To fight against cybercrime, Japan’s National Police Agency (NPA) has released a free decryption tool for victims of the Phobos and 8Base ransomware variants. The decryptor, made publicly available in collaboration with international law enforcement agencies, aims to assist thousands of organizations worldwide that have suffered from ransomware attacks since 2019.
The Japanese police revealed decryption utility along with an English-language user guide, offering relief to affected organizations across multiple sectors.
The initiative follows extensive international cooperation involving the European Cybercrime Centre (Europol), the FBI, and law enforcement agencies in the U.S., Germany, South Korea, France, and Thailand.
The FBI’s Baltimore field office led the investigation, which earlier this year resulted in the takedown of key elements of the Phobos ransomware infrastructure and criminal charges against several alleged affiliates.

Background on Phobos and 8Base Ransomware
Phobos ransomware first emerged in 2019 and is known for targeting small to mid-sized organizations, demanding relatively modest ransom payments, many under $100,000. According to U.S. prosecutors, Phobos operators and affiliates have collectively extorted more than $16 million from over 1,000 victims globally.
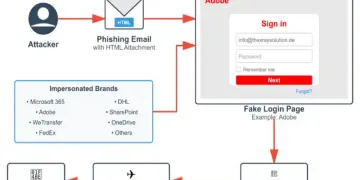
The 8Base ransomware group, which emerged as a spinoff in mid-2023, leveraged Phobos’s infrastructure to develop its own variant. Europol previously stated that 8Base tailored attacks for maximum impact using Phobos’s encryption and delivery mechanisms. The group has been particularly aggressive with its double extortion tactics, encrypting victims’ data and threatening to publish the stolen files unless a ransom was paid.
Notable targets of 8Base include:
Critical Infrastructure Among the Victims
U.S. authorities warned earlier this year that Phobos and its variants had affected state, local, tribal, and territorial government entities. The targets included public healthcare services, emergency services, education systems, and law enforcement. The damages amounted to millions of dollars in ransom payments and disrupted operations.
Victim examples from court documents include:
- California public school system – Paid $300,000 (Summer 2023)
- Maryland accounting firm for federal agencies – Paid $12,000 (Early 2021)
- Pennsylvania healthcare organization – Paid $20,000 (Spring 2022)
- Maryland healthcare groups – Paid $25,000 and $37,000 (Summer 2022)
- North Carolina children’s hospital – Paid $100,000 (Fall 2023)
- Other victims include contractors for the U.S. Department of Defense and Energy, public school systems in Connecticut, a New York law enforcement union, and a federally recognized tribe.
Law Enforcement Hits Back
The global investigation culminated in several high-profile arrests:
- Evgenii Ptitsyn, an alleged administrator of Phobos, was extradited from South Korea in November.
- Another suspect was arrested in Italy after an international arrest warrant was issued by French authorities.
- A Thai police operation dubbed “PHOBOS AETOR” led to the arrest of four individuals—two men and two women—in Phuket.
The U.S. Department of Justice later break open charges against Roman Berezhnoy (33) and Egor Nikolaevich Glebov (39), who are accused of using the Phobos ransomware to generate over $16 million in illicit revenue. According to the indictment, the duo profited by distributing Phobos code to affiliates on the dark web. When victims paid for decryption, affiliates shared a portion—often $300—with the administrators. Prosecutors confirmed that Ptitsyn controlled the main cryptocurrency wallet used to collect these fees.
In tandem with the arrests, law enforcement agencies dismantled over 100 servers used in the ransomware operations and issued alerts to more than 400 companies that were either under threat or already compromised.
How to Use the Free Decryption Tool
The decryption tool, named “PhDec Decryptor,” is available for free download via the No More Ransom portal (https://www.nomoreransom.org). The software can decrypt a wide range of files encrypted by Phobos or 8Base ransomware variants.
Supported File Extensions:
- .phobos
- .8base
- .elbie
- .faust
- .LIZARD
- Additional extensions matching the naming convention {Original Filename}.id[{8 random characters}–{4 digit numbers}].[{Mail address}].{File Extensions}
Note: Decryption may not be successful if the files were corrupted during the encryption process or if encryption keys were broken.
Step-by-Step Guide to Use Decryption Tool
- Download & Run the Tool:
- Download from No More Ransom and execute the .exe file.
- Users may need to override antivirus warnings.
- Agree to Terms of Service:
- Review and accept terms before proceeding.
- Select Files or Folder:
- Choose a single file or entire folders for decryption.
- Drag-and-drop functionality is supported.
- Set Output Directory:
- Specify where decrypted files should be saved.
- Start Decryption:
- Press [Decrypt] to initiate the process.
- Check Results:
- On completion, a message confirms success.
- Results include the number of successfully decrypted, failed, and unsupported files.
Output reports are generated in .txt, .csv, and .log formats to provide detailed feedback on the decryption process.
Conclusion
As ransomware continues to evolve, coordinated law enforcement action and accessible resources like this tool offer a lifeline to organizations hit by such debilitating attacks. Victims are encouraged to avoid paying ransoms, use the free decryptor, and report incidents to local and international cybersecurity authorities.
Caution for Victims: While the decryptor offers hope, the Japanese NPA cautions that it does not guarantee the integrity of all decrypted files, especially if the original encryption was flawed or if the files were altered post-attack.