A critical Flowise RCE vulnerability is now being actively exploited. The flaw, tracked as CVE-2025-59528, carries a maximum severity rating and enables attackers to execute arbitrary code on affected systems, potentially leading to full system compromise.
Security researchers have confirmed that threat actors are taking advantage of the Flowise RCE vulnerability to infiltrate vulnerable deployments. This issue, identified as CVE-2025-59528, allows malicious actors to inject and execute arbitrary code through unsafe handling of user input within the platform.
The vulnerability was first publicly disclosed in September of last year, accompanied by warnings that successful exploitation could result in command execution and unauthorized access to the file system. Despite the availability of a patch, exploitation attempts have now been observed in real-world environments.
Unsafe JavaScript Execution
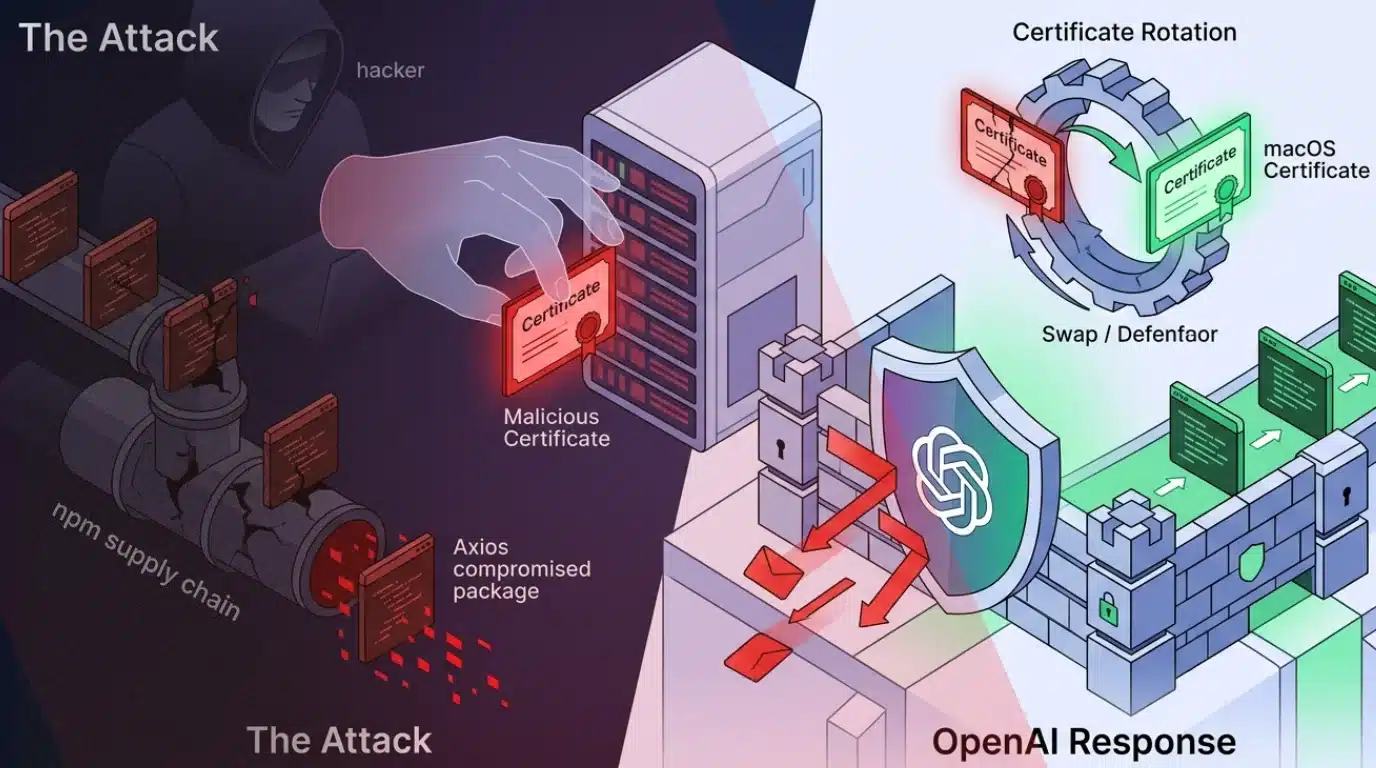
The issue arises in the Flowise CustomMCP node, a component designed to connect with external Model Context Protocol (MCP) servers. The vulnerability arises because the node unsafely evaluates user-supplied input in the mcpServerConfig setting.
This design flaw allows attackers to inject malicious JavaScript code without undergoing proper validation or security checks. As a result, attackers can leverage the Flowise RCE vulnerability (CVE-2025-59528) to execute arbitrary code, potentially gaining control over the affected system.
The developers addressed the vulnerability in Flowise version 3.0.6. The latest available version, 3.1.1, was released two weeks ago and includes the necessary fixes.
Flowise itself is a low-code, open-source platform used to build AI agents and large language model (LLM) workflows. It features a drag-and-drop interface that enables users to design pipelines for chatbots, automation tools, and other AI-driven systems.
Evidence of Flowise RCE Vulnerability
According to Caitlin Condon, VP of Security Research at VulnCheck, exploitation activity has already begun. She stated:
“New hashtag#KEV: Early this morning, VulnCheck’s Canary network began detecting first-time exploitation of CVE-2025-59528, a CVSS-10 arbitrary JavaScript code injection vulnerability in Flowise, an open-source AI development platform. The vulnerability resides in the CustomMCP server logic in multiple versions of Flowise and allows for code execution.”
She further noted:
“Observed activity so far originates from a single Starlink IP. Our team’s ASM queries show 12,000 – 15,000 instances of Flowise on the public internet as of today. CVE-2025-59528 is patched in version 3.0.6 of Flowise.”
This suggests that while exploitation is currently limited, the attack surface remains significant due to the large number of exposed instances.
Additional Vulnerabilities Increase Risk
The Flowise RCE vulnerability (CVE-2025-59528) is not the only security concern affecting the platform. Researchers have also observed active exploitation of two other vulnerabilities: CVE-2025-8943 and CVE-2025-26319.
Condon emphasized that both of these flaws are included in VulnCheck’s Known Exploited Vulnerabilities (KEV) catalog and have been detected through their monitoring systems. This indicates a broader pattern of attackers targeting Flowise deployments to execute arbitrary code and gain unauthorized access.
Although estimates suggest that between 12,000 and 15,000 Flowise instances are accessible on the public internet, it remains unclear how many of these are vulnerable to CVE-2025-59528.
Even so, the presence of such a large number of exposed systems increases the likelihood of further attacks, especially as exploit techniques become more widely available.
Recommendations for Users
Users of Flowise are strongly advised to take immediate action to mitigate the risks associated with CVE-2025-59528. Upgrading to version 3.1.1, or at a minimum version 3.0.6, is critical to patch the Flowise RCE vulnerability and prevent attackers from exploiting it to execute arbitrary code.
Additionally, organizations should evaluate whether their Flowise instances need to be publicly accessible. If external access is not required, removing these systems from the public internet can significantly reduce exposure to attacks.