In today’s world, it’s hard to miss the constant buzz about cyber threats, especially when they hit critical infrastructure and sectors like energy, healthcare, and transportation. These attacks are not just increasing in number; they’re becoming more sophisticated, making it crystal clear that we need to step up our defenses.
Take recent events, for example. In February, the Cybersecurity and Infrastructure Security Agency (CISA), National Security Agency (NSA), and FBI teamed up with their partners to issue a serious warning. They alerted key infrastructure sectors about potential cyber threats, drawing attention to vulnerabilities that had already been exploited by cyber operations linked to the People’s Republic of China (PRC).
And it’s not just happening in the U.S. a cyberattack on a nuclear facility in the UK recently showed us how high the stakes can be when it comes to protecting our infrastructure. Yet, despite all the alarms and awareness, there’s still a huge gap in both legislation and international cooperation on cybersecurity.
The Dying Need for a Better Global Cyber Treaty
The current state of cybersecurity for critical infrastructure is fragmented, with a patchwork of regulations and standards that often fail to address the complexities of modern threats. Although the United Nations adopted voluntary norms in 2015, their impact has been limited.
Cyber incidents targeting infrastructure have reportedly doubled between 2020 and 2022, according to the International Energy Agency, highlighting the inadequacy of the current response framework.
To address this pressing issue, the international community should consider establishing a global cyber treaty specifically focused on enhancing the protection of critical infrastructure. Such a treaty could build on existing frameworks, introducing binding measures that would elevate global cybersecurity standards.
Currently, the cybersecurity regulatory environment comprises a mix of federal laws, industry standards, and sector-specific guidelines. However, none of these regulations provide comprehensive coverage for all critical infrastructure sectors.
- Health Insurance Portability and Accountability Act (HIPAA): This federal law is crucial for safeguarding medical information, requiring healthcare providers and their associates to implement security measures to protect patient data. Despite its importance, HIPAA’s scope is limited to the healthcare sector and does not extend to other critical infrastructure areas.
- Cybersecurity Maturity Model Certification (CMMC): Designed for defense contractors working with the Department of Defense (DoD), the CMMC ensures these entities adhere to specific cybersecurity standards. However, its applicability is restricted to defense-related contractors, leaving other sectors without comparable protections.
- Payment Card Industry Data Security Standard (PCI DSS): This industry standard, adopted widely across states, sets security requirements for entities handling credit card data. Yet, PCI DSS does not encompass critical infrastructure sectors beyond financial transactions.
- Communications Assistance for Law Enforcement Act (CALEA): Enforced by the Federal Communications Commission (FCC), CALEA mandates telecommunications companies to facilitate lawful interception of communications. However, CALEA’s focus on law enforcement does not address broader cybersecurity concerns.
- North American Electric Reliability Corporation Critical Infrastructure Protection (NERC CIP): NERC CIP guidelines are instrumental in securing the electric grid from cyber threats. Nonetheless, they are sector-specific and do not extend to other critical infrastructure areas such as transportation or manufacturing.
- Despite these existing frameworks, there is no central, comprehensive approach to cybersecurity across all critical infrastructure sectors. This fragmented regulatory environment often results in gaps that cyber adversaries can exploit.
The Case for a Unified Cybersecurity Framework
The need for a more integrated regulatory approach is not only important but has become the need of the hour. Centralized regulations could establish a baseline for security practices, encouraging organizations to develop and refine their cybersecurity strategies.
This would address common vulnerabilities and foster innovation in security measures. For instance, the Zero Trust model, which manages interactions between people, data, and systems to mitigate security risks, has emerged in response to the need for better security in increasingly parameterless networks.
Centralized regulations could also standardize security practices across supply chains, reducing vulnerabilities that arise from interconnected business operations. By ensuring that all parties adhere to the same security protocols, organizations can better manage and mitigate risks. This approach would not only enhance security but also build trust among stakeholders, including consumers and supply chain partners.
