As the world steps closer to 2024, the cybersecurity industry is poised to witness some transformative changes. The cybersecurity predictions for 2024 suggest that with the increasing numbers of cybercrime syndicates across the globe constantly working to disrupt business operations, organizations need to buckle up and build digital fortresses to protect against otherwise obvious disasters.
A research report indicates that the cybersecurity industry will grow from US$190 billion in 2023 to US$208.8 in 2024, indicating a 10% year-on-year growth. With the increased rates of cybercrime, the need for strong cybersecurity is constantly increasing, giving rise to the demand for trustable cybersecurity solutions.
Experts have predicted a continued rise in the exploitation of zero-day vulnerabilities, ransomware, state-sponsored attacks, as well as a lack of adequately trained cybersecurity resources in 2024.
Cybersecurity Predictions for 2024
The cybersecurity anticipations for 2024 from the industry experts across numerous security teams who work on the frontlines of cyberattacks suggest that the proliferation of AI is going to be a boon for both cybersecurity professionals and cybercrime syndicates.
Increased Artificial Intelligence Usage
AI is going to be the major factor driving changes in the cybersecurity industry for the upcoming year where a lot of trends are going to redefine the way we have been navigating the cyber universe till now.
A recent report suggests an expanding global AI market in the upcoming two years. It is expected to reach US$190.61 billion by 2025, which is a compound annual growth rate (CAGR) of 36.62%.
Pooja Shimpi, founder and CEO of Sybernow believes that the usage of artificial intelligence will continue to increase in the coming year which might give rise to the already increased number of ransomware attacks. She further explains that the use of AI has increased and will continue to do so in the coming year too along with the associated risks.
The increased use of AI will serve as a supporting factor for individuals on both sides giving rise to a challenging competition between the cybersecurity defenders and the cybercriminal gangs. Increased sophistication of AI tools is expected to enhance the precision of both offense and defense.
David Aviv, CTO at Radware said, “An AI arms race will transform both offense and defense in the cyber domain. In just over a year, AI attack tools have advanced from simple amplification to sophisticated open-source code that enables bad actors to customize assaults that exploit vulnerabilities with precision.”
2024 Will be the Cloud Era
The data presented by IDC’s Worldwide Semiannual Public Cloud Services Tracker suggests that the revenue generated from cloud services will reach US$663 billion by the end of 2023, an increase of 20% over 2022. A similar increase is expected in 2024.
Business Wire quoted IDC stating that the total amount spent globally in 2024 on cloud services, the professional and managed services opportunities that surround them, and the gear and software that support cloud services will exceed US$1.0 trillion.
Experts predict that this trend will also give rise to an increased need for strong zero-trust architecture and cloud security across various sectors as the human threat actors combined with AI might amplify the threats.
Milin Shah, a cybersecurity professional and AVP at SitusAMC stated, “The year 2024 will witness a shift to cloud services. Considering the upcoming changes, I anticipate major cybersecurity developments for the next two years in the field of cloud security”.
Growing Frequency of Mobile Cybercrime
Google’s Cybersecurity Forecast 2024 also predicts that in 2024, scammers and cybercriminals will still be using social engineering techniques, like spoofing pop-up alerts, phony social media accounts, banks, or government officials, to trick victims into downloading malicious apps to their smartphones.
Experts are anticipating that mobile devices will be a target for cybercriminals in 2024, with an increase in mobile-specific threats. These threats will include mobile malware, banking trojans, and phishing attacks.
Mobile devices have taken an integral place in our lives. and this makes them an attractive target for cyber adversaries. Exposure to mobile phone data can lead to serious threats of identity theft, unauthorized access to sensitive personal data, and financial fraud.
State Sponsored Attacks
This year has witnessed several states-sponsored cyberattacks on both the citizens of the same country, as well as on the citizens and organizations of enemy nations. Towards the end of 2023, celebrities and politicians of countries got notifications on their mobile phones for possible “state-sponsored hacking” attempts to extract data for government agencies, India too witnessed a similar incident.
Also, government-sponsored hacktivists and attackers have been on the rise in 2023, which is expected to continue in the upcoming year 2023 as the world continues to grapple with multiple fault lines of geopolitical stress like the Russia-Ukraine, and Israel-Palestine.
Milin Shah, while citing the Russia-Ukraine war and the use of state-sponsored attacks, stated that 2024 will witness, a “Rise in State-sponsored cyberattacks, economic and cyber espionage targeting critical infrastructure, rise of a political war due to increased deepfakes and their use for political influence.
