As billions of fans gather in India to witness the much-awaited 13th edition of the ICC Men’s Cricket World Cup on October 5, 2023, cybersecurity experts face a significant challenge.
Following the successful G20 summit in the first week of September this year, despite being targeted by hacktivist groups, it’s now crucial to safeguard the integrity of the ICC World Cup.
With fans from all over the world converging in India to cheer for their favorite teams, the cybersecurity community has a herculean task ahead.
Throughout the 48 matches at nearly 10 venues, fans will flock to the Narendra Modi Stadium in Ahmedabad, India for the opening game. Scammers will attempt to exploit these enthusiastic spectators with enticing offers aimed at financial gain.
In the cybersecurity landscape of 2023, data breaches, often stemming from deceptive spear-phishing emails, constitute nearly 90% of cyber attacks. Opportunistic scammers are quick to leverage crises, using them as opportunities to establish fraudulent websites and prey on unsuspecting individuals.
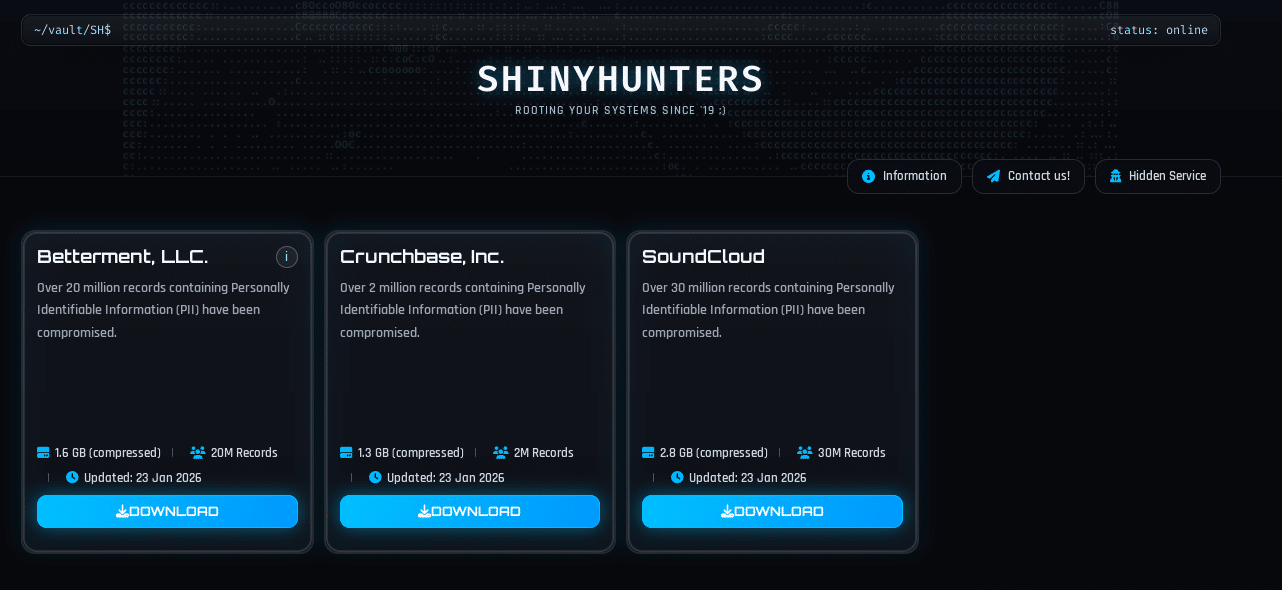
Even global sporting events have been hit by cyber attacks, with headlines frequently reporting data breaches exposing customer data online. For instance, CricketSocial, an online platform that provides cricket analytics and tournament data to fans, players, and authorities, was involved in one such event.
An unintentional data leak revealed a database with approximately 100,000 client entries, including admin login info, emails, and hashed passwords. “Alongside the admin’s passwords and user PII the open instance also holds all of the content stored on the website,” stated a Cybernews report.
The consequences of such breaches are far-reaching. Cybercriminals, armed with tools to exploit cricket data, pose a significant threat. The grandeur of events like the ICC World Cup, T20 World Cup, and IPL not only attracts passionate spectators worldwide but also invites cybercriminals.
In this digital age, where billions of fans unite to embrace the spirit of cricket, it’s crucial to bolster cybersecurity measures and prioritize data privacy to safeguard both the sport and its devoted enthusiasts. In this article, we’ll explore cricket cybersecurity, emphasizing the need for a proactive and collaborative effort to preserve the sport’s integrity and the security of its passionate followers.
Data Privacy Concern in Cricket
Cricket has evolved into a vast industry propelled by data and technology in the digital age, becoming more than just a sport. While the digital revolution has brought fans closer to the game than ever before, it has also created serious worries about data protection.
Cricket organizations, like several other entities, collect and use personal information from spectators and players for a variety of objectives. However, mismanagement or leakage of this data can have serious implications not only for the players but also for the sport.
Collection of personal data and usage: Cricket organizations collect personal data from fans and players through ticket purchases, online merchandise orders, and social media interaction. This information includes names, addresses, contact information, and, in certain situations, financial information.
The data is frequently used for marketing, targeted advertising, and improving fan experiences. For example, cricket websites may use cookies to track user activity and preferences to provide customized content.
