A hacktivist group known as ‘Team R70’ has named an Indian government website as one of its victims.
Hailing from Yemen, Team R70 claimed responsibility for defacing the website of the Chhattisgarh State Biodiversity Board. The Chhattisgarh Biodiversity Board cyber attack was not confirmed by the authorities at the time of writing.
Based in central India, the Chhattisgarh State Biodiversity Board focuses on conserving and promoting the state’s rich biodiversity. It implements initiatives to protect diverse flora, fauna, and ecosystems, ensuring sustainable development, conducting biodiversity research, and raising awareness about conservation.
The Cyber Express emailed the Chhattisgarh government and forest department to confirm the Chhattisgarh Biodiversity Board cyber attack. We will update this report based on their response.
Chhattisgarh Biodiversity Board cyber attack by Team R70 hacker group
The hackers from the Team R70 group claimed the Chhattisgarh Biodiversity Board cyber attack as part of the Operation India (OpIndia) campaign.
Team R70 posted about the alleged Chhattisgarh Biodiversity Board defacement attack on their dark web portal.
Previous cyber attacks by Team R70 and collaboration of hacker groups
The Yemeni Team R70 hackers claimed a Swedish taxi service provider in July this year. Threat Intelligence Service Falcon Feeds confirmed that the targeted website was down at the time of reporting the Taxi Priser cyber attack.
Team R70 was also named in reports of pro-Russian hackers targeting Swedish websites. The NoName hacker group claimed that they targeted the website of the Swedish Ministry of Finance in June 2023.
Following this, several groups including Anonymous Sudan, Team R70, UserSec, and more, joined the league of attackers.
“In the days that ensued, a collection of known and lesser-known hacker groups, including Anonymous Sudan, Team 1919, Islamic Hacker Army, Host Kill Crew, US NEXUS HACKER, Mysterious Team Bangladesh, KEP TEAM, UserSec collective, Team Heroxr, Electronic Tigers Unit, Team R70, GANOSEC TEAM, and Turk Hack Team, orchestrated DDoS attacks on a myriad of Swedish websites,” a SOC Radar report read.
Hackers collaborating to launch large-scale cyber attacks
Hackers are collaborating and sharing resources to expand their reach in targeting a greater number of websites.
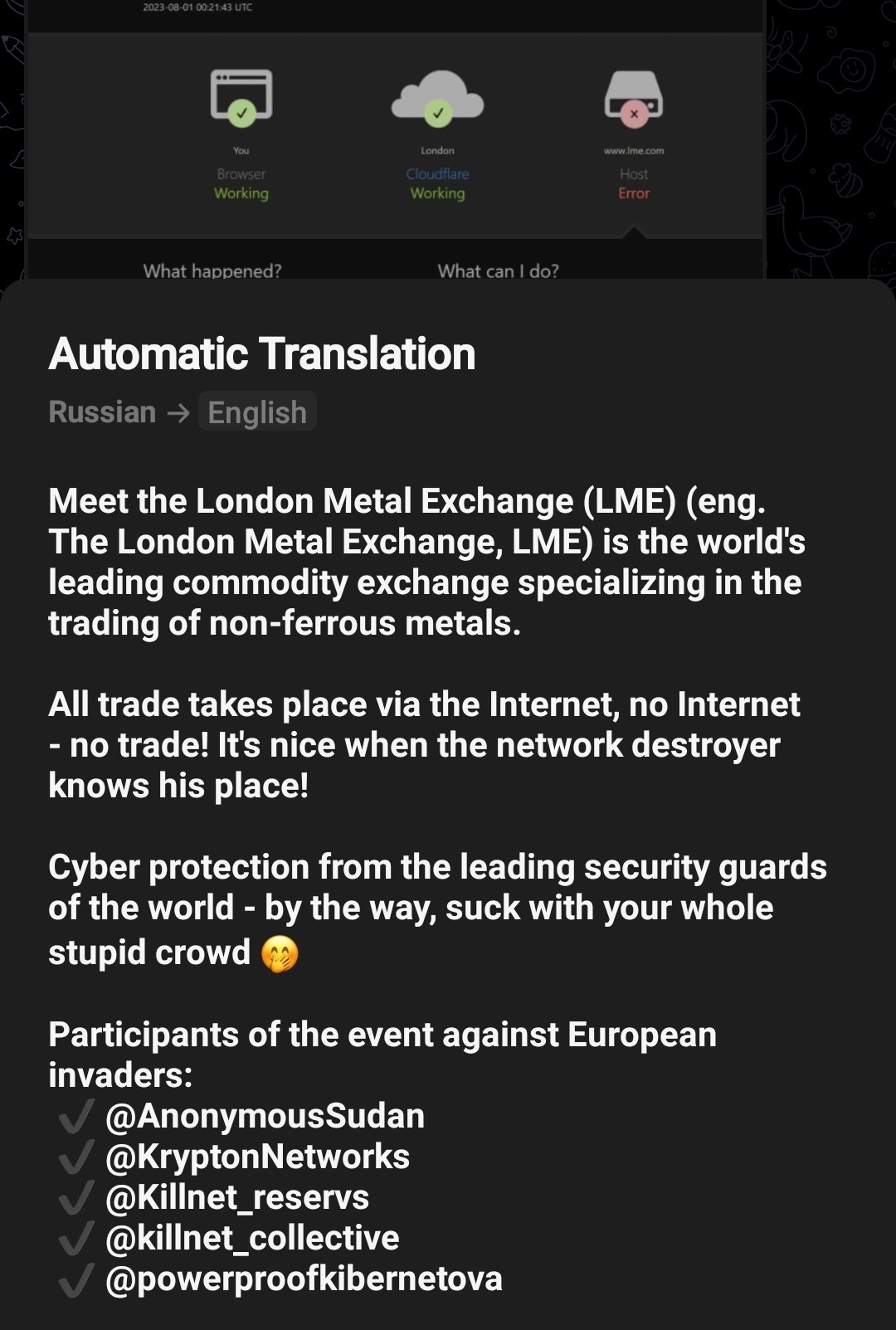
Anonymous Sudan was found sharing its communication platform with the Killnet group. While Killnet claimed that they attacked the London Metal Exchange as part of a joint event.
They were supported by –
- Anonymous Sudan
- KryptonNetworks
- Killnet_reservs
- Killnet_collective
- Powerproofkibernetova
Cybercriminals use their Telegram channel to announce that they will be targeting a specific country as part of an operation like OpIsrael, or OpSweden. They also use the social media to invite new hackers and developers to join them in their fight against nations.
Frequently, hackers engage in conflicts fueled by geopolitical tensions among nations and individuals. Unfortunately, organizations bear the brunt of these hostilities, facing the repercussions in the form of lawsuits and data breaches, often resulting in significant financial losses.
The LockBit ransomware group was recently observed actively seeking developers and testers as they attempted to breach highly secure macOS devices.
These offers, enticing skilled individuals with incentives, serve as alluring bait on the dark web, luring them into the realm of cybercrime. This is regardless of whether they understand the operations and campaigns launched by notorious hacker groups for whom they might work.
Evident in the recent arrest of the two teens linked to the Lapsus$ hacking group, who were presented in court for several counts of fraud and blackmail.























































