The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a manufacturing operations management software vulnerability to its Known Exploited Vulnerabilities (KEV) catalog, a rare addition of an industrial control system (ICS)/operational technology (OT) vulnerability to the KEV catalog.
CVE-2025-5086 is a 9.0-rated Deserialization of Untrusted Data vulnerability in DELMIA Apriso, a manufacturing operations management (MOM) and manufacturing execution system (MES) software from Dassault Systèmes that is used to manage production processes and connect factory floors to enterprise resource planning (ERP) systems.
The vulnerability affects DELMIA Apriso from Release 2020 through Release 2025 and could lead to remote code execution (RCE).
DELMIA Apriso CVE-2025-5086 Exploits Detected
The SANS Internet Storm Center (ISC) reported attack attempts targeting the DELMIA Apriso CVE-2025-5086 vulnerability in a September 3 blog post by Johannes Ullrich, ISC founder and Dean of Research for SANS Technology Institute.
The scans detected by SANS appear to originate from the IP 156.244.33[.]162. The exploit uses SOAP requests to the WebServices/FlexNetOperationsService service, embedding a payload encoded in XML that decodes to a GZIP-compressed Windows executable. As of publication time, the payload is undetected by all but one security tool in VirusTotal.
The string “Project Discovery CVE-2025-5086” suggests that the scan may originate from a vulnerability scanner, SANS said. In a note to clients, Cyble reported that the Nuclei scanning script for the vulnerability is available in the public domain.
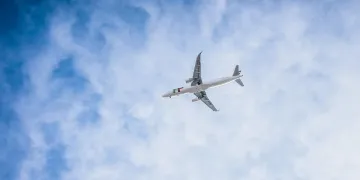
The DELMIA Apriso platform is used by major companies in sectors such as aerospace, automotive, and consumer goods. As Apriso underpins production workflows and supply chain visibility, a successful compromise could disrupt manufacturing processes, making timely patching and mitigation essential.
“When I am thinking about the security of manufacturing environments, I am usually focusing on IoT devices integrated into production lines. All the little sensors and actuators are often very difficult to secure,” Ullrich wrote. “On the other hand, there is also ‘big software’ that is used to manage manufacturing. One example is DELMIA Apriso by Dassault Systèmes. This type of Manufacturing Operation Management (MOM) or Manufacturing Execution System (MES) ties everything together and promises to connect factory floors to ERP systems. But complex systems like this have bugs, too.”
The Dassault security advisory on CVE-2025-5086 includes a link to remediation information.
ICS/OT Vulnerabilities in the KEV Catalog
CISA rarely adds ICS/OT vulnerabilities to the KEV catalog, although IT vulnerabilities in the KEV catalog often appear in ICS/OT products too.
Perhaps the most recent ICS/OT vulnerability added to the KEV catalog before CVE-2025-5086 was CVE-2023-6448, a 9.8-severity Insecure Default Password vulnerability in Unitronics VisiLogic before version 9.9.00, used in Vision and Samba PLCs and HMIs. CISA added the vulnerability to the KEV catalog in December 2023.
CISA has given Federal Civilian Executive Branch (FCEB) agencies a deadline of October 2 to apply updates to protect against CVE-2025-5086, and others affected by the vulnerability are urged to apply fixes too.