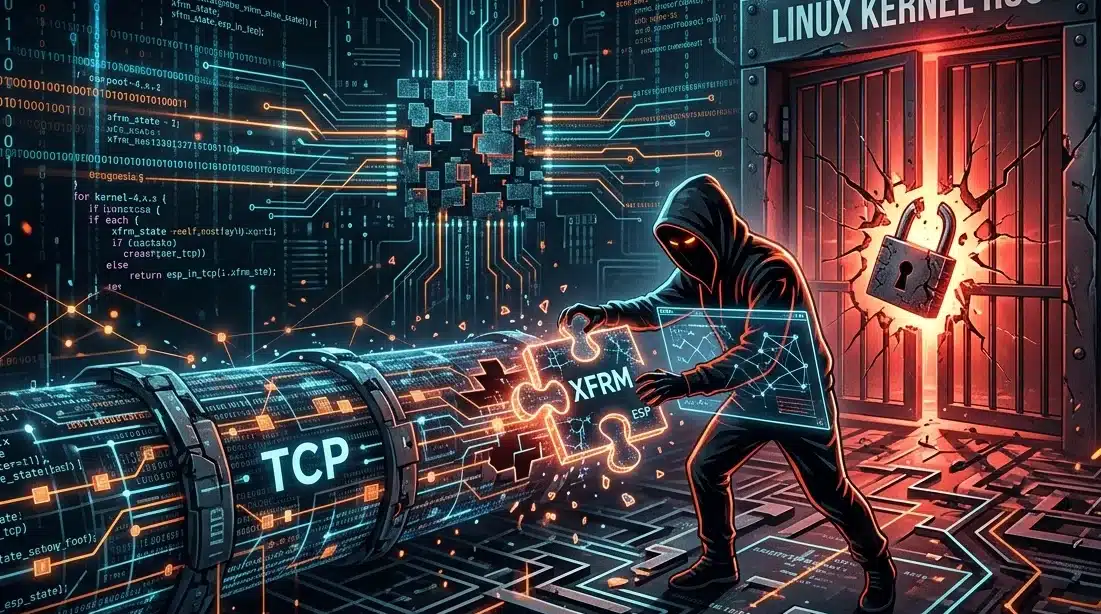
The current threat system highlights the need for better regulatory frameworks. Online threats such as Advanced Persistent Threats (APTs) and the convergence of IT and Operational Technology (OT) systems pose significant challenges.
Convergence of IT and OT Systems: The integration of IT and OT systems has expanded the attack surface for critical infrastructure. Systems like industrial control systems (ICS) and supervisory control and data acquisition (SCADA) are now vulnerable to cyber threats that were previously limited to IT networks. This convergence highlights the need for integrated cybersecurity frameworks that address both IT and OT environments.
Advanced Persistent Threats (APTs): APTs are sophisticated, often state-sponsored attacks aimed at high-value targets over extended periods. Addressing APTs requires advanced detection and response capabilities, as well as continuous monitoring and threat intelligence. Regulations that mandate these capabilities could help organizations better defend against such sophisticated attacks.
Internet of Things (IoT) and Legacy Systems: The proliferation of IoT devices introduces additional security challenges, as many are designed with minimal security controls. Moreover, critical infrastructure often relies on legacy systems that were not designed with modern cybersecurity threats in mind. Updated regulatory standards are needed to address these vulnerabilities.
Global Perspectives and Recommendations
Given the global nature of cyber threats, international cooperation is essential for protecting critical infrastructure. A global cybersecurity treaty focused on critical infrastructure could help establish universal standards and norms. Such a treaty would provide a framework for responding to cross-border cyber threats and build on existing frameworks, like the UN’s guidelines on responsible state behavior in cyberspace.
Enhancing public-private partnerships is also crucial. Collaboration between government agencies, industry stakeholders, and cybersecurity experts can lead to more effective security measures and facilitate the sharing of threat intelligence. Initiatives such as the Cybersecurity and Infrastructure Security Agency (CISA) and Information Sharing and Analysis Centers (ISACs) play a vital role in fostering this collaboration.
Moreover, promoting innovation in cybersecurity is essential for staying ahead of emerging threats. Investing in research and development for new security technologies and fostering collaboration between researchers, developers, and industry practitioners can drive the development of advanced security solutions.
To Sum Up
As we navigate the complexities of our digital world, upgrading cybersecurity standards for critical infrastructure is more urgent than ever. The recent spike in cyberattacks on energy grids, healthcare systems, and transportation networks exposes a troubling stagnation and insufficiency in our current defenses.
While frameworks like HIPAA, CMMC, and PCI DSS exist, they fall short of covering all critical sectors comprehensively. The fragmented nature of today’s cybersecurity landscape leaves dangerous gaps, especially as technology advances and threats become more sophisticated.
To truly tackle these challenges, the international community needs to push for a unified global cyber treaty. Such a treaty could bring a cohesive approach to protecting critical infrastructure, establishing universal standards, and enhancing global cooperation. By aligning our efforts, standardizing practices, and encouraging innovation, we can build a stronger, more resilient cybersecurity strategy capable of standing up to the evolving threats of the digital age.