to succeed.
The company says it will continue to refine its AI models and broaden the scope of protection, extending to more device types and threat categories over time.