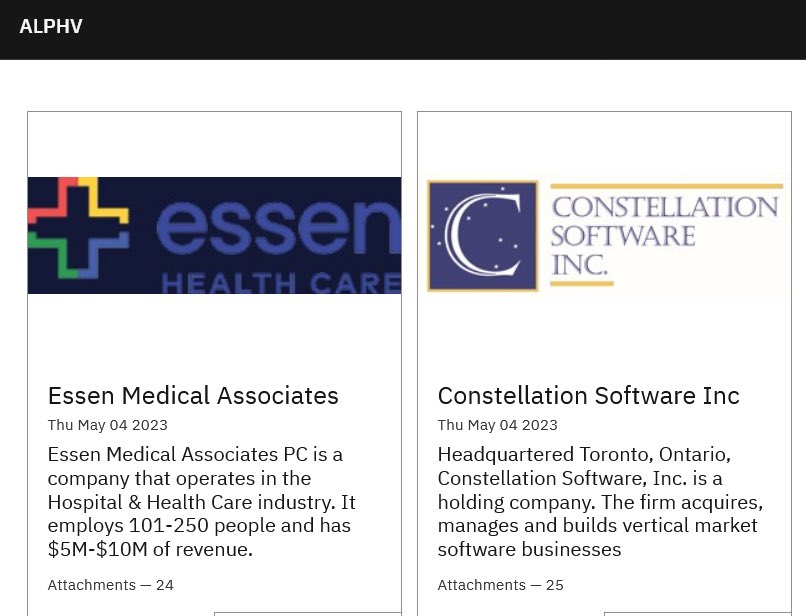
The ALPHV/BlackCat ransomware group has claimed responsibility for the Constellation Software cyber attack. The latest post on the ransomware gang’s leak site also listed US healthcare service Essen Medical Associates as a victim, along with the Canadian software company.
Essen Medical Associates and the Constellation Software cyber attacks were claimed on May 4, as shown in the screenshot shared below.
The leak site post by the ransomware group featured the number of attachments ALPHV/BlackCat accumulated from the two data breaches.
While 24 attachments were stolen files post the Essen Medical Associates cyberattack, 25 were breached after the Constellation Software cyber attack.
Constellation Software cyber attack: Company statement
A company press release disclosed right after the ALPHV/BlackCat leak site post has confirmed the Constellation Software cyber attack. According to the press release, the company was subjected to a cyber incident on April 3, impacting a limited number of its IT systems.
The systems were pertaining to a small number of internal financial reporting and data storage by the operating groups and businesses of the company.
The independent IT systems of Constellation’s operating groups and businesses were not impacted by this Incident in any way. The Incident has not had a material impact on the business operations of Constellation,” said the press release.
Following the forensic investigation carried out by the Canadian software company, it was confirmed that the impact of the Constellation Software cyber attack was fully curbed.
A limited amount of personal information of individuals was impacted by the Incident. A limited amount of data of the business partners of Constellation businesses was also impacted,” said the press release.
“Constellation’s operating groups and businesses are now in the process of contacting such individuals and business partners directly.”
However it refrained from terming the Constellation Software cyber attack as a ransomware attack.
Data impacted by the Constellation Software cyber attack
It was found that the personal information of individuals, and business partners were affected by the Constellation Software data breach.
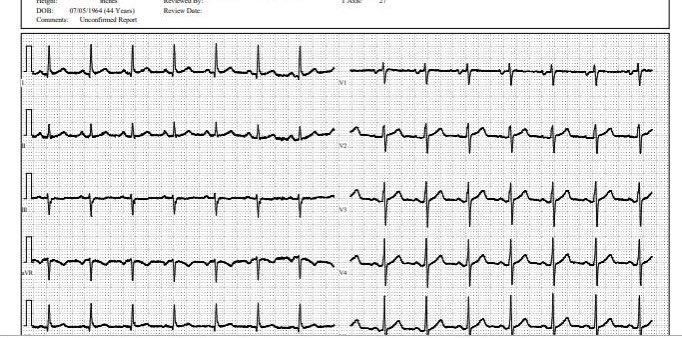
A patient’s cardiograph leaked as proof (Photo: Dominic Alvieri)Cybersecurity Analyst Dominic Alvieri shared the above screenshot that was made public by the ALPHV ransomware group as proof of the alleged Essen Healthcare data breach.
Besides the Constellation Software data breach and the cyberattack on Essen Healthcare, the group named 20 elementary and high school individuals’ names connected to Constellation Software.
The hackers were able to gain access to 20 of the elementary and high school who were clients of Constellation Software. The website of Essen Medical Associates was functioning well at the time of writing.
This incident again highlights how third-party cyber attacks that gravely impact linked organizations.
As hackers are able to access multiple users’ data by attacking a service provider’s system. It spares the ransomware groups from hacking several entities yet demand ransom from each.
In this scenario, no matter how well the clients protect their systems and networks, their vendor’s systems breach allows hackers to access their data.
ALPHV ransomware group has been targeting organizations globally with triple-extortion techniques to launch cyberattacks.
They steal sensitive data, encrypt the information, seek a ransom, and threaten to leak data. They threaten the targets of launching a DDoS attack if ransom demands are not met.