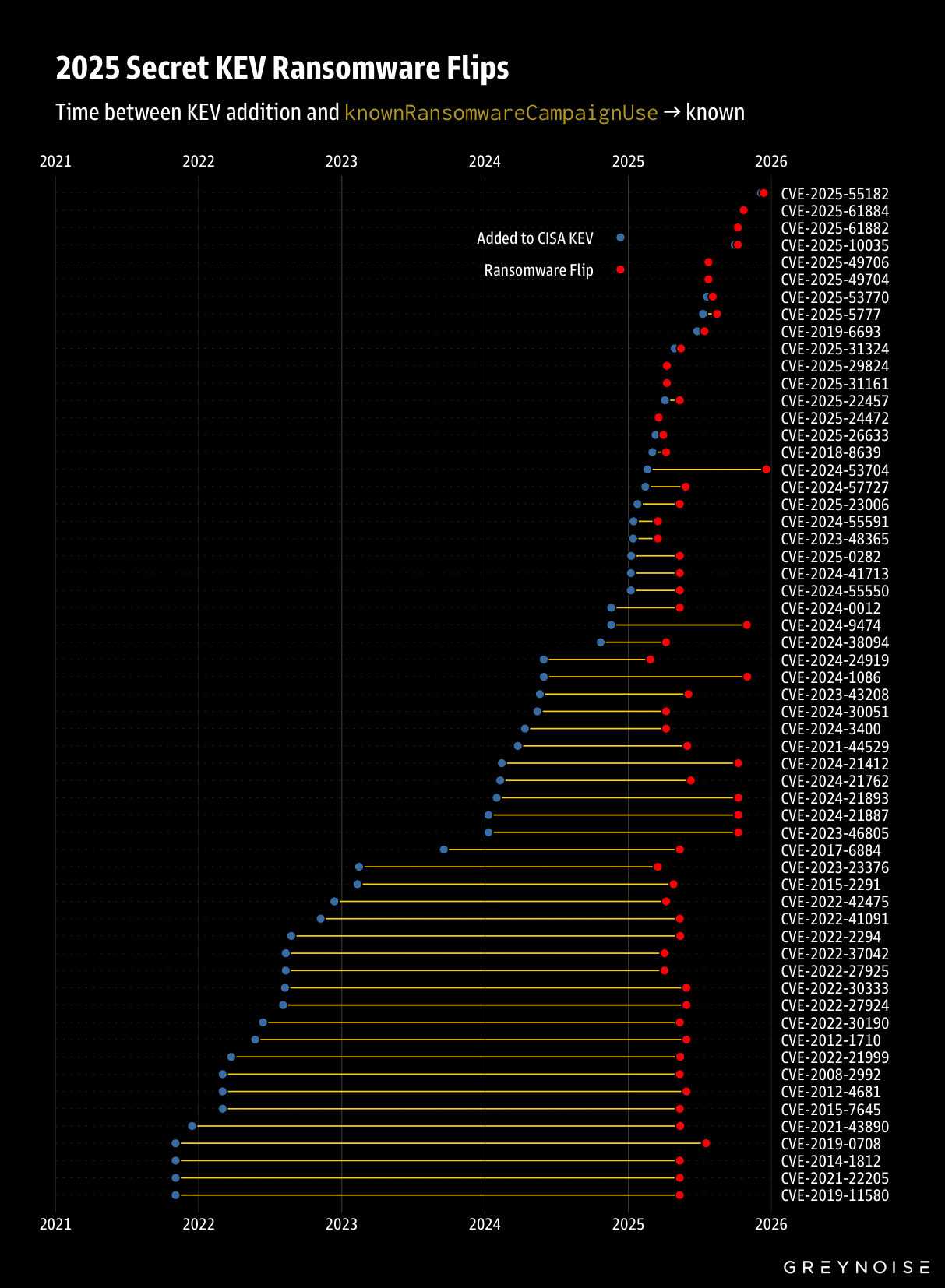
Rise in Ransomware Attacks
Experts like Pooja Shimpi anticipate that with the continued rise in ransomware attacks, cybercriminal groups might also evolve in their attacking methods and will operate at a larger scale to churn bigger profits.
This also will expose organizations to a higher risk if they do not adopt a better cybersecurity strategy. Hackers are also getting very advanced; organizations need to be well-equipped and train their employees to guard against them.
Sabarinathan Sampath, Chief Strategy Officer at Wire 19, said that ransomware attacks are increasing. Organizations must be prepared to guard against them. He believes that employees are the weakest link in the cybersecurity chain and that adequate training helps them understand where the weakness lies, and how to react in such scenarios.
He also highlighted the need for an inter-government collaboration for sharing cybersecurity intel related to ransomware. Sampath believes that governments need to help organizations train to react to such situations and elements.
Rise in AI-Powered Frauds
Experts also predict that the world needs to buckle up for AI-powered frauds in 2024. This time, cybercriminals will more cunningly orchestrate deceit with morphed photos, doctored videos, and fake voices.
Knowing the trade won’t be enough to peacefully do business, organizations will need to have an understanding of the tricks deployed by cybercriminals too, and keep themselves aware and updated against cybercrime.