Risk of data breach: Data breaches in cricket can have far-reaching consequences. In 2023, a data breach exposed the passport details of cricket icons and current stars such as Wasim Akram, Chris Gayle, Ian Bell, and Mohammad Babar Azam.
Over 500 cricketers, including players from India, New Zealand, and Afghanistan, were affected by the breach, which was discovered by UK-based researcher Etizaz Mohsin, who also identified phone numbers and email addresses of players and their agents in the data.
This case clearly shows that violations not only result in financial losses, but also degrade the reputations of the individuals involved and the sport itself. Fans may lose faith in the ability of cricket organizations to preserve their data.
Furthermore, the costs of data breaches go beyond people. Cricket organizations also keep sensitive strategic data, player contracts, and financial records, making them appealing targets for fraudsters. The disclosure of such information may jeopardize the sport’s competitive balance and financial stability.
Regulatory Measures and Guidelines for Data Protection
Cricket firms are prioritizing cybersecurity to reduce the risk of data breaches and comply with data protection rules. Individuals inside any organization, including cricket, are subject to privacy rules defined by the country’s data governing organizations.
The ICC cricket website notifies users about data gathering techniques, such as IP addresses, browser type, time zones, and items viewed. This data is used for internal operations and statistical purposes, and it is shared with ICC affiliates.
The ICC adheres to the International Standard for the Protection and Privacy of Personal Information (ISPPPI) to ensure data security, particularly in conducting anti-doping programs aligned with privacy rights.
The USA Cricket Privacy Policy collects user and player information for various purposes, including fraud prevention and research, utilizing Google Analytics for internal evaluation.
Personal data is retained only as long as necessary and then securely disposed of. The policy emphasizes that personal information of children under 13 is not collected without parental consent.
In New Zealand, cricket communities like Cricket Nation collect user information but exclude financial data. Sharing occurs with sporting initiatives and organizations as required by law. Users have the right to access their personal data.
Addressing the correction of personal data by users, the portal read, “You are entitled to obtain confirmation of whether or not we hold any personal information about you and to obtain access to that information.”
The Kent County Cricket Club in the United Kingdom complies with data protection legislation, including the EU General Data Protection Regulation and the Privacy and Electronic Communications Regulations (PECR). Information collected is accessible to authorized entities such as health service providers and government organizations.
The Greater Manchester Cricket League (GMCL), working with the Lancashire Cricket Foundation and the England and Wales Cricket Board, collects data related to club support, player registration, complaints, and participant demographics for diversity monitoring.
These measures help cricket organizations and communities ensure data protection and cybersecurity while complying with regulations.
Cricket’s Global Popularity Breeds Cybercriminal Activities

Cricket has the second-highest global audience of any sport, with the ICC Men’s Cricket World Cup, which is set to conclude in November 2023 and is set to bring together more than 1,000 nations and 4,200 players. This massive following, however, has made it a great target for cyber scammers attempting to take advantage of cricket fans’ excitement.
Cricket’s huge attraction, spanning genders and decades, makes it a rich playing field for con artists. The sport’s popularity is as broad as it is large, with millions of followers. For instance, the 100-ball Cricket event in 2021 drew a sizable 21% female viewership, demonstrating its broad popularity. While England’s cricket enthusiasm accounted for 65% of spectators in several matches, India alone has 1.1 billion cricket fans.
As the world excitedly awaits ongoing cricket matches and upcoming tournaments, cricket-lovers throughout the world are preparing to participate in a variety of sports-related activities, such as purchasing online tickets, visiting to stadiums, acquiring souvenirs, and photographing memorable moments.
Scammers, on the other hand, are well aware of these fan engagements and have begun creating fraudulent offerings such as counterfeit tickets, cloned websites, and alluring games with cricket-related incentives.
The ICC itself was the victim of a hoax, that led to a significant financial loss of around US$2.5 million. This shows scammers’ ever-changing techniques, which include social engineering attacks such as fake emails and attention-grabbing website pop-ups.
Common online cricket scams include a variety of alluring hotel discounts, restaurant coupons, and shopping incentives, all designed to deceive naïve participants.
Securing the Stumps: Cricket Cybersecurity Best Practices

To stay away of cyber traps and prevent falling prey to cybercrime, individuals should take note of the following safety guidelines:
- Cross-check with official websites: Make sure to visit official websites for all your cricket-related needs. Be wary of duplicated or cloned websites that lack complete material. Examine all webpages for legitimacy and the accompanying social media pages.
- Be cautious while sharing on social media: Use caution while sharing travel and personal information on social media platforms, especially with strangers who may be friends with you.
- Be mindful of freebies: Be wary of free ticket scams that promise incentives for clicking on dubious websites, spinning wheels, or updating gadgets due to purported virus concerns. These are frequently used as traps for cybercriminals.
- Read emails carefully: Keep an eye on your email inbox. Malware can damage your browser data and provide hackers information about your online habits. If you receive unexpected emails advertising discounted Cricket-related products or services, it is most certainly a fraud. To improve security, change passwords and enable multi-factor authentication.
Cricket fans can assure a safer online experience by taking simple steps, protecting both their personal information and the integrity of the sport.
Keeping in mind cricket’s global popularity, all users need to improve their defenses and keep cyber scammers at bay, allowing fans to enjoy their favorite game without falling subject to digital deception.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.