By Ashish Tandon, Founder & CEO, Indusface
In the ever-evolving landscape of digital threats and cyberattacks, the year 2024 demands a renewed commitment to cybersecurity. As technology advances, so do the tactics employed by malicious actors seeking to exploit vulnerabilities in our digital infrastructure.
According to Indusface’s Q3 Report, over 1.6 billion cyberattacks were blocked from India, indicating a 70% increase compared to Q2, 2023. It is imperative that individuals, businesses, and organizations proactively fortify their digital defences to thwart these evolving threats.
Cybersecurity Resolutions: Tips Strengthening Digital Defences
Maintain an Inventory of Public-Facing Assets and APIs
The first step in securing digital fortifications is understanding what assets are exposed to the public. Over 70% of successful cyberattacks target web applications and APIs, making a comprehensive asset inventory crucial. Regularly updating and reviewing this inventory helps organizations stay ahead of potential threats and streamline their cybersecurity efforts in an ever-changing digital landscape.
Regular Vulnerability Scans and Penetration Testing
Identifying vulnerabilities in a timely manner is essential for proactive cybersecurity. To enhance security, implementing practices akin to penetration testing is crucial. This involves systematically assessing and fortifying against misconfigurations, access vulnerabilities, session management weaknesses, input validation flaws, error handling issues, and encryption loopholes.
Scanning alone may not be sufficient; organizations should complement it with annual penetration testing for a comprehensive security approach.
Deploy a WAAP in Block Mode
With the rising sophistication of cyberattacks, deploying a Web Application and API Protection (WAAP) system is no longer an option but a necessity.
Configuring WAAP in block mode allows organizations to proactively prevent malicious traffic from reaching the application and acts as a robust barrier against a variety of cyber threats, including SQL injection, cross-site scripting, and DDoS attacks.
By preventing malicious activities at the edge, organizations can significantly reduce the risk of successful cyber-attacks and minimize potential damage.
Enable Origin Server Protection
Blocking malicious traffic at the edge is crucial, never expose your origin servers to the internet. Make sure that you deploy an edge security solution like a WAAP. Also, once the WAAP is deployed, make sure to whitelist only a set of trusted IPs on the origin server. This will make sure that only trusted IPs/users access your origin server directly.
Regularly Apply Zero-Day Patches and Autonomous Patches on WAAP
Zero-day attacks pose a significant challenge, targeting organizations of all sizes. Staying vigilant and applying zero-day patches promptly is crucial. However, acknowledging that immediate patching may not always be feasible, the adoption of autonomous patching on the WAAP for application and business logic vulnerabilities becomes crucial.
Protection on WAAP, also called virtual patching, acts as a temporary fix, mitigating the risk of exploitation while organizations work on a permanent solution.
Adopt AI
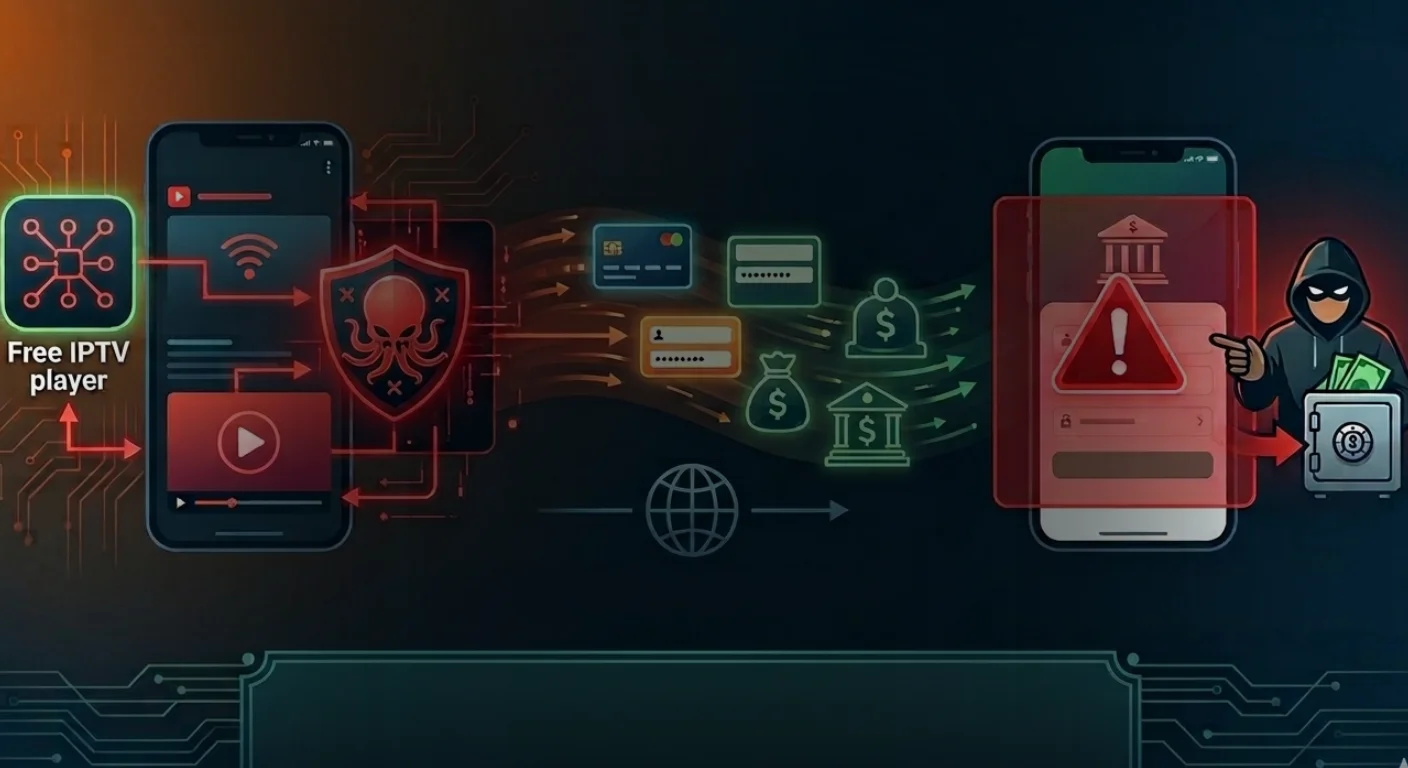
2023 might very well be the inflection point in terms of bot attacks given how easy it is to deploy bots with widespread adoption of LLMs. On our WAAP, we saw a high double-digit growth of bot attacks each quarter. Card cracking, credential stuffing and bot-led slow-DDoS attacks were the most frequently used attack vectors.
Countering these attacks requires the use of AI models that can quickly alert the SOC / managed services teams to take quick mitigation measures.
In conclusion
The responsibility lies with individuals, businesses, and organizations to bolster their digital defenses against an ever-evolving array of cyber threats. Through the maintenance of comprehensive, updated inventories, regular vulnerability assessments, deployment of AI-based protection measures, and a proactive approach to patching, we can collaboratively construct a resilient digital ecosystem, safeguarding our valuable assets amidst the dynamic landscape of cyber threats.
Recognizing the importance of foresight in cybersecurity, let us commit to strengthening digital defences in 2024 and paving the way for a more secure and interconnected future.
Disclaimer: The views and opinions expressed in this guest post are solely those of the author(s) and do not necessarily reflect the official policy or position of The Cyber Express. Any content provided by the author is of their opinion and is not intended to malign any religion, ethnic group, club, organization, company, individual, or anyone or anything.