Padmakumar Nair, CEO and co-founder of Ennoventure Inc. stated, “As we approach 2024, the escalating threat of counterfeiting necessitates a proactive approach harnessing cutting-edge technology-driven anti-counterfeit solutions.”
Adv Puneet Bhasin, an expert in cyber law and data protection anticipates that there will be increased AI-powered frauds in 2024. Such frauds could happen in multiple ways like fake voices, doctored videos, and morphed photos.
AI will assist in making very realistic audio-visual content for malicious actors. She predicts that this will continue to happen in 2024, until and unless people are adequately educated about it and don’t fall prey to vicious threat actors.
She also predicted that the trend of Indian organizations, primarily financial institutions being targeted in cybercrime will also continue.
Increased Need for Employee Training
Skill crunch in the cybersecurity industry has been a continuous issue since the emergence of the cybersecurity industry. Forbes quoted a report by Enterprise Strategy Group stating that 54% of cybersecurity professionals feel that their firm has been negatively impacted by cybersecurity skills shortage in the past two years.
Vaibhav Patkar, an independent cybersecurity consultant stated, “Skill mismatch is always there. The only way out is constant training. And the way things are evolving, unless and until you upgrade yourself with training. Training should be done according to hierarchy levels and the responsibilities he is having in an organization.”
Cybersecurity stalwarts believe that upskilling employees is going to strengthen businesses against negative instances. A proactive approach to enhancing cybersecurity like vigilant defense against cyberattacks will build a more cyber-secure future.
Binod Singh, CEO and Chairman of Cross Identity said, “Upskilling programs emerged as a cornerstone, empowering organizations to transition from a defensive to a proactive cybersecurity stance. Fundamental cybersecurity practices – from robust passwords to vigilant defense against phishing – have laid the foundation for a more secure digital future.”
Experts predict that although several organizations are already implementing incident response training programs, 2024 will witness an increased need for adequate employee training to respond to cybersecurity emergencies that could emerge in the coming year.
Milin Shah states, “Incident response and planning is implemented by almost every MNC’s or Large-scale Startup’s, but how many of them have a real-world simulation exercise to ensure the incident response plan is effective?”
He continued by saying that even though the “Escalation Matrix” or the stepwise guide for complex cybersecurity incidents exists, are severe incidents handled well? He stated, “I would say less than 2 in 10.
That is the case with Employee Awareness too. While every company performs Security Awareness training, real-world simulated Phishing excessive with actual pressure is different from responding in well-aware and practice grounds.”
Continued Exploitation of Zero-Day Vulnerabilities
Since 2012, there has been an overall rise in the exploitation of zero-day vulnerabilities, and 2023 is expected to surpass the previous record set in 2021, according to Google’s Cybersecurity Forecast 2024.
Google anticipates that nation-state attackers and cybercriminal organizations will continue to use zero-day vulnerabilities in 2024. This can be attributed, in part, to the attackers’ desire to have persistent access to the system for as long as possible. By taking advantage of zero-day vulnerabilities, they can do so far longer than they could if they were to send a phishing email and then install malware.
Since security teams and solutions are now much better at spotting malware and phishing emails, attackers will look for additional ways to avoid detection. Threat actors are particularly drawn to edge devices and virtualization software because of their difficulty in monitoring.
Based on previous extortion incidents, cybercriminals are aware that utilizing a zero-day vulnerability would increase the number of victims and the number of enterprises willing to pay exorbitant ransomware or extortion demands.
Combined Power of AI and Human Threat Actors
In the times where everyone can access AI tools, it has become easier for cybercriminals to create mirages leading to phishing attacks and frauds. Malicious threat actors have added artificial intelligence to their arsenal to outsmart commoners, which is scary on the part of innocent, unsuspecting people.
Vaibhav Patkar, an independent cybersecurity consultant said that spotting phishing sites was easier in the older times as they had common doubt elements like spelling and grammatical errors. But nowadays with the help of AI and ML, these threat actors are improving their tactics, which is frightening for the common man.
He further explained that there are AI-powered tools available for almost everything. Anyone can go and make whatever changes they want to make to someone’s face and exploit it for blackmailing and extortion. But on the other hand, he believes that the same tools can also be used for a good cause. He thinks forums can be created where experts can come together and change the game.
As the world is advancing towards 2024, a new storyline emerges. The battle for survival in the cybersecurity sector will intensify and artificial intelligence will become the major driver of change for most cybersecurity trends in 2024.
Some experts predict that with AI tools being available for anything and everything, there will be an increase in cybercrimes; but at the same time, some of them also believe that the very power behind these crimes which is artificial intelligence, could also change things to the better side next year.
In addition, the combination of human factors and artificial intelligence will bring a new batch of cybersecurity problems and solutions. Ramped-up vigilance throughout the year will be followed by a concerted effort to train employees to guard against hackers.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.